Yesterday’s shut down of Troyak-as was definitely good news for the whole IT security community. Seeing cybercriminals getting kicked out from the Internet and then trying to get back inside calls for popcorn and soda.
But unfortunately, as some botnets struggle, others stay unaffected: Koobface, for example, which uses compromised legitimate websites as proxies for their main command and control server.
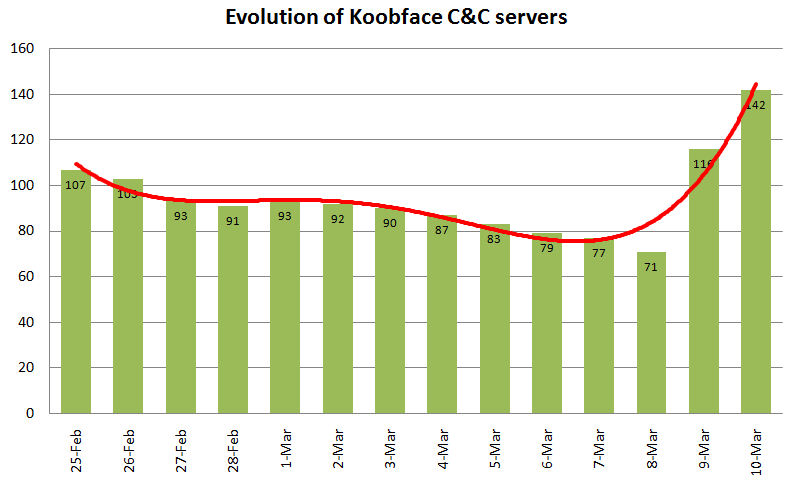
In the past 2 weeks, we’ve seen their live C&C servers getting shut down or cleaned on an average of 3 per day. The number dropped steadily from 107 on February 25 to as low as 71 on March 8.
Then, in just 48 hours, the number has grown from 71 to 142, no more and no less, basically doubling the total number of C&C servers which all the Koobface infected computers can use to get updates and commands (see chart below).
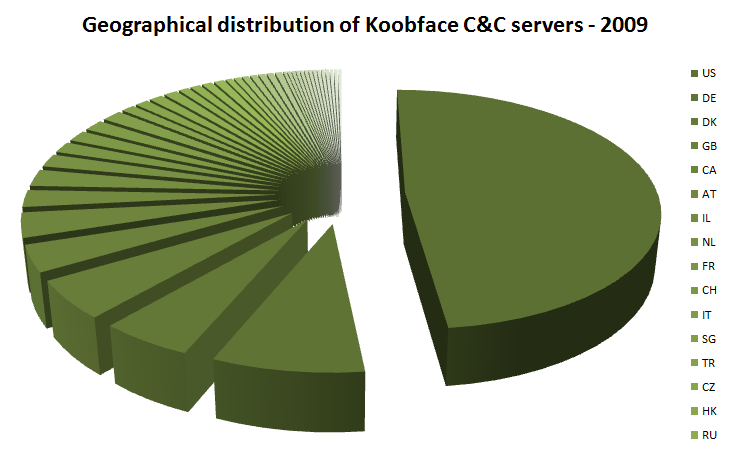
Another interesting thing happening right now to the Koobface command and control infrastructure can be observed when looking at the evolution of the geographical location of IP addresses used to communicate with the infected computers.
The trend that we are seeing is to increase the usage of C&C servers hosted in the United States.
This is how the picture looked at the end of 2009:
And this is how it looks right now, at the beginning of 2010:
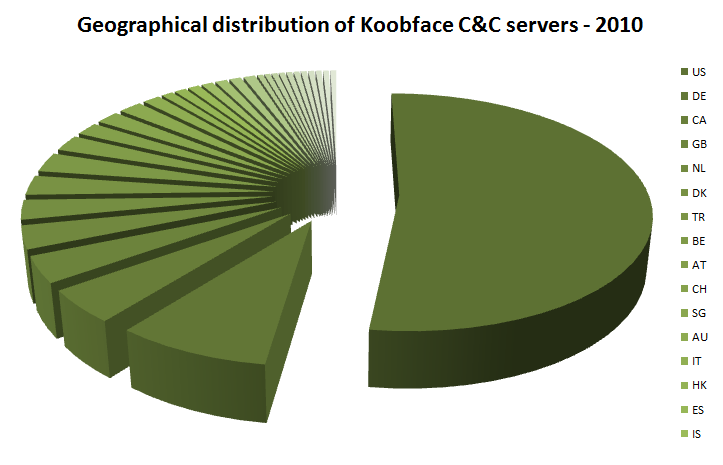
The percentage of Koobface C&C servers hosted in the United States grew from 48.22% to 52.23%. So, right now, more than half of the Koobface C&C servers are hosted in the United States, making the top 10 of countries which host Koobface C&C servers look like this:
- US 52.23%
- DE 8.48%
- CA 4.46%
- GB 3.57%
- NL 3.13%
- DK 2.68%
- TR 2.68%
- BE 2.68%
- AT 2.23%
- CH 1.79%
These latest happenings give us some indications on how the Koobface gang takes care of its infrastructure.
Here are some conclusions:
– First, we can clearly see that they are constantly monitoring their infrastructure status.
– They don’t want the number of their C&C servers to drop too much, as that would mean losing control over the botnet.
– When the number of alive C&C servers drops to a critical level, they seem to be prepared with dozens of new servers.
– The number of total Koobface C&C servers is always oscillating, going from above to below 100 and back in a matter of weeks.
– It seems that 100 online C&C servers is the right number to keep the Koobface gang relaxed.
– Also, they prefer having their C&C servers distributed all over the world, in different countries and different ISPs, to make the take down process harder.
– Still, most of the Koobface C&C servers remain in the United States, where also most of the Koobface infected computers are located: 40% of the IP addresses that connect to Koobface C&C servers are US based.
* Stefan Tanase is a senior security researcher at Kaspersky Lab.









