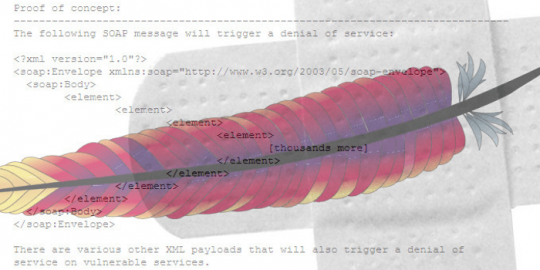
High-Severity RCE Bug Found in Popular Apache Cassandra Database
On the plus side, only instances with non-standard not recommended configurations are vulnerable. On the downside, those configurations aren’t easy to track down, and it’s easy as pie to exploit.