Adobe Systems is stomping out 17 critical vulnerabilities in Acrobat Reader, Photoshop and Brackets, which could lead to arbitrary code execution if exploited.
Overall, Adobe released patches – as part of its regularly-scheduled updates – addressing 25 CVEs across various products, including its Acrobat Reader PDF viewer; Photoshop editing tool; ColdFusion 2018 commercial rapid web-application development platform; and Brackets, its source-code editor primarily focused on web development. No exploits for these vulnerabilities have been detected in the wild thus far, said Adobe.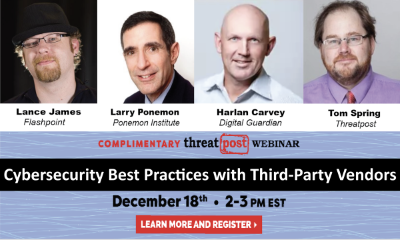
In Adobe Acrobat and Reader, Adobe fixed 14 critical arbitrary code execution flaws, including out-of-bounds write glitches (CVE-2019-16450, CVE-2019-16454), use after free flaws (CVE-2019-16445, CVE-2019-16448, CVE-2019-16452, CVE-2019-16459, CVE-2019-16464), untrusted pointer dereference vulnerability (CVE-2019-16446, CVE-2019-16455, CVE-2019-16460, CVE-2019-16463), a heap overflow (CVE-2019-16451), buffer error (CVE-2019-16462) and a security bypass (CVE-2019-16453).
Adobe also fixed seven “important”-rated flaws in Acrobat Reader. Users are encouraged to update to Acrobat DC and Acrobat Reader DC Continuous versions 2019.021.20058 (for Windows and MacOS); Acrobat and Acrobat Reader Classic 2017 version 2017.011.30156 (for Windows and MacOS) and Acrobat and Acrobat Reader Classic 2015 version 2015.006.30508 (for Windows and MacOS).
The update is a Priority 2, which according to Adobe “resolves vulnerabilities in a product that has historically been at elevated risk. There are currently no known exploits. Based on previous experience, we do not anticipate exploits are imminent. As a best practice, Adobe recommends administrators install the update soon (for example, within 30 days).”
Various researchers from Google Project Zero, Cisco Talos, Tencent Security Xuanwu Lab and more were credited with discovering the flaws (a full list can be found here).
Critical flaws were also reported in Adobe Photoshop CC versions 20.0.7 and earlier (an update is available in 20.0.8) and 21.0.1 and earlier (an update is available in 21.0.2) for Windows and MacOS. The two critical flaws (CVE-2019-8253 and CVE-2019-8254) are memory corruption glitches that could lead to arbitrary code execution.
Honggang Ren of Fortinet’s FortiGuard Labs was credited with discovering the flaws.
A final critical vulnerability was disclosed in versions 1.14 and earlier of Brackets for Windows, Linux and MacOS (users are encouraged to update to version 1.14.1).
The flaw (CVE-2019-8255) is a command infection vulnerability that could enable arbitrary code execution. Tavis Ormandy of Google Project Zero was credited with discovering the flaw.
Adobe also reported an important flaw (CVE-2019-8256) in ColdFusion Update 6 and earlier versions, stemming from insecure inherited permissions of the default installation directory, that could enable privilege escalation. A fix is available in Update 7.
Nuttakorn Tungpoonsup, Ammarit Thongthua and Sittikorn Sangrattanapitak from Secure D Center Research Team, Secure D Center Co.,Ltd. were credited with discovering the flaw.
Overall, Adobe issued more critical patches in December than it did in November, when it warned Illustrator 2019 users that two critical memory-corruption vulnerabilities could allow for an attacker to remotely connect to a Windows machine, execute code and gain control of the targeted system.
Free Threatpost Webinar: Risk around third-party vendors is real and can lead to data disasters. We rely on third-party vendors, but that doesn’t mean forfeiting security. Join us on Dec. 18th at 2 pm EST as Threatpost looks at managing third-party relationship risks with industry experts Dr. Larry Ponemon, of Ponemon Institute; Harlan Carvey, with Digital Guardian and Flashpoint’s Lance James. Click here to register.











