Microsoft booted eight malicious apps from its official desktop and mobile app store after researchers found the programs surreptitiously mined for Monero cryptocurrency.
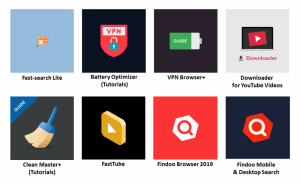
Researchers who discovered the apps said that an unspecified, but significant number, of users may have downloaded the rogue apps from the official Microsoft Store. The eight apps are; Fast-search Lite, Battery Optimizer (Tutorials), VPN Browser+, Downloader for YouTube Videos, Clean Master+ (Tutorials), FastTube, Findoo Browser 2019 and Findoo Mobile and Desktop Search.
“In total, we discovered eight apps from these developers that shared the same risky behavior,” according to Yuanjing Guo and Tommy Dong, with Symantec in a Friday post. “After further investigation, we believe that all these apps were likely developed by the same person or group.”
Researchers said they discovered the apps on Jan. 17. Soon after, Microsoft was notified and it removed the apps from Microsoft Store. The apps were published between April and December 2018, with most of them published toward the end of the year.
 According to researchers, once victims downloaded and launched the apps, the apps fetched a coin-mining JavaScript library. Adversaries did this by triggering Google Tag Manager (GTM) – a tag management system created by Google to manage JavaScript and HTML tags used for tracking and analytics on websites – in their domain servers.
According to researchers, once victims downloaded and launched the apps, the apps fetched a coin-mining JavaScript library. Adversaries did this by triggering Google Tag Manager (GTM) – a tag management system created by Google to manage JavaScript and HTML tags used for tracking and analytics on websites – in their domain servers.
“GTM is a legitimate tool that allows developers to inject JavaScript dynamically into their applications,” researchers said. “However, GTM can be abused to conceal malicious or risky behaviors, since the link to the JavaScript stored in GTM is https://www.googletagmanager[.]com/gtm.js?id={GTM ID} which doesn’t indicate the function of the code invoked.”
The mining script, Coinhive, then gets activated and begins using the majority of the computer’s CPU cycles to mine for Monero cryptocurrency. Researchers said that there is no mention of coin mining on the apps’ privacy policy or descriptions.
The cryptominer in question was made by Coinhive, a company that offers a Monero JavaScript miner to websites as a nontraditional way to monetize website content. Coinhive’s JavaScript miner software is often used by hackers, who secretly embed the code into websites or apps and then mine Monero currency by tapping the processing power of site visitors’ phones, tablets and computers.
Interestingly, researchers said the apps use shared domain name servers, and are likely published by the same developers using different names. The apps came from three developers: DigiDream, 1clean, and Findoo.
“Although we can’t get exact download or installation counts, we can see that there were almost 1,900 ratings posted for these apps. However, app ratings can be fraudulently inflated, so it is difficult to know how many users really downloaded these apps,” researchers said.
In addition to Microsoft, researchers reached out to Google, which removed the mining JavaScript from Google Tag Manager (hosted on the adversary’s domain). Moving forward, researchers said users can stay protected by paying close attention to CPU and memory usage of their computers or devices.
Cryptomining malware has turned into a top threat, according to a 2018 report– with attacks jumping higher than ransomware instances in the first quarter of 2018. In 2018, websites from the Make-A-Wish Foundation to the Los Angeles Times were discovered harboring cryptojacking code.
While the popularity of cryptojacking may not be a shock to the security industry, malicious cryptominers are increasingly using new sophisticated techniques. A March 2018 report by Kaspersky Lab highlighted how one cryptomining gang, tracked over six months, raked in $7 million with the help of 10,000 computers infected with mining malware.
Interested in learning more about mobile enterprise security threats and best practices? Don’t miss our free Threatpost webinar on Feb. 27 at 2 p.m. ET. Join Threatpost senior editor Tara Seals and a panel of mobile security experts, including Patrick Hevesi of Gartner; Mike Burr of Google Android; and David Richardson from Lookout. They’ll discuss the top evolving threats and risks that are unique to this work-from-anywhere environment; best practices for addressing them; and new challenges on the horizon, such as 5G services.










