North Korean APTs Stole ~$400M in Crypto in 2021
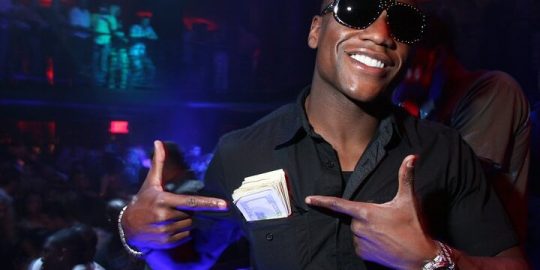
Meanwhile, EtherumMax got sued over an alleged pump-and-dump scam after using celebs like Floyd Mayweather Jr. & Kim Kardashian to promote EMAX Tokens.
Infosec Insider content is written by a trusted community of Threatpost cybersecurity subject matter experts. Each contribution has a goal of bringing a unique voice to important cybersecurity topics. Content strives to be of the highest quality, objective and non-commercial.
Sponsored Content is paid for by an advertiser. Sponsored content is written and edited by members of our sponsor community. This content creates an opportunity for a sponsor to provide insight and commentary from their point-of-view directly to the Threatpost audience. The Threatpost editorial team does not participate in the writing or editing of Sponsored Content.