Cisco is warning of a critical flaw in the web server of its IP phones. If exploited, the flaw could allow an unauthenticated, remote attacker to execute code with root privileges or launch a denial-of-service (DoS) attack.
Proof-of-concept (PoC) exploit code has been posted on GitHub for the vulnerability (CVE-2020-3161), which ranks 9.8 out of 10 on the CVSS scale. Cisco issued patches in a Wednesday advisory for the flaw, which affects various versions of its Cisco IP phones for small- to medium-sized businesses.
According to Jacob Baines with Tenable, who discovered the flaw, Cisco IP phone web servers lack proper input validation for HTTP requests. To exploit the bug, an attacker could merely send a crafted HTTP request to the /deviceconfig/setActivationCode endpoint (on the web server of the targeted device).
This triggers a stack-based buffer overflow due to the lack of input validation: “In libHTTPService.so, the parameters after /deviceconfig/setActivationCode are used to create a new URI via a sprintf function call. The length of the parameter string is not checked,” according to Baines.
The end result is the attacker being able to crash the device, or even potentially execute code remotely.
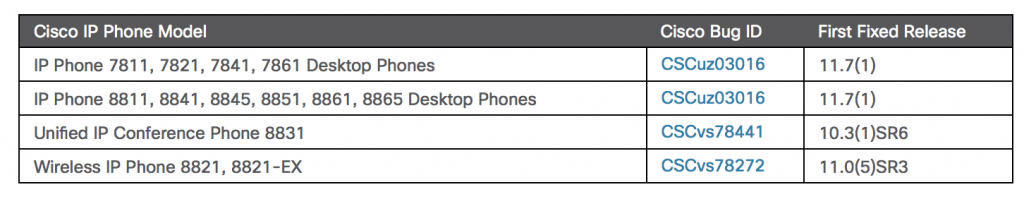
Affected products include: IP Phone 7811, 7821, 7841, and 7861 Desktop Phones; IP Phone 8811, 8841, 8845, 8851, 8861, and 8865 Desktop Phones; Unified IP Conference Phone 8831 and Wireless IP Phone 8821 and 8821-EX.
Of note, according to Cisco, some of these products (particularly the Wireless IP Phone 8821 and 8821-EX) are utilized by the healthcare industry who are currently on the frontlines of the coronavirus pandemic.
Cisco has also confirmed various products that aren’t affected by the flaw on its website. Beyond Cisco’s patches, one mitigation for the flaw is disabling web access on the IP phones (in fact, web access is disabled by default on IP phones), according to Cisco.
New findings by Tenable’s Baines also led Cisco to bump up the severity of a previously-discovered vulnerability (CVE-2016-1421) in its IP phones to critical on Wednesday. Previously the flaw was medium-severity (ranking 5 out of 10 on the CVSS scale).
However, Baines found that the flaw could be exploited by an unauthenticated actor (previously Cisco said exploiting the flaw required authentication) and could potentially enable remote code execution as well as DoS (previously Cisco found it could only enable DoS). Baines also found a produce, the Wireless IP Phone 8821, to be vulnerable that wasn’t listed on the affected list.
Other Critical Flaws
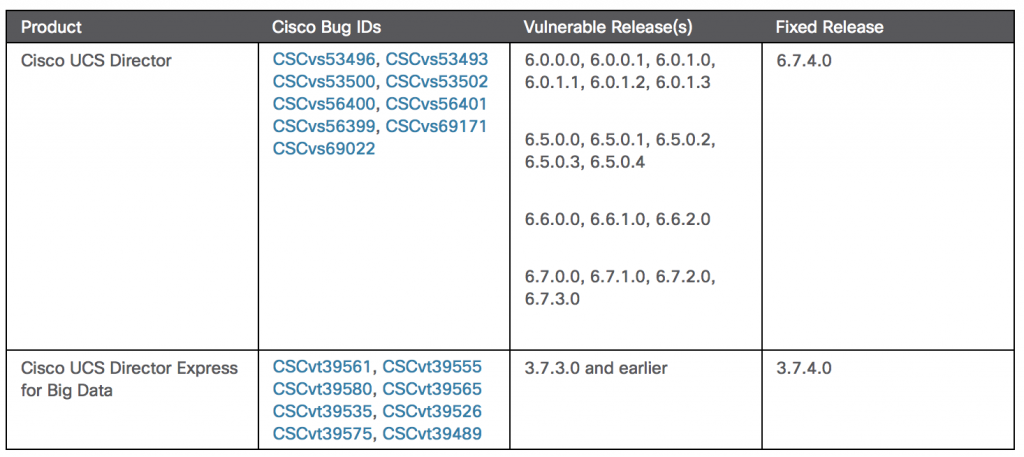
Cisco Wednesday also addressed critical- and high-severity flaws tied to nine CVEs in its Cisco Unified Computing System (UCS) Director and Cisco UCS Director Express for Big Data. Cisco UCS Director is an end-to-end management platform for various Cisco and non-Cisco data infrastructure components. Cisco UCS Director Express for Big Data is an open private-cloud platform that delivers Big-Data-as-a-Service on premises.
The flaws (CVE-2020-3239, CVE-2020-3240, CVE-2020-3243, CVE-2020-3247, CVE-2020-3248, CVE-2020-3249, CVE-2020-3250, CVE-2020-3251, CVE-2020-3252) exist in the REST API for both products, and may allow a remote attacker to bypass authentication or conduct directory traversal attacks on an affected device. Below is a list of affected products and the fixed releases.
Steven Seeley of Source Incite, working with Trend Micro’s Zero Day Initiative, was credited with reporting the flaws.
“The Cisco Product Security Incident Response Team (PSIRT) is not aware of any public announcements or malicious use of the vulnerabilities that are described in this advisory,” according to Cisco.
Worried about your cloud security in the work-from-home era? On April 23 at 2 p.m. ET, join DivvyCloud and Threatpost for a FREE webinar, A Practical Guide to Securing the Cloud in the Face of Crisis. Get exclusive research insights and critical, advanced takeaways on how to avoid cloud disruption and chaos in the face of COVID-19 – and during all times of crisis. Please register here for this sponsored webinar.