For the second time in ten days, researchers at UpGuard released sensitive data belonging to the United States Defense Department that was stored insecurely online. This time it was nearly 100 GB of critical data belonging to the United States Army Intelligence and Security Command (INSCOM).
Some of data included information labeled “top secret” and “NOFORN” (no foreign nationals) and mostly pertained to a project called Red Disk, a proposed plan to offer cloud-computing capabilities to a U.S. military intelligence network known as the Distributed Common Ground System (DCGS).
“INSCOM’s web presence provides troubling indications of gaps in their cybersecurity – exemplified by the presence of classified data within this publicly accessible data repository,” wrote UpGuard in a report outlining its findings on Tuesday.
The data was found on an Amazon S3 storage bucket publicly accessible to the internet. According to UpGuard, the AWS storage bucket belonged to a now-defunct third-party defense contractor named Invertix, a past INSCOM partner.
Requests for comment made to INSCOM were not returned. The NSA an U.S. Army referred all questions on the matter to INSCOM. INSCOM is an intelligence command overseen by both the U.S. Army and the NSA.
The data leak follows a number of previous embarrassing leaks for the Defense Department where sensitive data was also left on publicly accessible servers. Last week, UpGuard reported it found a massive archive of 1.8 billion publicly accessible social-media posts on the Amazon S3 storage buckets that belonged to a Pentagon contractor.
UpGuard Director of Cyber Risk Research, Chris Vickery, is credited for finding both leaky servers. According to the UpGuard, the INSCOM data was found on Sept. 27, 2017 on an AWS storage bucket configured for public access.
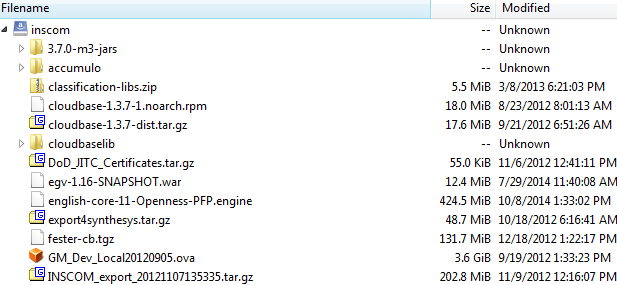
“Set to allow anyone entering the URL to see the exposed bucket’s contents, the repository, located at the AWS subdomain ‘inscom,’ contained 47 viewable files and folders in the main repository, three of which were also downloadable,” UpGuard reported Tuesday. UpGuard said that three of the downloadable files contained “highly sensitive” data that was explicitly classified.
Aside from information about Red Disk, a virtual hard drive and Linux-based operating system was also publicly accessible. The hard drive contains six partitions, varying in size from 1 GB to 69 GB.
“
“While the virtual OS and HD can be browsed in their functional states, most of the data cannot be accessed without connecting to Pentagon systems – an intrusion that malicious actors could have attempted, had they found this bucket,” researchers noted.
Also exposed were private keys used for accessing distributed intelligence systems, belonging to Invertix administrators, as well as hashed passwords which, if still valid and cracked, could be used to further access internal government systems.
Just how sensitive is the data exposed is unclear.
“It is unnecessary to speculate as to the potential value of such an exposed bucket to foreign intelligence services or malicious individual actors; the care taken to classify sections of the exposed virtual drive as ‘Top Secret’ and ‘NOFORN’ provide all the indications necessary to determine how seriously this data was taken by the Defense Department,” UpGuard wrote.
The leak is just the latest in a long string of incidents where data has been exposed to the public internet via misconfigured servers. As of September 2017, IBM X-Force said 1.3 billion records tied to 24 incidents have been exposed. Accenture, Verizon, Dow Jones and Deep Root Analytics are just a few of the firms in the past year when it comes to the millions of private records and sensitive enterprise data exposed on cloud backends this year.
UpGuard said it worked with INSCOM to remove and secure the data.