Victims of ransomware attacks now face a double whammy of headaches. Cybercriminals are increasingly inflicting more pain on ransomware victims by threatening to leak compromised data or use it in future spam attacks, if ransom demands aren’t met.
The ransomware tactic, call “double extortion,” first emerged in late 2019 by Maze operators – but has been rapidly adopted over the past few months by various cybercriminals behind the Clop, DoppelPaymer and Sodinokibi ransomware families.
“Double Extortion is a clear and growing ransomware attack trend,” Lotem Finkelsteen, manager of threat intelligence with Check Point Research, said in a Thursday analysis. “We saw a lot of this in Q1 of 2020. In this tactic, threat actors corner their victims even further by dripping sensitive information into the darkest places in the web to substantiate their ransom demands.”
A November 2019 ransomware attack against Allied Universal, a large American security staffing company, set the precedent for “double extortion.” After the company was hit by a Maze ransomware attack, and refused to cough up the 300 Bitcoin ($2.3 million) ransom, the attackers threatened to use sensitive information extracted from Allied Universal’s systems, as well as stolen email and domain name certificates, for a spam campaign impersonating Allied Universal.
To prove the validity of the threat, the threat actors leaked 700 MB worth of data (only 10 percent of what the crooks claimed to have stolen) including contracts, medical records, encryption certificates and more – and published a new ransom demand that was 50 percent higher than the original.
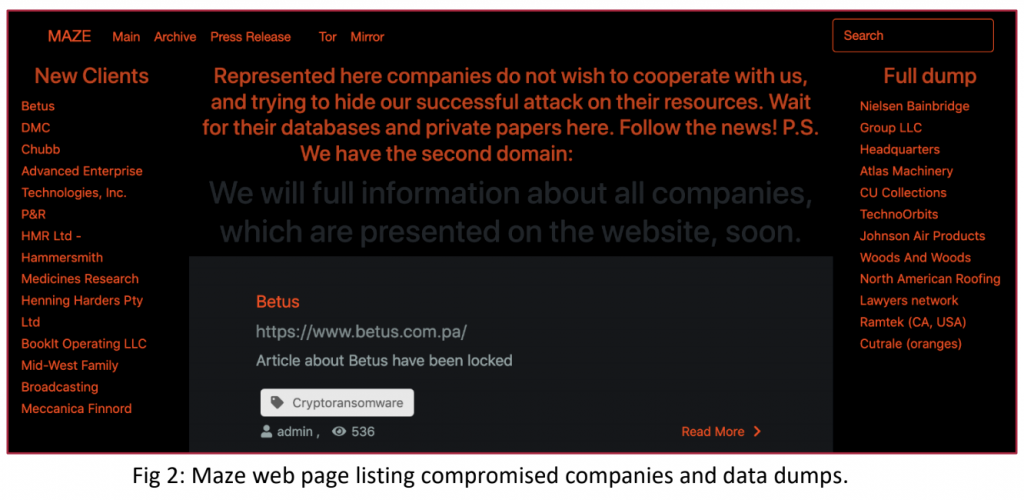
Now, researchers say that, TA2101, the group behind the Maze ransomware, have since created a dedicated web page which lists the identities of their non-cooperative victims and regularly publishes samples of the stolen data.
“Maze has since published the details of dozens of companies, law firms, medical service providers and insurance companies who have not given in to their demands. It is estimated that many other companies avoided publication of their sensitive data by paying the ransom demanded,” said Finkelsteen.
Since this incident, Finkelsteen said other cybercriminal groups behind the Clop, Nemty (before the ransomware operation shut down this week), DoppelPaymer and the Sodinokibi ransomware have copied these efforts, opening their own sites to publish or leak stolen data in an effort to place additional pressure on the ransomware victims to pay up.
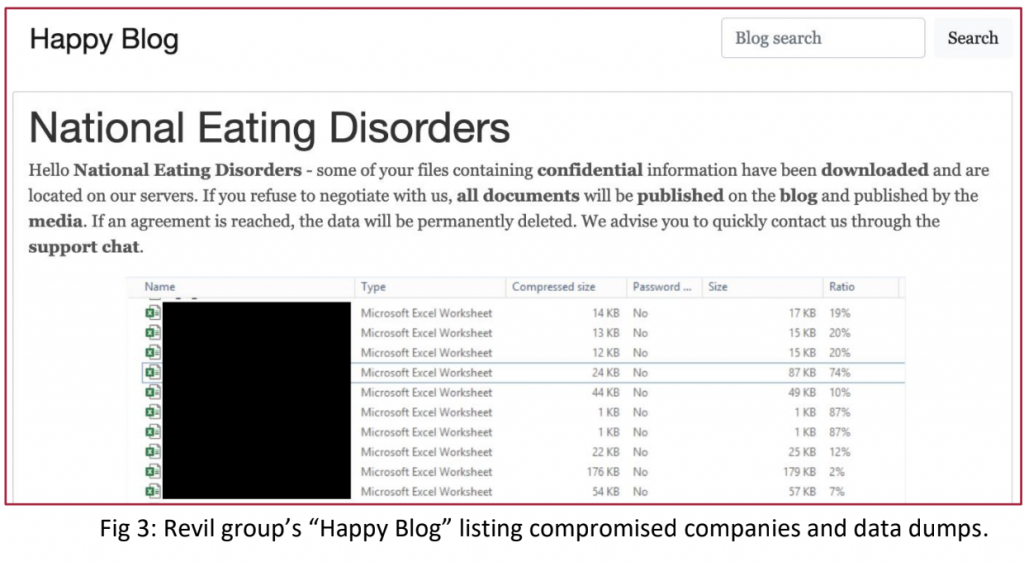
For instance, attackers using the Sodinokibi ransomware (also known as REvil) have created a “Happy Blog” where they have recently published details of ransomware attacks on 13 targets, as well as company information stolen from the targeted organizations. That includes files of the National Eating Disorders Association, an organization that aids people with eating disorder, which was first infected by ransomware earlier in April (and data for which was leaked by the ransomware attackers on April 4). Threatpost has reached out to the National Eating Disorders Association for further comment.
Similarly, the operators behind the Sodinokibi ransomware threatened to sell an entire database compromised from global currency exchange Travelex after a malware attack at the new year knocked the company offline and crippled its business during the month of January (Travelex ended up paying out $2.3 million in Bitcoin).
Researchers said that ransomware attackers will first publish screenshots of the information only, to serve as a warning for victims that they need to pay their ransom on time. If the payment is not made in time, the attackers follow through on their threat and make the confidential files available on the web for public download.
“This puts targeted organizations in a double-jeopardy trap: if they don’t give in to the attacker’s demands, the attackers will publish stolen data and the organization will have to report the breach to the relevant national or international data privacy watchdog – which could in turn levy a large fine on the organization,” said Finkelsteen. “Either way, the organization is likely to have to pay to move forward.”
Hospitals
Research experts warn that “double extortion” attacks will continue to hit ransomware victims in 2020 – particularly with more hospitals, which not only collect sensitive, health-related data, but are also currently on the front lines of the coronavirus pandemic being targeted with cyberattacks.
Despite ransomware gangs recently pledging that they would stop attacking hospitals in the midst of the pandemic, cyberattacks continue. Several hospitals have been targeted by the Ryuk ransomware, according to security researcher “PeterM” on Twitter. Hammersmith Medicines Research, a London-based healthcare provider that was working with the British government to test COVID-19 vaccines, was also recently hit by a ransomware attack. The Maze ransomware operators, which launched the attack, later posted the stolen data online.
“We’re especially worried about hospitals having to face this threat,” said researchers. “With their focus on coronavirus patients, addressing a double extortion ransomware attack would be very difficult. We issue caution to hospitals and large organization, surging them to back up their data and educate their staff.”
Researchers say that companies can protect themselves by following many of the best practices that initially prevent ransomware attacks – including backing up their data and files, educating employees, keeping signature based protections up to date and implementing multi layered security protections.
Worried about your cloud security in the work-from-home era? On April 23 at 2 p.m. ET, join DivvyCloud and Threatpost for a FREE webinar, A Practical Guide to Securing the Cloud in the Face of Crisis. Get exclusive research insights and critical, advanced takeaways on how to avoid cloud disruption and chaos in the face of COVID-19 – and during all times of crisis. Please register here for this sponsored webinar.