Hamas has been caught taking a classic “catfish” approach, to tempt Israeli soldiers into installing spyware on their phones. Members posed as teen girls who are looking for quality chat time.
This is the third time that the Palestinian group has used the tactic – but this time it upped its technical game.
According to the Israel Defense Forces (IDF), the Palestinian group took to Facebook, Instagram and Telegram under the guise of six social media personae: Sarah Orlova, Maria Jacobova, Eden Ben Ezra, Noa Danon, Yael Azoulay and Rebecca Aboxis. The IDF tweeted out a short notice on the campaign, which it said it disrupted:
Hamas created fake social media profiles, using photos including this one, in an attempt to hack the phones of IDF soldiers.
What Hamas didn’t know was that Israeli intelligence caught onto their plot, tracked the malware & downed Hamas’ hacking system.#CatfishCaught
— Israel Defense Forces (@IDF) February 16, 2020
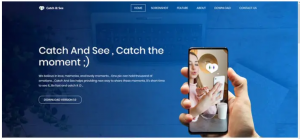
The IDF told the Times of Israel that the idea was to catch male targets’ attention, strike up a rapport and eventually lure the soldiers into installing a special app on their phones. The apps purported to allow private chatting where posts disappear after a time, a la Snapchat. The apps were called Catch & See, ZatuApp and GrixyApp.
The ‘ladies’ claimed to be immigrants to Israel with a “lack of full command of the Hebrew language,” and with vision and hearing problems (in an effort to explain away spelling and grammatical errors).
The IDF said that the characters had multiple profiles on different platforms, and accounts used stolen images from legitimate pages to add verisimilitude to the proceedings. However, the photographs had been edited and altered in order to thwart Google image lookups and other efforts to find their original source.
Prior to installation, the application would ask for various permissions to access location, camera, microphone and so on, which the victim would need to allow. After install, the app would show up as an icon; but, if a soldier clicked on it, he would get an error message saying that the app wasn’t compatible with the device. After that, it would seemingly “disappear.”
“The apps, which were not available in official app stores, would appear to fail with an error message after installation – but in reality install malware on behalf of Hamas to take remote control of an infected smartphone,” security researcher Graham Cluley said in an analysis this week. “Once in place, the malware could take remote photographs, access files, steal SMS messages and address books, and share the device’s GPS location.”
The IDF told the Jerusalem Post that this campaign was more sophisticated in its efforts than previous efforts, both in its tampering of the stolen images as well as the spyware’s capabilities: This time, the malware was able to download and transfer files, and provided access to the phone’s location for the first time, according to the report.
The IDF said that no officers fell for the trick, and that the information gleaned from the victims (whose numbers were in the “low hundreds,” according to the Times of Israel source) was of little tactical value.
Hamas has tried catfishing twice before. In 2017, soldiers were targeted by Facebook friend requests from various “ladies,” expressing their interest, along with photos cribbed from other, legitimate Facebook profiles. After chatting enough to convince the soldier that she’s real, the person on the other end asked the soldier to video chat.
“But all the [existing video] apps he has won’t work for her—she needs him to download another one,” the IDF described in a blog at the time. “She sends him a link to an app [in a third-party app] store called ‘apkpk.’ He downloads the app she requested. The app isn’t working, not for the soldier, at least. He tries to tell the pretty girl on the other end, but she won’t respond.”
Then, in 2018, the militant group was back, this time using WhatsApp as the attack vector. In that case, the catfishers sent victims a link to download a purported “dating app,” dubbed GlanceLove, or, oddly, a fake World Cup fan app called Golden Cup.
The U.S. military has also been targeted with similar tactics. In 2018, prisoners in South Carolina formed a sextortion ring that bilked 442 service members from the Army, Navy, Air Force and Marine Corps out of more than $560,000. The inmates and their outside civilian associates identified and targeted members of the military via social media forums and online dating websites. Then, posing as attractive females, they exchanged pictures and lured service members into online romances. The prisoners would then assume a role of the female’s father, who claimed the female was a juvenile, and ask for payment in exchange for not pursuing charges through law-enforcement channels.
Learn how Operational Technology and Information Technology systems are merging and changing security playbooks in this free Threatpost Webinar. Join us Wednesday, Feb. 19 at 2 p.m. ET when a panel of OT and IT security experts will discuss how this growing trend is shaping security approaches for IoT and 5G rollouts. This webinar is for security and DevOps engineers, IoT edge developers and security executives.