It’s rare a week goes by now without a new strain of ransomware making headlines. Researchers described one of the latest earlier this week, a relatively affordable ransomware-as-a-service named AlphaLocker.
One of the main selling points to AlphaLocker is how cheap it is; the ransomware can be purchased directly from the author for as little as $65 USD, via Bitcoin, researchers claim. With proof of purchase, attackers get a copy of the actual ransomware, the master decryptor binary, and their own administrative panel, according to Cylance, which carried out a full review of the ransomware on Wednesday.
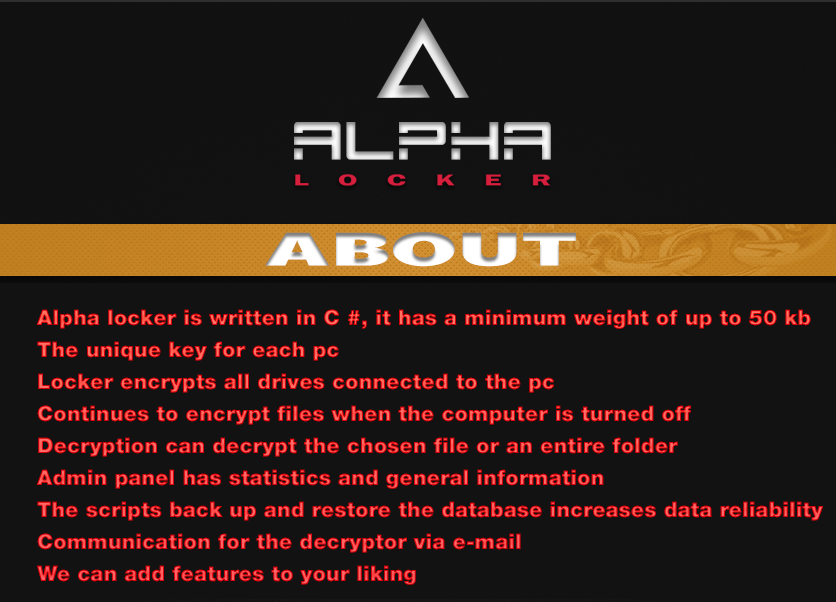
Advertising for AlphaLocker boasts the ransomware “encrypts all drives connected to the PC,” and “continues to encrypt files when the computer is turned off” but it’s the malware’s inexpensiveness that frightens Jim Walter, a researcher with the firm.
“The lower price point allows ‘less-skilled’ ne’er–do–wells to possess and control (and profit from) ransomware, with little to no coding and zero ramp-up time,” he warned.
Like most strains of ransomware, once it springs into action, AlphaLocker scours systems for a bevy of file types – editable by the ransomware’s buyer – and has a command and control server generate a random AES key to encrypt each of them.
As soon as the files have been encrypted, victims are given a text file and told to pay the ransomware by following a link and paying 0.35 Bitcoin.
While support files affiliated with the ransomware are in English, the firm believes the author behind it is Russian. Some of the panel files suggest the ransomware hails from a Russian background while researchers have seen AlphaLocker hawked by cybercriminals on Russian forums.
Walter, a senior member of Cylance’s SPEAR research team, points out that AlphaLocker is based on EDA2, a project built last year on open source code. Turkish researcher Utku Sen originally published EDA2 under the condition it’d only be used for educational purposes but it didn’t take long for the code to make its way into the real life ransomware. It was incorporated in the Magic ransomware in January, something which prompted Sen to abandon the project soon after.
Despite being built on readily available – and one would think easily detectable – open source code, AlphaLocker actually excels when it comes to evading detection.
The authors behind the ransomware periodically push updates to avoid getting caught by signature-based security technologies, Walter claims.
“While that practice is absolutely the norm amongst malware authors, it never ceases to amaze just how easily the bad guys are able to keep up the evasion, staying one step ahead of signature-based detection technologies,” Walter wrote.
Details around AlphaLocker come just a few days after the FBI issued a warning urging businesses hit by ransomware to resist paying attackers for access to their files.
One of those businesses, The Board of Water and Light in Lansing, Mich. is reportedly nearly recovered from a cyber attack that took down its system for nearly 12 days. The utility posted on Facebook last week that it was the victim of ransomware which spread throughout its corporate network via a phishing virus. According to a report earlier today in the Lansing State Journal, staffers with the office “spent three hours on each computer running scans to prevent the virus from returning” and that it should be completely recovered by Friday.