This article originally appeared on InformIT.com as part of Gary McGraw’s Software [In]Security series.
 Using the Software Security Framework (SSF) introduced in October, we interviewed nine executives running top software security programs in order to gather real data from real programs.Our goal is to create the Building Security In Maturity Model (BSIMM) based on these data, and we’re busy going over what we’ve built with the executives who run the nine initiatives (stay tuned here for more).
Using the Software Security Framework (SSF) introduced in October, we interviewed nine executives running top software security programs in order to gather real data from real programs.Our goal is to create the Building Security In Maturity Model (BSIMM) based on these data, and we’re busy going over what we’ve built with the executives who run the nine initiatives (stay tuned here for more).
Nine Top Software Security Programs
Of the twenty-four large-scale software security initiatives we are aware of, we chose nine that we considered the most advanced. Our nine organizations are drawn from three verticals: financial services (4), independent software vendors (3), and technology firms (2). You can find some data about the organizations we study here.
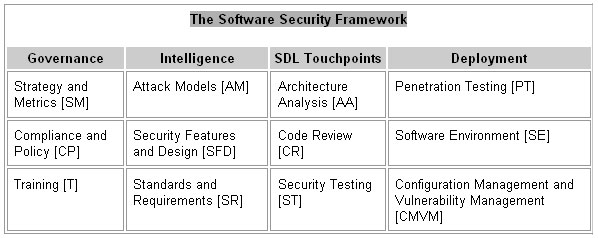
To refresh your memory, the table below shows the SSF. There are twelve practices organized into four domains. There are three practices under each domain. Note that the BSIMM describes objectives and activities for each practice.
Our construction process was driven top down by the SSF and bottom up by the raw interview data. Each of the three investigators collected raw interview data independently during the nine interviews. All three investigators were present for each interview. Step one was for each investigator to create twelve “bullet lists” for each of the nine organizations, one bullet list for each SSF practice. There is no canonical length for the bullet lists, which are meant to abstract the activities noted during the interviews under each practice. We carefully cross-checked each bullet list against raw interview data and brought our independently-created bullet lists into alignment.
Step two was to unify the bullet lists into “buckets.” Once again the goal was to abstract from the current data and to fuse the lists of activities into one list for each practice. During the merging process, we tracked the number of times that an activity showed up in all nine organizations. For example, under the Strategy and Metrics practice one of the items on the bucket list was “started with process, evolved over time and widely used” which we observed in four of the nine organizations.
Step three involved building a preliminary set of levels, one for each practice from the bucket lists. Once again, each investigator performed this step independently and we merged our results (often going back and checking against raw data, buckets, and bullet lists). The final product of step three what we call the BSIMM skeleton.
The BSIMM skeleton covers 110 activities, each paired directly with an objective. Activities are sorted into the 12 practices of the SSF. For example, the Strategy and Metrics practice includes eleven activities. The activities in each practice are ranked into three maturity levels. Our approach is to identify goals for each level of a practice, which can be further split into objectives for the practice/level and are in this way associated with activities. This helps with business-level decisionmaking around a software security initiative. We will release the entire BSIMM model which includes an explanation of all 110 activities in early March 2009.
Nine Things Everybody Does
Of the 110 possible activities, there are nine activities carried out by all of the nine programs we studied. Though we can’t directly conclude that these nine activities are necessary for all software security initiatives, we can say with confidence that these activities are commonly found in highly successful programs. This suggests that if you are working on an initiative of your own, you should carefully consider these nine activities (not to mention the other 101).
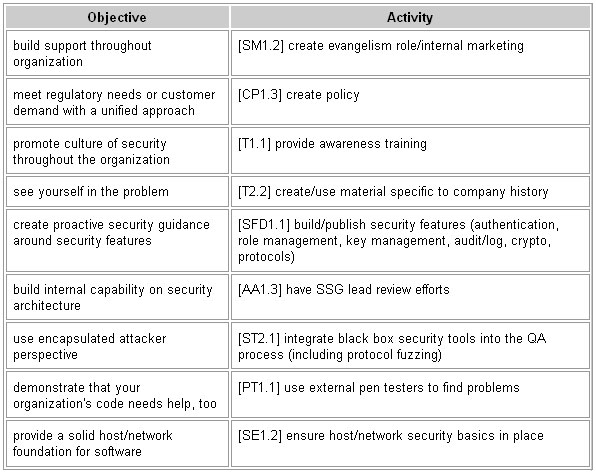
Without further ado, the nine activities that nine successful real software security initiatives carry out. We include the BSIMM “tag” for each activity in the heading.
[SM1.2] Evangelism
In order to build support for software security throughout the organization, the Software Security Group (SSG) plays an evangelism role (as opposed to an audit role). This internal marketing function helps the organization understand the magnitude of the software security problem and the elements of its solution. The SSG might give talks for internal groups, extend invitations to outside speakers, author white papers for internal consumption, or create a collection of papers and other resources on an internal Web site.
[CP1.3] Policy
The SSG acts as a focal point for addressing regulatory requirements and customer-driven security requirements. The SSG guides the rest of the organization by creating policy. The policy provides a unified approach for satisfying the (potentially lengthy) list of external security drivers. As a result, project teams can avoid learning the details involved in regulations or suggested by compliance bodies such as SOX, PCI DSS, HIPPA or FFIEC. Likewise, project teams don’t need to re-learn customer security requirements on their own. The SSG policy documents are sometimes focused around major compliance topics such as the handling of personally identifiable information or the use of cryptography.
[T1.1] Awareness Training
The SSG provides awareness training in order to promote a culture of security throughout the organization. Training might be delivered by members of the SSG, by an outside firm, by the internal training organization, or through a computer-based training system. Course content is not necessarily tailored for a specific audience. For example, all programmers, quality assurance engineers, and project managers could attend the same Introduction to Software Security course.
[T2.2] Company History in Training
In order to make a strong and lasting change in behavior, training includes material specific to the company’s history. When participants can see themselves in the problem, they are more likely to understand how the material is relevant to their work and to know when and how to apply what they have learned. One way to do this is to use noteworthy attacks on the company as examples in the training curriculum.
[SFD1.1] Security Features
Some problems are best solved only once. Rather than have each project team implement all of their own security features, the SSG provides proactive guidance by building and publishing security features for other groups to use. Project teams benefit from implementations that come pre-approved by the SSG, and the SSG benefits by not having to repeatedly track down the kinds of subtle errors that creep into features such as authentication, role management, audit/logging, key management, and cryptography.
[AA1.3] Architecture Analysis by SSG
The SSG takes a lead role in performing architecture analysis in order to begin building the organization’s ability to find design flaws. Architecture analysis is enough of an art that the SSG needs to be proficient at it before they can turn the job over to the architects. The SSG cannot be successful on its own either — they will likely need help from the architects or implementers in order to understand the design. With a clear design in hand, the SSG might carry out the analysis with a minimum of interaction with the project team.
[ST2.1] Black Box Tools
The organization uses one or more black box security testing tools as part of the quality assurance process. The tools are valuable because they encapsulate an attacker’s perspective, albeit in a generic fashion. Tools such as IBM/Rational AppScan or HP WebInspect are relevant for Web applications, and fuzzing frameworks such as PROTOS are applicable for most network protocols. In some situations other groups might collaborate with the SSG to apply the tools. For example, a testing team could run the tool but come to the SSG for help interpreting the results.
[PT1.1] External Penetration Testing
Many organizations are not willing to address software security until there is unmistakable evidence that the organization is not somehow magically immune to the problem. If security has not been a priority, external penetration testers will demonstrate that the organization’s code needs help. Penetration testers could be brought in to break a high-profile application in order to make the point.
[SE1.2] Good Host and Network Security
The organization provides a solid foundation for software by ensuring that host and network security basics are in place. It is common for operations security teams to be responsible for duties such as patching operating systems and maintaining firewalls. Tackling software security without covering the network security basics is foolhardy.
Here is how the nine activities are presented in the BSIMM skeleton (complete with objectives and activity tags). Remember, there are 110 activities in BSIMM and here we’ve covered only nine activities that everybody does.
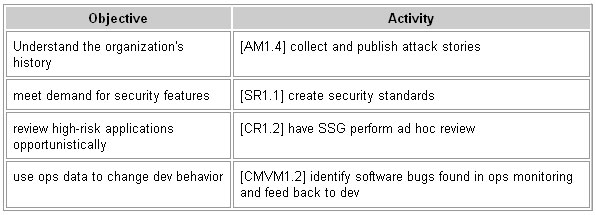
The problem with this list of nine core activities is that four of the twelve practices in the SSF have no representative activities in the list above. That’s the way the cookie crumbles. Turns out there are no activities that everyone does in the four practices in question (Attack Models, Standards and Requirements, Code Review, and Configuration Management and Vulnerability Management).
What we can do to attain complete coverage of practices in the SSF is identify those activities that are the most commonly observed in our data, one for each of the four practices. By combining the four activities below with the nine above, we can identify a core set of 13 activities covering the SSF. Here are the four activities that complete the core:
The next step in our process is to go over the complete BSIMM with the nine companies we worked with and work out any kinks. As soon as that process is complete, we’ll be ready to release the BSIMM to the public.
This article originally appeared on InformIT.com as part of Gary McGraw’s Software [In]Security series.
*Gary McGraw is the CTO of Cigital, Inc., a software security and quality consulting firm with headquarters in the Washington, D.C. area. He is a globally recognized authority on software security and the author of eight best selling books on this topic. His titles include Java Security, Building Secure Software, Exploiting Software, Software Security, and Exploiting Online Games; and he is editor of the Addison-Wesley Software Security series.








