Google has awarded its inaugural annual top prize for the Google Cloud Platform (GCP), for vulnerabilities found in the Google Cloud Shell. The find — a container escape that leads to host root access and the ability to use privileged containers — has earned $100,000 for Dutch researcher Wouter ter Maat.
The internet giant also announced that it would be expanding the scope of payouts for annual GCP prizes, as part of the Google Vulnerability Reward Program (VRP). It will offer six prizes in total for the top vulnerability reports in GCP products submitted in 2020, for a collective $313,337 in winnings. Prizes will start at $1,000 for sixth place and top out at $133,337 for first.
Thanks a 100.000 times to Google and the @GoogleVRP team!! 🙂 Not only for the (amazing) GCP prize, but for all the fun events and opportunities that you provide. Hope to see you all again soon.https://t.co/NtYTnEntjA
— wtm@offensi.com (@wtm_offensi) March 11, 2020
Bug-hunters will need to provide a public write-up in order to be eligible; and, interestingly, that write-up cannot be more than 31,337 words. Google also noted in a posting this week that a free tier of GCP is available for those researchers with budget constraints.
Winning Entry
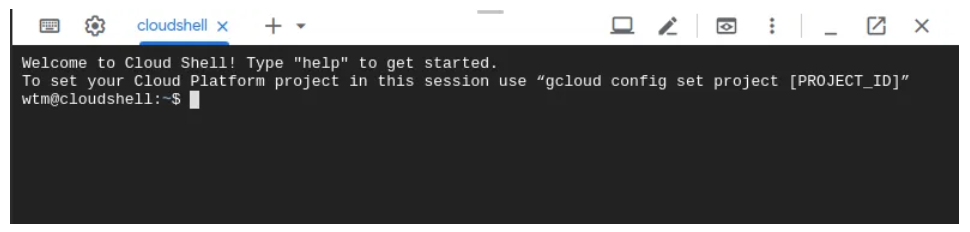
The Google Cloud Shell is a Linux- and browser-based front-end for administrators that provides access to various resources in the Google Cloud Platform. Those can include gcloud, Docker, Kubernetes, Python, vim, Emacs, Theia and others. Users of the Google Cloud Platform can launch a Cloud Shell instance via the Google Cloud Console:
Ter Maat noted that several issues exist in how Cloud Shell interacts with resources, starting with an authentication problem. The end result is the ability to gain root access on the host with the power to reconfigure any containers housed there.
“When the Cloud Shell instance is done starting a terminal window is presented to the user,” ter Maat wrote in his write-up, first published in December. “Noteworthy is the fact that the gcloud client is already authenticated. If an attacker is able to compromise your Cloud Shell, it can access all your GCP resources.”
After launching a Cloud Shell, the researcher was able to connect to resources, determining that he was “trapped inside a Docker container” because there were only a small number of processes running. He was then able to escape the container and access the full host by examining the file system.
“I noticed that there were two Docker UNIX sockets available,” explained ter Maat. “One in ‘/run/docker.sock’, which is the default path for our Docker client running inside the Cloud Shell (Docker inside Docker); the second one in ‘/google/host/var/run/docker.sock.'”
This second socket was revealed to be a host-based Docker socket, as indicated by its pathname.
“Anyone who can communicate with a host-based Docker socket can easily escape the container and gain root access on the host at the same time,” the researcher noted, adding that he wrote a quick script to do just that.
After that, with root access, he was also able to reconfigure Kubernetes to flip all of the containers from unprivileged to privileged by writing a new “cs-6000.yaml” configuration file and setting the old config file to “/dev/null.”
“After running it you will find that all containers inside the pod will automatically reboot. Now all containers run in privileged mode,” said ter Maat.
The cybersecurity implications of gaining malicious control over privileged containers are myriad, according to research firm Trend Micro.
“Running a container with privileged flag allows internal teams to have critical access to the host’s resources — but by abusing a privileged container, cybercriminals can gain access to them as well,” according to an advisory late last year. “For malicious actors who gain access to exposed privileged containers, the possibilities for abuse are seemingly endless. Attackers can identify software running on the host to find and exploit vulnerabilities. They can also exploit container software vulnerabilities or misconfigurations, such as containers with weak credentials or no authentication. Because an attacker has root access, malicious code or coin miners can be executed and effectively hidden.”
Interested in security for the Internet of Things and how 5G will change things? Join our free Threatpost webinar, “5G, the Olympics and Next-Gen Security Challenges,” as our panel discusses what use cases to expect in 2020 (the Olympics will be a first test), why 5G security risks are different, the role of AI in defense and how enterprises can manage their risk. Register here.