It’s only been a few days since Apple fixed the nasty certificate-validation “goto fail” vulnerability in iOS and OSX and now word comes that another bug, one that could allow an attacker to monitor keystrokes on iOS 7 devices without the user being any the wiser, also exists.
The problem apparently exists on iOS 6.1.x and the following versions iOS 7 versions: 7.0.4, 7.0.5, and 7.0.6.
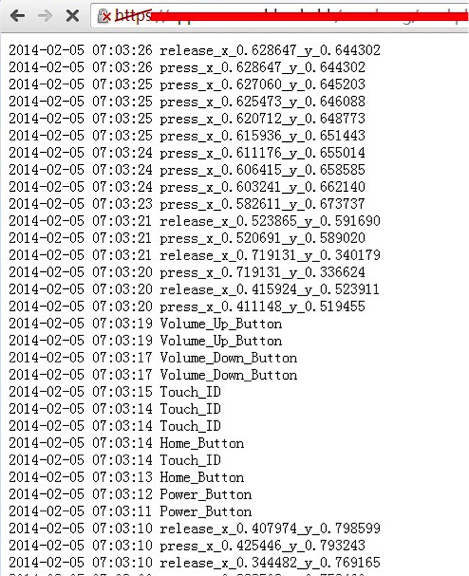
Researchers at FireEye found the problem which could essentially permit someone to keep track of “all the user touch/press events” happening in the background of one’s iPhone or iPad. Some of the details an attacker could glean include knowing whenever a user touches the screen, presses the home button, increases or decreases the volume or uses Touch ID, the fingerprint identity sensor Apple shipped with its latest iPhone 5S device.
The bug relies on bypassing the phone’s “background app refresh,” a resource that the operating system would normally allocate for apps to run in the background. The feature is intended to help users multitask and easily switch between recent apps they’ve used.
The FireEye researchers, Min Zheng, Hui Xue and Tao Wei, were able to exploit the hole by creating a proof-of-concept monitoring app they claim could bypass Apple’s app review process and cause trouble as long as they could get the victim to download the app via phishing. The researchers claim they could also “exploit another remote vulnerability of some app and then monitor in the background.”
While the app can’t tell exactly which keys the victim is pressing, it does provide a list of time-stamped X and Y coordinates that an attacker could later decode to determine which buttons were pressed.
Keyloggers or apps that allow background monitoring for iOS devices are nothing new. Multiple apps can run silently in the background on phones, mining users’ activities. The apps can be purchased, some for a lump sum, some for a subscription fee, through third party merchants. The caveat for those apps is that the device needs to have been jailbroken. In this situation however the FireEye researchers claim that non-jailbroken devices could also be vulnerable.
According to the blog the group wrote Monday for their exploit they used a non-jailbroken iPhone 5S running on version 7.0.4.
The trio claim they’re in the middle of collaborating with Apple on the bug. While a fix is coming, if anyone is truly concerned about being spied on in the meantime, the researchers recommend selectively killing apps running in the background, which users can do by pressing the home button twice and swiping an app up and out of preview to disable unnecessary or suspicious applications.