 Every year it seems that security-related news advances further from its roots in national security circles, IT departments, and the antivirus industry into the mainstream consciousness. From July to the end of year was no exception. However, despite a handful of flashy security stories, F-Secure claims that the second half of 2012 was really about things that rarely (if ever) come up in local and national news: botnets, ZeroAccess in particular, Java and other Web exploits, and the ubiquitous Zeus banking Trojan.
Every year it seems that security-related news advances further from its roots in national security circles, IT departments, and the antivirus industry into the mainstream consciousness. From July to the end of year was no exception. However, despite a handful of flashy security stories, F-Secure claims that the second half of 2012 was really about things that rarely (if ever) come up in local and national news: botnets, ZeroAccess in particular, Java and other Web exploits, and the ubiquitous Zeus banking Trojan.
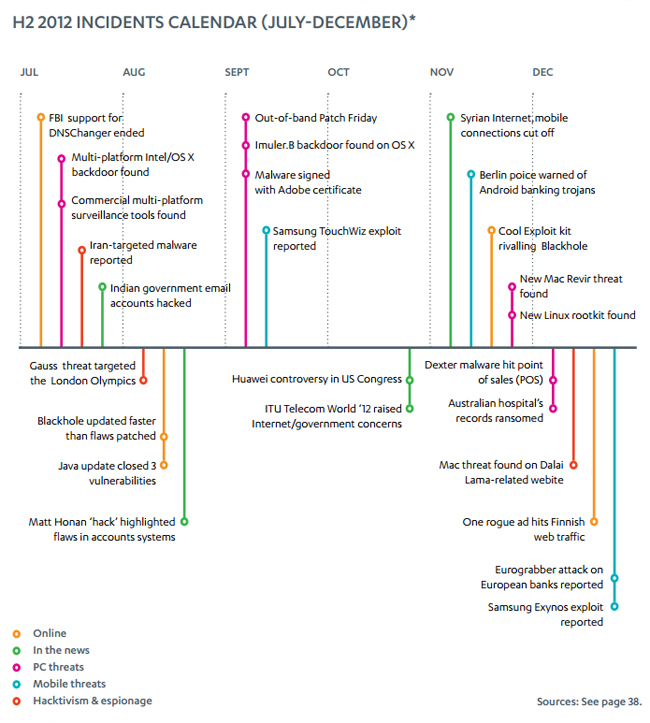
F-Secure’s assessment [pdf] of second half standout threats is somewhat understated considering the other stories that came out during that six month period: rampant misinformation, talk of some global Internet apocalypse, and otherwise irrational hoopla abounded around the FBI’s thoroughly anticipated and largely inconsequential cessation of support for DNSChanger-infected machines, there was yet-another sophisticated cyberespionage tool, this one called Gauss; the Blackhole exploit kit continued improving itself as Cool and others emerged to rival the once dominant crime-pack; someone targeted Iran with malware (again); there was an out-of-band, emergency Patch Friday resolving a serious Internet Explorer zero-day; there was malware with legit Adobe signatures and a Linux rootkit and the Dexter malware and Huawei in the halls of congress and Eurograbber and Mac malware targeting Tibetan activists among many, many other threats. Amidst all these, F-Secure researchers are steadfast that the second half of 2012 was about botnets, banking Trojans, and Web exploits.
2011 was marked by a number seemingly successful botnet takedowns, but in 2012 some of those botnet were resurrected by there botmasters, the report indicates. Zeus came back strong, implementing new features, like “gameover” that shifted the bot away from a centralized command and control infrastructure and toward more of a peer-to-peer structure. Despite takedown attempts new Zeus variants like Citadel and Ice IX emerged and the bot continues to make cybercrime easy for thieves of all skill levels. The Carberp botnet resurfaced as well. A bot called DorkBot hit the scene in October making money through click-fraud and ransomware scams.
Android bots are still in their infancy, largely serving SMS spam, the report claims. Android malware, however, is making strides, accounting for some 79 percent of all mobile malware. Symbian comes in a distant second, accounting for only 19 percent of such threats.
F-Secure’s report especially highlights the ZeroAcces botnet, which they claim was the fastest growing network in the second half of the year. It’s partially a click-fraud bot with 140,000 unique IPs clicking 140 million ads per day, reportedly costing legitimate ad networks, who have difficulty determining the difference between real and fraudulent clicks, more than $900,000 a day. ZeroAccess is also an effective Bitcoin miner as well, allocating at least half of its resources to stealing the digital currency.
The Zeus banking Trojan (as opposed to the Zeus botnet mentioned above) continues its reign as the most prolific bank robber of the Internet age, injecting websites with phishing forms and stealing user login credentials. F-Secure saw 644 URLs, mostly in the US, targeted by Zeus’s Web-injections over the six month span. The sites included personal and corporate banking sites, investment and trading sites, credit card services, and more generally popular websites.
The vast majority of attacks, the report claims, centered around just four vulnerabilities: Windows TrueType-related CVE- 2011-3402, Adobe-related CVE-2010-0188, and the Java-related CVE-2012-4681 and CVE-2012-5076 vulnerabilities. CVE-2012-0507 and CVE-2012-1723, also Java issues, came in a distant fifth and sixth place respectively.
F-Secure attributes this vulnerability preferentiality to the rise of the exploit kit and kit-makers’ tendency toward building exploits for these particular vulnerabilities into their kits, often faster than the respective vendors can ship patches. In many cases, these vulnerabilities have been fixed, but many users remain stubborn about installing updates.
Vulnerability exploitation along with social engineering is increasing as the preferred infection vector that used to be dominated by Trojans. F-Secure’s data revealed that such attacks accounted for 28 percent of infections. Among vulnerability exploiting attacks, 68 percent of the malware exploited the java development platform.
“The sheer volume of Java-related detections indicate both the widespread popularity of that platform and its susceptibility to the malicious inventiveness of malware authors,” wrote the researchers.
F-Secure also highlights the reality that as Webhosting becomes easier and more seamless for well-meaning users, it also becomes so for criminals. Dynamic DNS providers, subdomain and redirection hosting, blog and content hosting, file hosting, and app markets are among the most commonly used services for malware distribution.
There were no major, platform-specific malware outbreaks of note in the last six months, according to the report. On the contrary, attackers seem to have taken a liking to cross-platform attacks where OS-neutral malware can infect different operating systems. Once that system is compromised the attacker can determine which operating system it runs before loading OS-specific malware onto it.
Watering hole attacks are now a suitable alternative to more traditional corporate espionage methods involving maliciously crafted documents loaded up with malware and exploits. Instead of infecting random sites or trying to spear-phish persons of interest, attackers are compromising sites that they believe their targets are likely to visit (i.e. watering holes) in order to install backdoors on high-value networks. Organizations that service potentially valuable targets are now at risk of acting as an attack vector themselves, meaning that target organizations now must keep an eye on the websites and other services that their employees are likely to use in addition to monitoring their own networks.
According to the report, Windows remains the most frequently targeted operating system, but malware authors are increasingly attempting to target Apple users. In all of 2011, F-Secure recorded just 59 variants of Mac malware. In the second half of 2012, the number of unique samples increased to 121.
In other news, passwords remain problematic.
“The password is dead and we all know it. But unfortunately, its successor has yet to turn up,” researchers wrote.










