 Android attacks have become all the rage in the last year or two, and targeted attacks against political activists in Tibet, Iran and other countries also have been bubbling up to the surface more and more often lately. Now those two trends have converged with the discovery of a targeted attack campaign that’s going after Tibetan and Uyghur activists with a spear-phishing message containing a malicious APK file. Researchers say the attack appears to be coming from Chinese sources.
Android attacks have become all the rage in the last year or two, and targeted attacks against political activists in Tibet, Iran and other countries also have been bubbling up to the surface more and more often lately. Now those two trends have converged with the discovery of a targeted attack campaign that’s going after Tibetan and Uyghur activists with a spear-phishing message containing a malicious APK file. Researchers say the attack appears to be coming from Chinese sources.
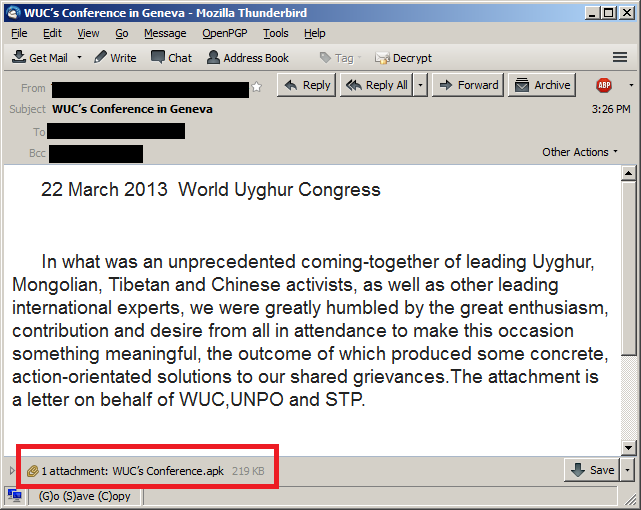
The new campaign began a few days ago when unknown attackers were able to compromise the email account of a well-known Tibetan activist. The attackers then used that account to begin sending a series of spear-phishing messages to other activists in the victim’s contact list. One of the messages referred to a human rights conference in Geneva in March, using the recipients’ legitimate interest in the conference as bait to get them to open the attachment. The malicious attachment in the emails is named “WUC’s Conference.apk”.
Once the victim opens the attachment on her Android phone, the file installs an application called “conference” that will display some information about the Geneva conference. Meanwhile, the malware is running in the background.
“While the victim reads this fake message, the malware secretly reports the infection to a command-and-control server. After that, it begins to harvest information stored on the device,” according to an analysis of the attack by Kaspersky Lab researchers.
“It is important to note that the data won’t be uploaded to C&C server automatically. The Trojan waits for incoming SMS messages (the “alarmReceiver.class”) and checks whether these messages contain one of the following commands: “sms”, “contact”, “location”, “other”. If one these commands is found, then the malware will encode the stolen data with Base64 and upload it to the command and control server.”
The malware looks for a specific set of data, including contacts, call logs, SMS messages, geolocation and phone data. The malware communicates with a command-and-control server at the URL: hxxp://64.78.161.133/*victims’s_cell_phone_number*/process.php. The malware authors apparently have some familiarity with the Tibetan language, as some of the commands use native words. However, there also are a number of Chinese words and commands in the code, as well.
“Throughout the code, the attackers log all important actions, which include various messages in Chinese. This was probably done for debugging purposes, indicating the malware may be an early prototype version,” the Kaspersky analysis says.
Interestingly, the C2 server for the attack is located in Los Angeles and is registered to a companybased in Beijing. While this is one of the first known targeted attack campaigns to utilize Android as a delivery mechanism, it likely won’t be the last.
“Every day, there are hundreds if not thousands of targeted attacks against Tibetan and Uyghur supporters. The vast majority of these target Windows machines through Word documents exploiting known vulnerabilities such as CVE-2012-0158, CVE-2010-3333 and CVE-2009-3129,” the analysis says.
“In this case, the attackers hacked a Tibetan activist’s account and used it to attack Uyghur activists. It indicates perhaps an interesting trend which is exploiting the trust relationships between the two communities. This technique reminds us of a combination between ages old war strategies ‘Divide et impera’ and ‘By way of deception’.”









