A malware family called Cardinal RAT has reappeared, after two years of silence, in a series of attacks that have been targeting Israel-based financial technology firms.
After Cardinal RAT was first detected in 2017, the malware disappeared for two years. But now, in this latest campaign, researchers with Palo Alto Networks’ Unit 42 said that the malware is back, and has adapted new tricky modifications aimed at evading detection and hindering analysis.
“Since April 2017, we have observed Cardinal RAT in attacks against two customers, both customers were FinTech companies who write software relating to forex [foreign exchange] and cryptocurrency trading, and both companies were based in Israel,” Unit 42 researchers Tom Lancaster and Josh Grunzweig said in a Tuesday analysis.
Cardinal RAT
When it was first detected in 2017, researchers noted that Cardinal RAT had a very low volume (roughly 27 total samples). The malware is delivered via a downloader dubbed “Carp” which uses malicious macros in Microsoft Excel documents to compile embedded source code into an executable, which then deploys the Cardinal RAT malware family.
The malware is capable of stealing username and credentials, cleaning out cookies from browsers, keylogging and capturing screenshots on targeted systems.
While the latest version of Cardinal RAT (version 1.7.2) is similar, it also now employs various obfuscation techniques to hinder analysis of the underlying code.
“Underneath all this obfuscation, this Cardinal RAT payload does not have any significant changes compared to the previously discussed version in terms of its operation or capabilities,” researchers said. “One of the most significant changes lies in the obfuscation used by the malware; all of the functions, methods, and variables have been renamed to MD5 hashes.”
For instance, the malware uses steganography, which is the practice of concealing a file or message within an image. It’s doing this to hide itself using .NET and an embedded bitmap (BMP) file. After it is executed, the malware will read the BMP file, parse out pixel data from the image and eventually decrypt the result using a single-byte XOR key.
EVILNUM Link
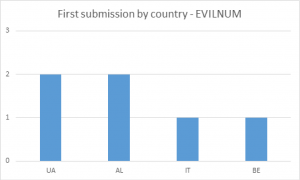
Researchers also discovered a possible relationship between Cardinal RAT and another malware family, called EVILNUM.
Both malware families targeted two companies in short succession; and Both families were distributed using malicious documents, which containing lists of the names and numbers of individuals involved in cryptocurrency.
EVILNUM is a JavaScript-based a first-stage malware family that is used in attacks against similar organizations, researchers said. The malware gives an attacker data about the infected host before they decide to install other utilities on the machine. EVILNUM is also able to set up persistence, download additional files and take screenshots on infected machines.
“When looking at files submitted by the same customer in a similar time frame to the Cardinal RAT samples, we saw that the customer had also submitted a malware family we’d been tracking as EVILNUM,” they said. “From our viewpoint this is another family that seems to be used solely in attacks against finance related organisations.”
Companies can protect themselves against the dual threat of Cardinal RAT and EVILNUM through looking out for e-mails with LNK file as attachments, or attached ZIP files containing a single LNK file inside them.
“Organizations with effective spam filtering, proper system administration and up-to-date Windows hosts have a much lower risk of infection,” researchers said.