Cisco Systems is warning of a critical bug in two of its license management tools that could allow an unauthenticated remote attacker to execute arbitrary queries. A successful attack could allow for an attacker to modify and delete random data in Cisco product lifecycle management applications.
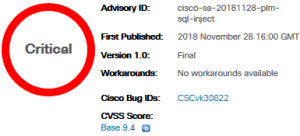 The alert was issued on Wednesday via a Cisco Security Advisory where the company said there is no workaround for the bug and that affected customers would have to download a software patch. The vulnerability itself has a Common Vulnerability Scoring System rating of 9.8 out of 10.
The alert was issued on Wednesday via a Cisco Security Advisory where the company said there is no workaround for the bug and that affected customers would have to download a software patch. The vulnerability itself has a Common Vulnerability Scoring System rating of 9.8 out of 10.
The bug (CVE-2018-15441) is tied to the web framework code of Cisco Prime License Manager (PLM) that could allow an unauthenticated, remote attacker to execute arbitrary Structured Query Language (SQL) queries. SQL is a standard language for communicating with relational databases.
“The vulnerability is due to a lack of proper validation of user-supplied input in SQL queries. An attacker could exploit this vulnerability by sending crafted HTTP POST requests that contain malicious SQL statements to an affected application,” according to the Cisco Security Advisory. “A successful exploit could allow the attacker to modify and delete arbitrary data in the PLM database or gain shell access with the privileges of the postgres user.”
Affected is Cisco Prime License Manager Releases 11.0.1 and later. Products affected are Cisco Unified Communications Manager and Cisco Unity Connection. The company said impacted are both products where the standalone and bundled installations of PLM are installed.
While no workaround is available, software fixes address the issue and will need to be manually installed by network admins. The Cisco Prime License Manager Release patch “ciscocm.CSCvk30822_v1.0.k3.cop.sgn” is available via Cisco’s Software Center. Cisco said it isn’t aware of the vulnerability being exploited in the wild.
Saudi Information Technology Company researcher Suhail Alaskar is credited for reporting the vulnerability. The initial public release of the bug was Wednesday, according to the advisory.










