Two Chinese nationals have been charged in the massive 2015 data breach of health insurer Anthem that impacted more than 78 million people.
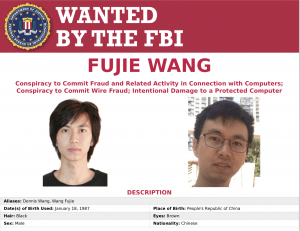
Fujie Wang, 32, and another Chinese man, who remains unnamed, were allegedly part of a China-based hacking group that was behind the breach of Indiana-based health insurance giant Anthem, which led to the compromise of 78.8 million customer records, as well as between 8.8 and 18.8 million Blue Cross Blue Shield customer records. The two were indicted on Tuesday.
“The allegations in the indictment unsealed today outline the activities of a brazen China-based computer hacking group that committed one of the worst data breaches in history,” said Assistant Attorney General Benczkowski in a statement, Thursday. “These defendants allegedly attacked U.S. businesses operating in four distinct industry sectors, and violated the privacy of over 78 million people by stealing their PII [personal identifiable information.] The Department of Justice and our law enforcement partners are committed to protecting PII, and will aggressively prosecute perpetrators of hacking schemes like this, wherever they occur.”
Beginning in February 2014, the two Chinese men, as part of the China-based group, allegedly hacked into the computer networks of Anthem, as well as three other unnamed U.S. businesses.
They did so using spearphishing techniques: By sending emails with embedded hyperlinks to employees of the targeted businesses, including Anthem, the indictment said.
After victims clicked the hyperlink, a file was downloaded that installed a backdoor onto their computers, which would provide remote access to the victim’s system through a server controlled by the hacking group.
They then allegedly installed malware and tools on the compromised computer systems to further compromise the network, and eventually scooped up Anthem customer PII and confidential business information between October and November 2014.
“As part of the computer intrusion and data breach of Anthem, the defendants identified and ultimately stole data concerning approximately 78.8 million persons from Anthem’s computer network, including names, health identification numbers, dates of birth, Social Security numbers, addresses, telephone numbers, email addresses, employment information and income data,,” the Department of Justice said in a statement.
The indictment alleged that Wang eventually gained access to Anthem’s enterprise data warehouse, and from there transferred encrypted archive files containing PII and other data to China throughout January 2015.
The data breach of Anthem led to a wave of aftermath and backlash for the health insurance company: In 2015, the company came under fire for refusing to undergo vulnerability scans and configuration compliance tests. In 2017, as part of a litigation settlement, Anthem said it would pay $115 million – the funds would mostly go towards two years of credit monitoring for the breach’s victims. And in 2018, it agreed to pay $16 million to the U.S. government for HIPAA violations.
The Anthem hackers represent only the latest legal action made as U.S. law enforcement cracks down on cybercrime: in March, a Sydney man was arrested after allegedly selling hundreds of thousands of compromised account details for subscription streaming services, including for Netflix, Hulu and music streaming service Spotify; and in April, a Romanian duo was convicted for infecting hundreds of thousands of computers with malware that scooped up credentials and financial information, and scamming victims out of millions of dollars.