For all that gets written about how poorly organizations have responded to data breaches as of late, believe it or not, one new study has deduced that companies are getting better. Almost three quarters of victims who sustained a compromise last year were able to contain it within 10 days.
The stat could be reflective of a somewhat positive trend, at least when it comes to the companies that Trustwave evaluated from 2012 to 2013 for its annual Global Security Report, released this morning.
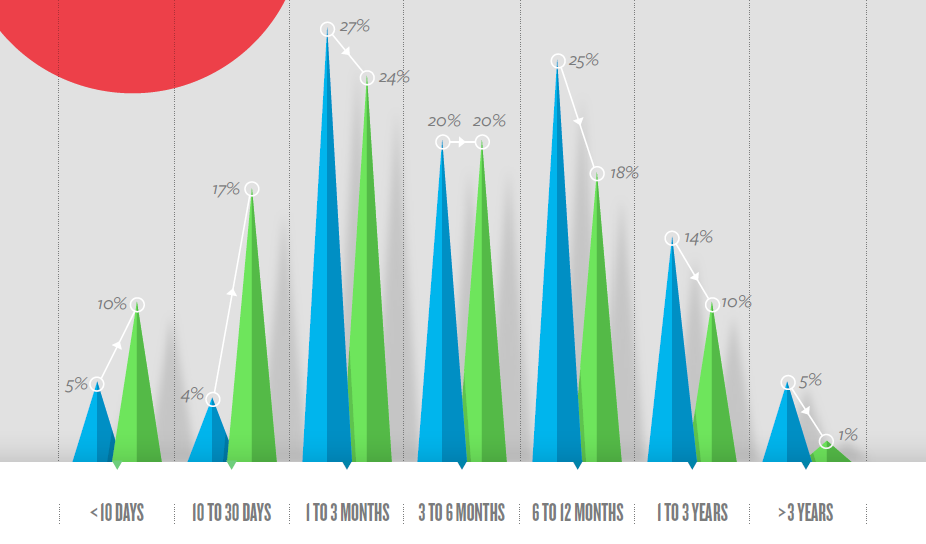
The security firm looked at three timelines to evaluate the median number of days it took certain organizations to detect breaches after there had been an intrusion, how long it took from detection to containment, and how many days it took the breach to elapse, from intrusion to containment.
From detection to containment the median time for companies was seven days while it took companies about 87 days, or roughly three months, to detect the breach from the intrusion.
On the whole, from intrusion to containment the median time for companies took about 114 days; 67 percent of victims were able to contain breaches in 10 days after they were detected, said Trustwave. The amount of time it takes companies to contain breaches is going down, Trustwave asserts.
In half of the compromises “the victim contained the breach within four months of the initial intrusion,” the report said before adding an additional stat: 71 percent of the breaches in 2013 were contained in six months.
One of the bigger drops, above, is the number of organizations that it took six to 12 months to contain a breach following an intrusion. The number dropped this year to 18 percent of companies, following 25 percent of them in 2012.
Elsewhere, the outfit determined that breaches that were self-identified led to shorter durations, something that “cut down on the time an attacker could siphon data from compromised systems and helped limit the repercussions.”
In those cases, the median time it took from intrusion to detection was lower, only 31.5 days from intrusion to detection and just a day from detection to containment, according to the company’s study.
These were somewhat rare occurrences however, as the report notes that 71 percent of the time last year victims it looked into did not detect their own compromises and instead used a combination of law enforcement, the public, merchant banks or some other third party.
For what it’s worth, Trustwave points out that while it has used the mean for breach reporting in years past, it’s opted for the median this year in hopes of preventing statistical outliers from skewing the data.
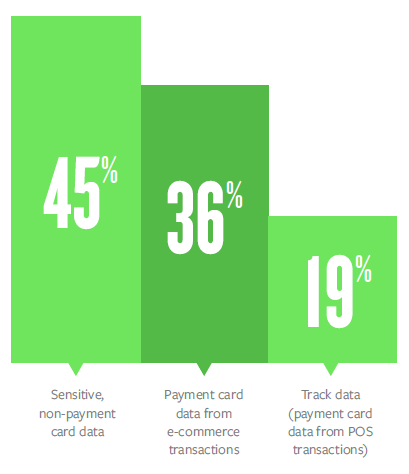 Another highlight of the study: 45 percent of the data stolen through the breaches it tracked in 2013 implicated serious non-payment card information. This includes information such as financial credentials, internal communications, merchant ID numbers and other personally identifiable information (PII).
Another highlight of the study: 45 percent of the data stolen through the breaches it tracked in 2013 implicated serious non-payment card information. This includes information such as financial credentials, internal communications, merchant ID numbers and other personally identifiable information (PII).
All in all, this shouldn’t come as too big of a surprise. There’s been a significant uptick in these bits of fringe information being targeted as of late. Attackers can take things such as a user’s address or their bank and employ social engineering tactics to get the information they really want. From there they can mend it together to solve a figurative puzzle about users and their habits.
While non-payment card data was on the rise this year—the 45 percent figure is a 33 percent increase from last year—some things never change: Payment card data still trumps all; 35 percent of the compromised data Trustwave analyzed came from ecommerce transactions and 19 percent of the breached data came from the card’s track data being compromised in POS transactions.
This means that more than half of the information attackers stole in breaches last year was sensitive banking information such as user’s card numbers, expiration dates and CVV codes. Data from the latter reflects the high profile breaches at retailers such as Target and Michael’s that came in December.
The company looked at 691 breaches across 24 countries for its annual research project, a 53.6 percent increase from the number of breaches it looked at in 2012.
As much of an undertaking as it sounds, the research is a tiny fraction of the work outlined in the bulky 100-plus page document. A smattering of other stats, including research on weak passwords, threat intelligence, exploit kits, spam, mobile vulnerabilities and more are discussed in the .PDF, which curious parties can download here.