Defense giant Northrop Grumman is hiring software engineers to help it carry out “offensive cyberspace operations,” according to a recent job posting.
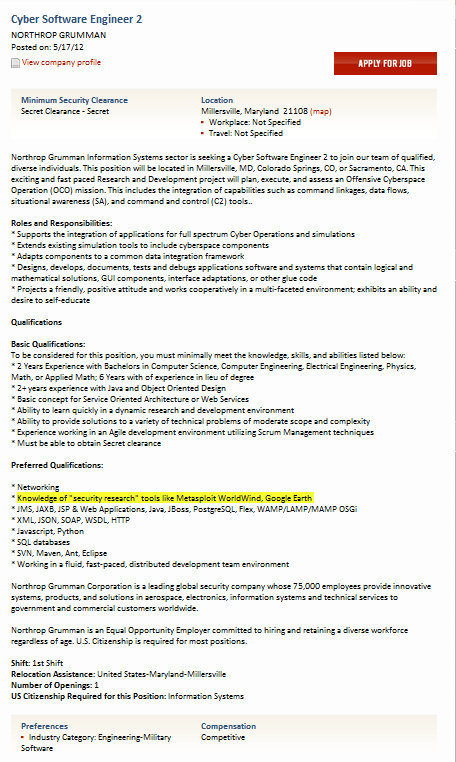
The job posting, for a “Cyber Software Engineer 2” appeared on the Website Clearancejobs.com and described a position on a Northrop R&D project to “plan, execute and assess an Offensive Cyberspace Operation (OCO) mission” that would include familiarity with tools like Metasploit and Google Earth and “integration of capabilities such as command linkages, data flows, situation awareness (SA) and command and control (C2) tools.”
Firms like Northrop have repeatedly been the target of sustained and sophisticated attacks from outside agents. Many of those attackers – euphemistically described as “Advanced Persistent Threats” – or APTs – are believed to have links to China and groups working for the People’s Liberation Army (PLA).
A spokeswoman for Northrop Grumman confirmed the validity of the job posting, but declined to elaborate on what Northrop was referring to with the term “Offensive Cyberspace Operations.”
As described, the job appears to be suited to a mid-level software engineer with experience in networking and agile development methodologies using a wide range of software- and Web development platforms, including Java, XML, JMS, PostgreSQL, Javascript and Python. The applicant is also expected to have knowledge of “‘security research’ tools like Metasploit, WorldWind (and) Google Earth,” according to the job posting.
“As a leading global security company and major provider of cyber services to the government, Northrop Grumman is always looking to hire talented and experienced cyber-professionals to join our company,” wrote Margaret Mitchell-Jones, Northrop’s Corporate Director for Media Relations in an e-mail to Threatpost. “At any given time there are a wide variety of job postings listed on www.northropgrumman.com/careers, which are often picked up and posted on career websites.”
In recent months, there has been discussion in policy circles about the need for the U.S. government to take a tougher line on such intrusions and for the U.S. military to develop cyber offensive capabilities to serve as a deterrent to future attacks.
The Defense Advanced Research Projects Agency (DARPA) has openly advocated improving U.S. cyber-offensive capabilities. In May, 2011, a report from the think tank The Center for a New American Century warned that cyber threats are outpacing the U.S. Government’s efforts to counter them, and called for the development of a kind of Monroe Doctrine for cyber space to discourage attacks against U.S. interests. In November, 2011, a report from the Office of the National Counterintelligence Executive accused China and Russia of a broad campaign of cyber espionage against the U.S. and its allies. Recent months have seen senior officials from the U.S. Department of State and Pentagon and their Chinese counterparts take part in joint cyber “war games” sponsored by the Center for Strategic and International Studies (CSIS) and Chinese think tanks.
However, the discussion hasn’t touched on the use of cyber offensive techniques by private firms. Such actions could be considered violations of domestic and international laws.
Whatever the source of the attacks, China would almost certainly be vulnerable. Independent security researchers have also pointed out that China, which has a formidable cyber offensive capability, lags badly when it comes to cyber defense, making the country susceptible to either counter-attacks or pre-emptive strikes.









