Researchers are on the hunt for the infection vector behind a mysterious mobile malware that has infected over 45,000 Android devices in the past six months.
Researchers said they have detected a surge in detections of the malware, dubbed Xhelper, which can hide itself from users, download malicious apps onto the phone and display pop-up advertisements. Perhaps most frustrating for victims, the malware is persistent – it is able to secretly re-install itself after victims try to uninstall it, researchers with Symantec said.
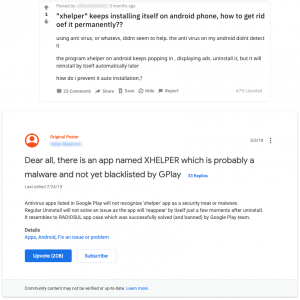
“We have seen many users posting about Xhelper on online forums, complaining about random pop-up advertisements and how the malware keeps showing up even after they have manually uninstalled it,” said researchers in a Tuesday analysis.
Xhelper continues to plague mobile users, particularly those in India, the U.S. and Russia – in the last month alone, an average of 131 devices have been infected daily.
Mystery Attack Vector
Researchers are still trying to pin down the infection vector used to distribute Xhelper. None of the samples analyzed have been found in apps on the Google Play Store.
However, researchers suspect that Xhelper is an application component that comes pre-installed on some phone brands. If it were an application component, it wouldn’t be listed in the device’s application launcher – which researchers say makes it easier for the malware to perform its malicious activities undercover.
“We believe it to be unlikely that Xhelper comes preinstalled on devices given that these apps don’t have any indication of being system apps,” said researchers. “Since it is unlikely that the apps are systems apps, this suggests that another malicious system app is persistently downloading the malware, which is something we are currently investigating.”
Various researchers have other theories. Malwarebytes researchers, who first analyzed the malware back in August, hypothesized that the malware was being spread via web directors or third-party, sketchy websites prompting users to download untrusted apps.
Malware Pool
Upon successful connection to the C2 server, Xhelper will start displaying random pop-ups, as well as installing additional payloads such as droppers, clickers and rootkits to the compromised device.
“We believe the pool of malware stored on the [C2] server to be vast and varied in functionality, giving the attacker multiple options, including data theft or even complete takeover of the device,” said the researchers.
Once Xhelper gains a foothold on the victim’s device, it begins executing its core malicious functionality by decrypting to memory the malicious payload embedded in its package. The malicious payload then connects to the attacker’s C2 server and waits for commands.
“To prevent this communication from being intercepted, SSL certificate pinning is used for all communication between the victim’s device and the [C2] server,” said researchers.
Making matters worse, the malware continues to re-install itself to the device – even after victims have uninstalled it or performed a factory reset.
“Xhelper can’t be launched manually since there is no app icon visible on the launcher. Instead, the malicious app is launched by external events, such as when the compromised device is connected to or disconnected from a power supply, the device is rebooted or an app is installed or uninstalled,” said researchers.
Evolution
When Xhelper was first seen in March 2019, the malware had “relatively simple” code and main functions around forcing victims to visiting advertisement pages for monetization purposes. Since then the code has drastically changed.
While initially the malware’s ability to connect to a C2 server was written into the malware, that functionality was eventually moved encrypted payload, in an attempt to evade signature detection.
“As described previously, Xhelper’s functionality has expanded drastically in recent times,” said researchers. “We strongly believe that the malware’s source code is still a work in progress.”
In the meantime, researchers urge users to keep their software up to date, avoid downloading apps from unfamiliar sites and only install apps from trusted sources.
What are the top mistakes leading to data breaches at modern enterprises? Find out: Join experts from SpyCloud and Threatpost senior editor Tara Seals on our upcoming free Threatpost webinar, “Trends in Fortune 1000 Breach Exposure.” Click here to register.