Unknown attackers are using a recently patched vulnerability in Samba to spread a resource-intensive cryptocurrency mining utility. To date, the operation has netted the attackers just under $6,000 USD, but the number of compromised computers is growing, meaning that a significant number of Samba deployments on *NIX servers remain unpatched.
The attack also demonstrates that the vulnerability in Samba, CVE-2017-7494, can extend EternalBlue-like attacks into Linux and UNIX environments. Samba is a software package that runs on Linux and UNIX servers and sets up file and print services over the SMB networking protocol, integrating those services into a Windows environment.
The Samba vulnerability is similar to the SMB bug exploited on May 12 by attackers using the NSA’s EternalBlue exploit to spread WannaCry ransomware. Experts warned that EternalBlue can be fitted with any measure of attack, and they have a similar message about this flaw, which has been nicknamed SambaCry.
Researchers at Kaspersky Lab said that one of their honeypots snagged on May 30 some of the first exploits targeting the Samba vulnerability. The payload was a two-headed threat: a Linux backdoor and a mining utility called Cpuminer that is leveraging the processing power of its victims to create Monero cryptocurrency.
“The attacked machine turns into a workhorse on a large farm, mining crypto-currency for the attackers,” Kaspersky Lab said in a report published on Securelist.com.
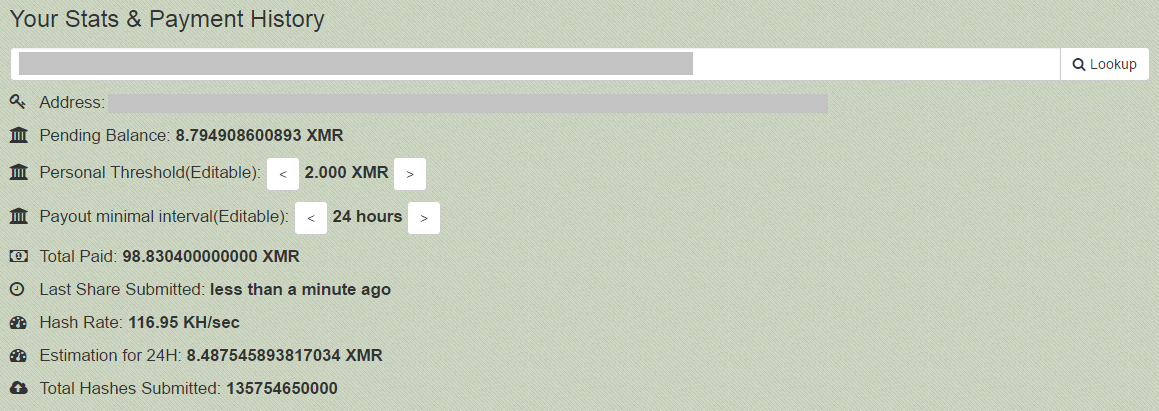
The researchers said the attackers’ Monero wallet and pool address are hardcoded in the attack.
“According to the log of the transactions, the attackers received their first crypto-coins on the very next day, on April 30th,” Kaspersky Lab said. “During the first day they gained about 1 XMR (about $55 according to the currency exchange rate for 08.06.2017), but during the last week they gained about 5 XMR per day. This means that the botnet of devices working for the profit of the attackers is growing.”
As of Friday, the attackers had mined about $6,000 USD, and Kaspersky Lab said it was unsure about the scale of the attack. Upon disclosure of the Samba vulnerability almost three weeks ago, Rapid7 said an internet scan using its ProjectSonar software found more than 104,000 endpoints running vulnerable versions of Samba over port 445, the SMB port. More than 92,000 are running versions of Samba that have no patches available. The vulnerability was introduced into Samba in 2010 in version 3.5.0; admins should upgrade to patched versions: 4.6.4, 4.5.10 and 4.4.14.
Kaspersky Lab said the exploit is assembled as a Samba plugin, below. After running a check—a file containing random symbols—to see whether the server has write permissions for the network, the attack must then brute-force the full path to dropped file. The most obvious paths are laid out in Samba instruction manuals, Kaspersky Lab said. Once it finds the path, the exploit is loaded and executed in the context of the Samba server process using the vulnerability; it runs only in virtual memory.
Kaspersky Lab said the attacks captured by its honeypot contained two files, a Linux backdoor and the miner. INAebsGB.so and cblRWuoCc.so respectively. INAebsGB.so is a reverse shell that connects to the port of the IP address specified by the owner giving it remote access to the shell.
“As a result, the attackers have an ability to execute remotely any shell-commands. They can literally do anything they want, from downloading and running any programs from the Internet, to deleting all the data from the victim’s computer,” Kaspersky Lab said, adding that this is similar to the SambaCry exploit in Metasploit.
The other file, cblRWuoCc.so, downloads and executes Cpuminer from a domain registered on April 29.
Coincidentally, another set of attackers used EternalBlue to spread a cryptocurrency miner called Adylkuzz for Monero on Windows machines. Monero is marketed as a privacy conscious cryptocurrency, and goes to great lengths to obfuscate its blockchain making it a challenge to trace any activity.
The Adylkuzz attacks pre-date WannaCry with the first samples going back to April 24, researchers at Proofpoint said. More than 20 virtual private servers were scanning the internet for targets running port 445 exposed, the same port used by SMB traffic when connected to the internet, and the same port abused by EternalBlue and DoublePulsar.