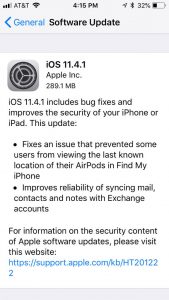
Apple has officially added a controversial security feature, USB Restricted Mode, to iPhones as part of its new iOS 11.4.1, released on Monday.
The feature removes the infamous iPhone USB access feature, blocking out hackers – but also potentially law enforcement – from accessing a locked phone’s data via the device’s port.
iPhone users who update their devices can now see a new control for USB Accessories under their Settings>Touch ID & Passcode option. The switch is now turned off by default – meaning that an hour after the iPhone has been locked, the phone’s Lightning port (its charging and data port) will automatically lock.
 The new feature means that users can still charge their phones, but will not be able to continue to transfer data to and from their device until they enter a passcode.
The new feature means that users can still charge their phones, but will not be able to continue to transfer data to and from their device until they enter a passcode.
When the feature was first revealed in June, an Apple spokesperson told Threatpost that the company had wanted to add additional mitigation which would remove the USB as an attack surface when customers don’t need it, without negatively impacting the user experience.
However, the move also escalates a longstanding conflict between Apple and law enforcement, which peaked in 2016, when Apple refused to comply with an FBI request to help unlock the iPhone of the San Bernardino gunman who killed 14 people in 2015.
Apple’s new feature effectively blocks off several devices (some of which have been used by federal law enforcement agencies) that have been designed to hack into iPhones via the Lightning port.
One such example are Cellebrite’s UFED devices, which are forensic tools for iPhones and iPads that can reportedly unlock iOS devices.
Another device, called the GrayKey box, has been known to unlock iPhones using the Lightning port to install software that cracks the passcode of an iOS device. Reports have found that several federal agencies – such as the FBI and other law enforcement – have used the device, made by a company called Grayshift, to unlock up-to-date iPhones.
Grayshift, for its part, reportedly claimed that it has found a workaround to Apple’s solution, according to a report by Motherboard in June.
While these devices provide valuable options for law enforcement who may need data hidden away on iPhones, “It is in Apple’s best interest to protect the privacy of its users, and it is in the best interest of law enforcement to support their investigations in the best way possible,”Troy Kent, threat researcher at Awake Security, told Threatpost. “Unfortunately, protecting the privacy of law abiding consumers also protects the privacy of criminals but it’s not like this is a new argument. It’s akin to the question as to whether or not we should just surveil the general population because it would capture crime, regardless of the effect the lack of privacy has on everyone else.”










