Apache has released version 2.4.9 of its ubiquitous HTTP web server (HTTPD), resolving two security vulnerabilities and a number of other bugs in the process.
The Apache Software Foundation is recommending HTTPD 2.4.9 over all previous versions.
The first patch fixes CVE-2014-0098. It aims to mitigate a cookie logging issue by accepting fewer redundant string parsing passes. In its latest iteration, Apache will log only cookies containing value assignments. Valueless cookies will be ignored. In all, the new version will prevent segmentation faults when logging truncated cookies.
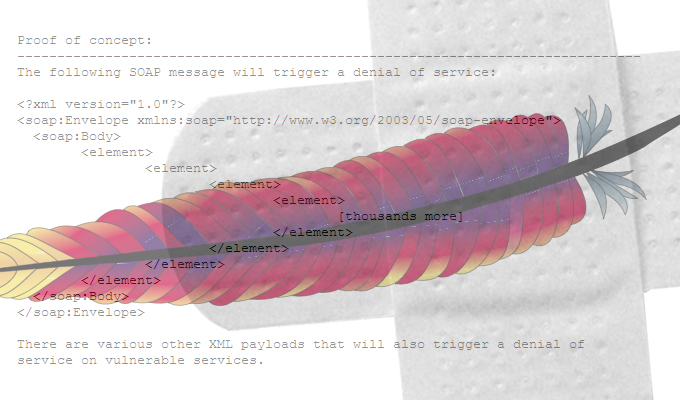
The second security bulletin closes off CVE-2013-6438, which – on unpatched systems – could potentially enable a denial of service condition. The bug existed in mod_dav, Apache’s Web distributed authoring and versioning module. The fix will do a better job of properly monitoring the length of character data while removing leading spaces. Ultimately, the fix should eliminate the DoS risk posed by specially crafted DAV write requests in prior versions.
Stay tuned for Apache security update news in the future.