More than half of people haven’t changed their password in the last year – even after they’ve heard about a data breach in the news.
That’s according to a recent survey, “Psychology of Passwords: The Online Behavior That’s Putting You At Risk,” that examined the online security and password behaviors of 3,250 global respondents – and found that people still employ an alarming number of very common and very risky habits, even though they know better.
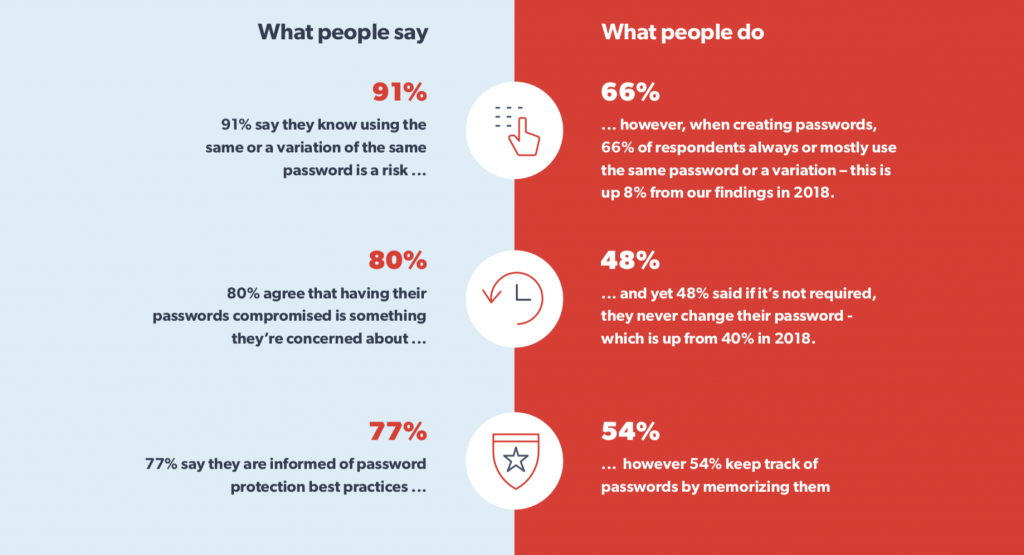
Researchers said that password reuse was the biggest security faux pas being committed by respondents. In fact, password reuse has actually gotten worse over the years: When asked how frequently they use the same password or a variation, 66 percent answered “always” or “mostly” – which is up 8 percent from the same survey in 2018.
Worse, 91 percent of respondents said they know using the same (or a variation of the same) password is a risk. They still do so anyways.
“Our survey shows that most people believe they are knowledgeable about the risks of poor password security; however, they are not using that knowledge to protect themselves from cyber threats,” said researchers with LastPass by LogMeIn, in a recent report.
In the wake of the COVID-19 health crisis, in which people find themselves working from home and spending time online more than ever due to global orders to stay at home, protecting personal data when using the internet is more crucial than ever, researchers said. However, people still seem to underestimate how much of that data is stored online and don’t take the necessary precautions to keep it safe from cybercriminals. These bad actors, coincidentally, have ramped up their threat behavior to take advantage of people’s new dependence on conducting business and personal activities online.
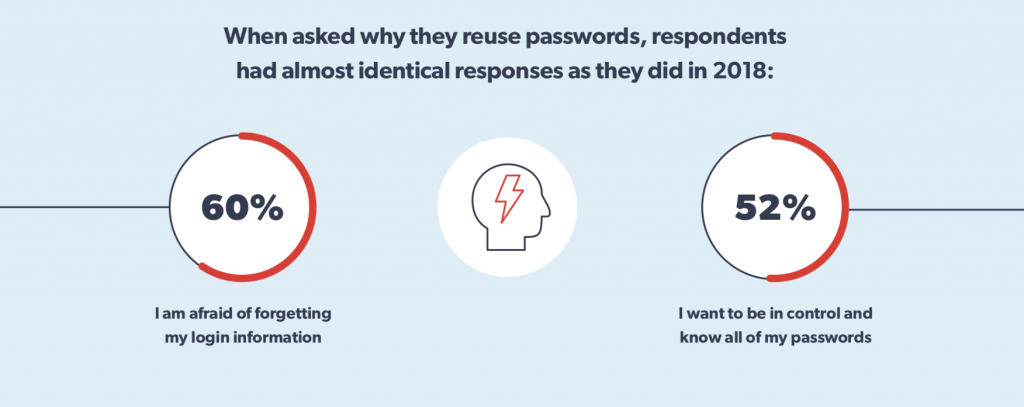
With breaches being disclosed daily – affecting large, popular brands like Macy’s and Marriott – why would consumers continue to reuse passwords? One reason is that people underestimate how valuable their information is, researchers explain. In fact, 42 percent of respondents said they think their accounts aren’t valuable enough to be worth a hacker’s time. When asked further about why they reuse passwords, 60 percent of users said they are afraid of forgetting their login information, while 52 percent said they want to “be in control” and know all of their passwords.
“People seem to be numb to the threats that weak passwords pose,” said researchers. “Technology like biometrics is making it easier for them to avoid text passwords all together and many people are simply comfortable using the ‘forgot password’ link whenever they get locked out of their accounts.”
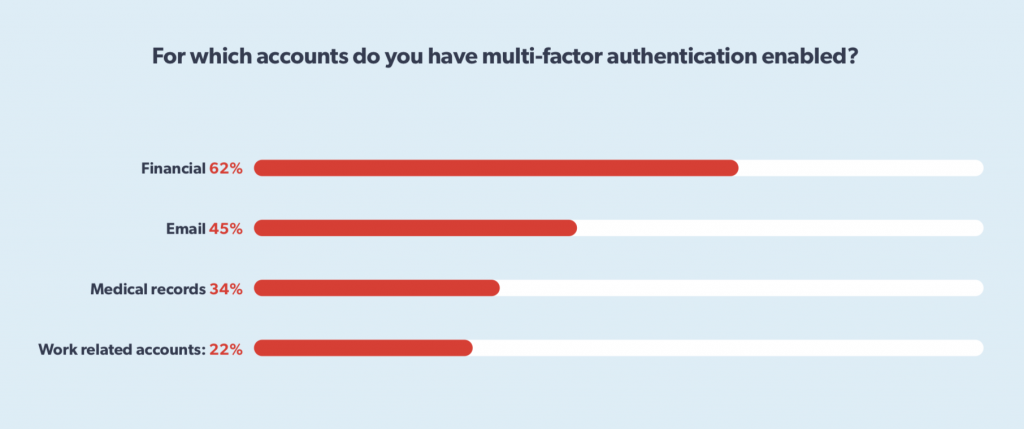
When it does come to security, the majority of respondents are prioritizing their financial accounts over their email, medical records and work-related accounts. For instance, 69 percent of respondents said they would create stronger passwords for their financial accounts, and 62 percent said that they have multi-factor authentication (MFA) enabled for their financial accounts. On the flip side, only 29 percent said they would create a stronger password for work-related accounts, and 22 percent said they have MFA enabled for work-related accounts.
The big “password problem” has plagued the security industry for years. Poor password hygiene, including reusing passwords or picking easy-to-guess passwords, is greatly exacerbating many of the major issues that plague the cybersecurity landscape, security experts like Troy Hunt have said in the past. Making matters worse, passwords are appearing left and right online as part of major data breaches – yet victims aren’t changing their passwords at all across various platforms. The Collection #1 data dump, which included 773 million credentials, and subsequent Collection #2-5 dumps, show exactly how many passwords are available on the Dark Web and underground forums.
“Respondents are protecting their work accounts at a lower rate than their personal,” said researchers. “We can see that security behaviors are flawed for personal data, and these bad habits extend into your business.”
Elizabeth Montalbano contributed to this article.
Concerned about the IoT security challenges businesses face as more connected devices run our enterprises, drive our manufacturing lines, track and deliver healthcare to patients, and more? On June 3 at 2 p.m. ET, join renowned security technologist Bruce Schneier, Armis CISO Curtis Simpson and Threatpost for a FREE webinar, Taming the Unmanaged and IoT Device Tsunami. Get exclusive insights on how to manage this new and growing attack surface. Please register here for this sponsored webinar.