Much has been made of the cybersecurity skills shortage: It has long been an issue that many companies can’t effectively source the in-house talent they need, even as threats accelerate in both volume and sophistication. A recent survey however shows that the situation doesn’t appear to be improving.
A survey by the Enterprise Strategy Group (ESG) and the Information Systems Security Association (ISSA) of cybersecurity professionals shows that 70 percent believe their organization has been impacted by the global cybersecurity skills shortage. Meanwhile, about 45 percent believe the cybersecurity skills shortage has gotten worse over the past few years, while 48 percent say it’s about the same. Only 7 percent believe things have gotten better.
A survey late last year from ISC(2) put some quantifiable numbers around what the shortage looks like: The estimate for the amount of additional trained staff needed to close the skills gap came in at 4.07 million professionals worldwide. Translated, that means that the cybersecurity workforce needs to increase 62 percent in the U.S. market, ISC(2) said.
So how does the industry get there?
“The top ramifications of the skills shortage include an increasing workload, unfilled open job requisitions and an inability to learn or use cybersecurity technologies to their full potential,” according to the recently released ESG/ISSA report [PDF]. “No single action (funding, college programs, retraining, etc.) is working to bridge the cybersecurity skills gap. What’s needed is a holistic approach of continuous cybersecurity education (starting with public education), comprehensive career development and career mapping/planning – all with support from and integration with the business.”
Thomas Hatch, CTO and co-founder at SaltStack, told Threatpost that considering all pools of talent will be important in meeting the challenge.
“Cybersecurity is a rapidly changing landscape, just like other landscapes in technology,” he said. “It is critical to change the way we educate and assess talent. My policy certainly values a formal degree, but I do not hang my hat on it. I want to know that the job candidate knows, and how well they will work. This is all about looking beyond the degree and understanding the many ways that people can gain an education. Companies are making great headwinds to reshape how people are expected to learn and grow, however, it will continue to be of the utmost importance to vet candidates’ abilities, whether they have a formal degree or not.”
Trouble Spots
The fundamental causes for the skill gap are myriad, starting with a lack of training and career-development opportunities. About 68 percent of the cybersecurity professionals surveyed by ESG/ISSA said they don’t have a well-defined career path, and basic growth activities, such as finding mentor, getting basic cybersecurity certifications, taking on cybersecurity internships and joining a professional organization, are missing steps in their endeavors.
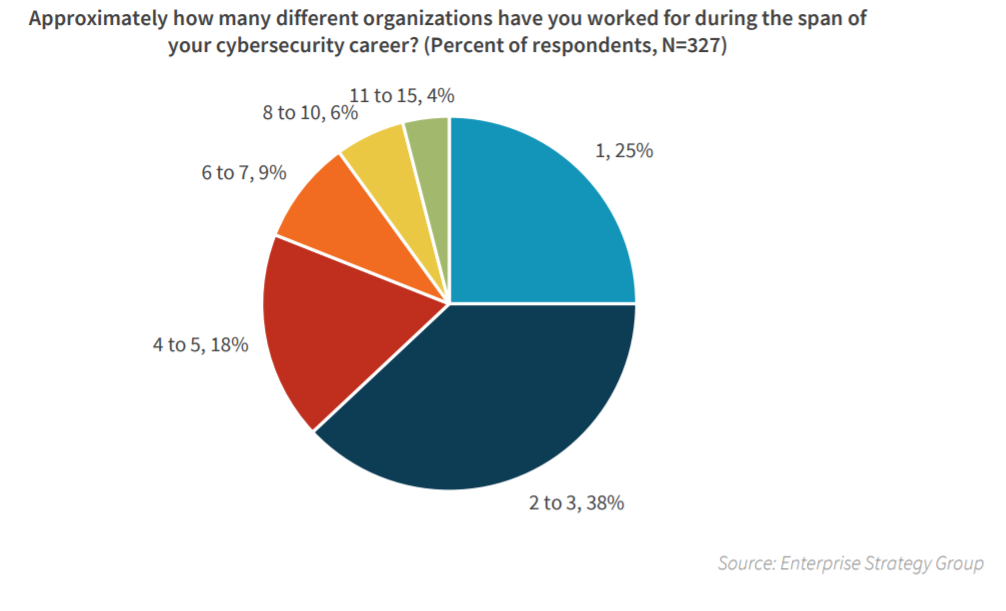
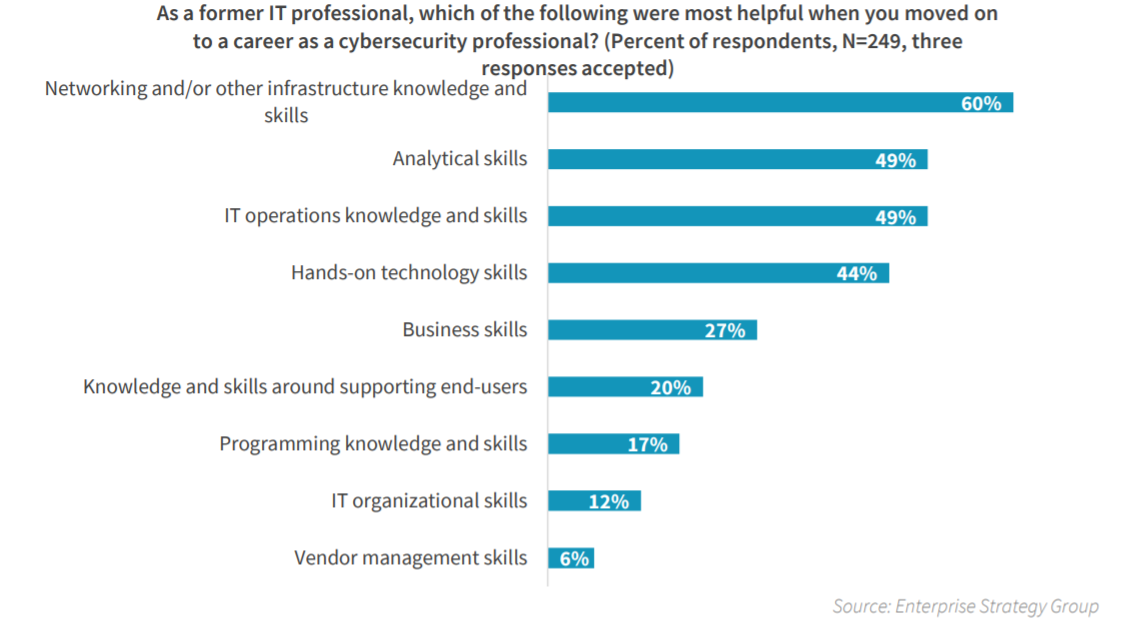
The survey also found that many professionals start out in IT, and find themselves working in cybersecurity without a complete skill set. A full 63 percent of respondents in the survey said they’ve worked in cybersecurity for less than three years, with 76 percent starting as IT professionals before switching their career to cybersecurity.
“Cybersecurity professionals often muddle through their careers with little direction, jumping from job to job and enhancing their skill sets on the fly rather than in any systematic way,” according to the report.
 To go along with this, the survey asked respondents to speculate on how long it takes a cybersecurity professional to become proficient at the job. The highest percentage of respondents (39 percent) believe it takes anywhere from three to five years to develop real cybersecurity proficiency, while 22 percent say two to three years, and 18 percent claim it takes more than five years.
To go along with this, the survey asked respondents to speculate on how long it takes a cybersecurity professional to become proficient at the job. The highest percentage of respondents (39 percent) believe it takes anywhere from three to five years to develop real cybersecurity proficiency, while 22 percent say two to three years, and 18 percent claim it takes more than five years.
The COVID-19 pandemic is not helping matters on this front: “Increasingly, lockdown has driven us all online and the training industry has been somewhat slow to respond with engaging, practical training supported by skilled practitioners who can share their expertise,” Steve Durbin, managing director of the Information Security Forum, told Threatpost. “Apprenticeships, on the job learning, backed up with support training packages are the way to go to tackle head on a shortage that is not going to go away.”
Another foundational issue uncovered in the report is the fact that executives often don’t understand the role of information security within their businesses, so CISOs and other cyber-leaders within an organization must take on larger advocacy and educational roles in order to develop the talent on their staff. When asked about the effectiveness of their CISOs, 42 percent rated the person as very effective, while a larger percentage (47 percent) responded somewhat effective. The remaining 12 percent said their CISOs were not very effective or not at all effective.
“This may reveal that few CISOs have the blend of business, leadership, communications and technical skills necessary for success,” according to the report. “CISOs are business, not technical, leaders.”
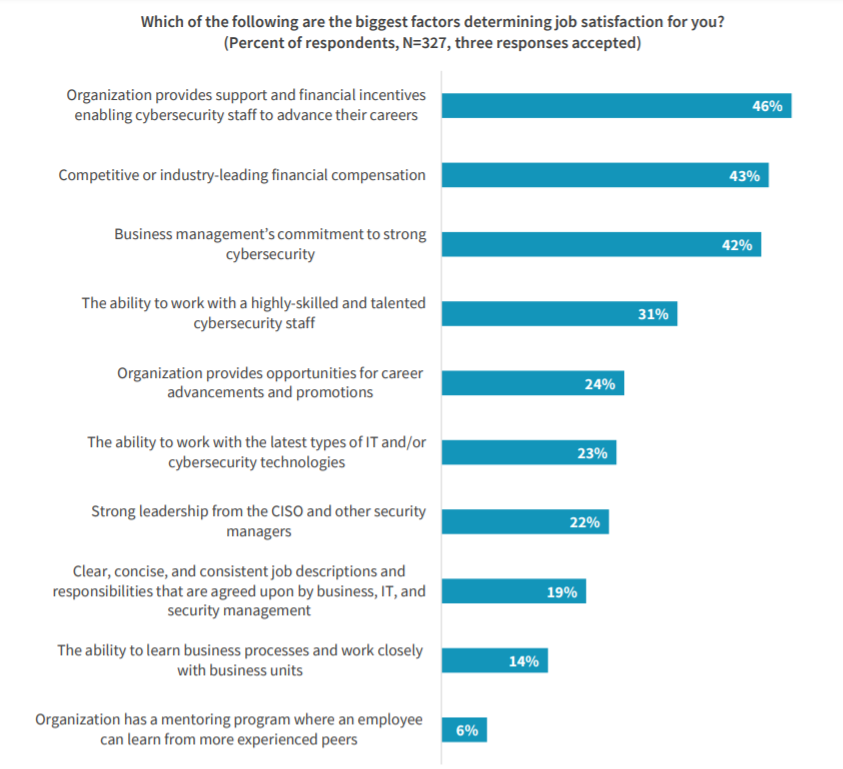
The flip side of the skills shortage is the fact that cybersecurity professionals are in high demand, and can pick and choose where they want to work. This puts companies on the hook for paying top salaries for these positions – a situation that many businesses can’t afford. The average salary in North America was $90,000 per year, according to the ISC(2). But the ESG/ISSA survey found that compensation is just one piece of the puzzle.
“Aside from compensation, cybersecurity job satisfaction is a function of many factors such as support and encouragement for continuing cybersecurity education, business management’s commitment to strong cybersecurity, and the ability to work with a highly skilled and talented cybersecurity staff,” the report found. “Organizations with all these qualities will have a distinct advantage in recruiting and hiring as they add to their cybersecurity staff.”
A less stressful environment could also woo talent to a business’ fold. When asked about personal mental and emotional health, 29 percent of respondents said that they’ve either experienced significant personal issues as a result of cybersecurity job stress or they know someone else who has. Another 17 percent said they either don’t know or prefer not to say.
All of this comes as cyberattacks continue to ramp up. Survey respondents were asked to compare the status of cyber-adversaries with that of cyber-defenders, and 67 percent of respondents said they believe that cyber-adversaries have a big advantage.
“The same issues present themselves year after year, including a shortage of skills, under-trained employees, and the stress and strain caused by a career in the cybersecurity field,” the report concluded.
Durbin added that companies will need to be proactive going forward to move the needle on the issues. “There is a practical element to be considered here: Organizations can either adopt an attitude that says we will work with the rich skill sets that are available and provide the security components by online training, apprenticeships and practical skills transfer through mentoring schemes, or they can sit back and wait for the perfect candidate to come along some time maybe never. I know which one I’d prefer to be,” he told Threatpost.
Complimentary Threatpost Webinar: Want to learn more about Confidential Computing and how it can supercharge your cloud security? This webinar “Cloud Security Audit: A Confidential Computing Roundtable” brings top cloud-security experts from Microsoft and Fortanix together to explore how Confidential Computing is a game changer for securing dynamic cloud data and preventing IP exposure. Join us Wednesday Aug. 12 at 2pm ET for this FREE live webinar with Dr. David Thaler, software architect, Microsoft and Dr Richard Searle, security architect, Fortanix – both with the Confidential Computing Consortium. Register Now.











