It was only a matter of time before the inevitable wave of malicious, election-tinged spam began to rain down upon internet users. In the wake of last week’s presidential debate between President Barack Obama and Republican nominee Mitt Romney, it appears the floodgates have opened.
According to a blog entry written by Websense’s Gianluca Giuliani earlier today, some of those spam e-mail messages, the ones that look as if they’re trying to gauge users’ interest in the candidates, are really leading to sites hosting the Blackhole Exploit kit code. The post claims attackers are using thousands of emails containing malicious .pdf, .jar and .exe files to dupe users into compromising their systems.
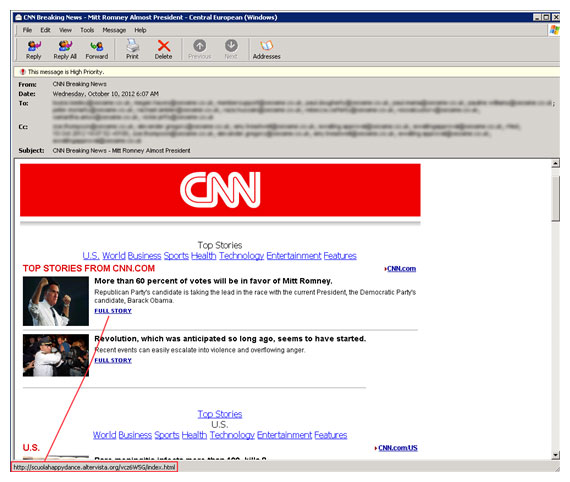
The post shows a fake email allegedly sent by “CNN Breaking News,” yet by hovering over one of the links, it’s easy to see users will be sent to a site hosting obfuscated BlackHole exploit kit 2.0 code.
Developers behind the kit have tried countless ways to get unsuspecting users to click through to their code, through fake automated Craigslist email notifications, fake AT&T emails, along with fake ADP and FDIC notifications.
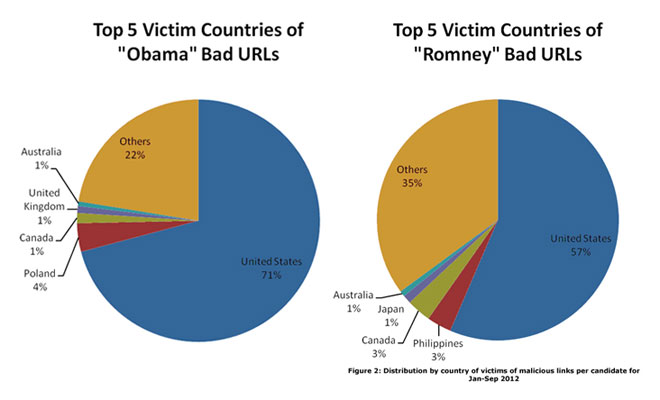
Attackers who choose to forgo with the malicious presidential emails continue to fare pretty well using the old-fashioned website. On Trend Micro’s Security Intelligence Blog today, Technical Communications Specialist Jonathan Leopando discusses how attackers using politically charged words to lure users to sites have been successful. After analyzing scams using Romney and Obama’s name over the last three months, Obama emerged victorious – at least when it comes to triggering bad URLs. Obama garnered 26,559 malicious hits while Romney got 4,519. 79 percent of those “Obama” mentions were from diseased vector URLs, while 11 percent came from spam. That compares to 20 percent of bad Romney links and 64 percent Romney diseased vector URLs.
Interestingly enough, while the majority of these bad URLs hit users in the U.S., a sliver, just more than five percent of Obama and Romney links, affected users through Europe (U.K., Poland), Asia and Canada.