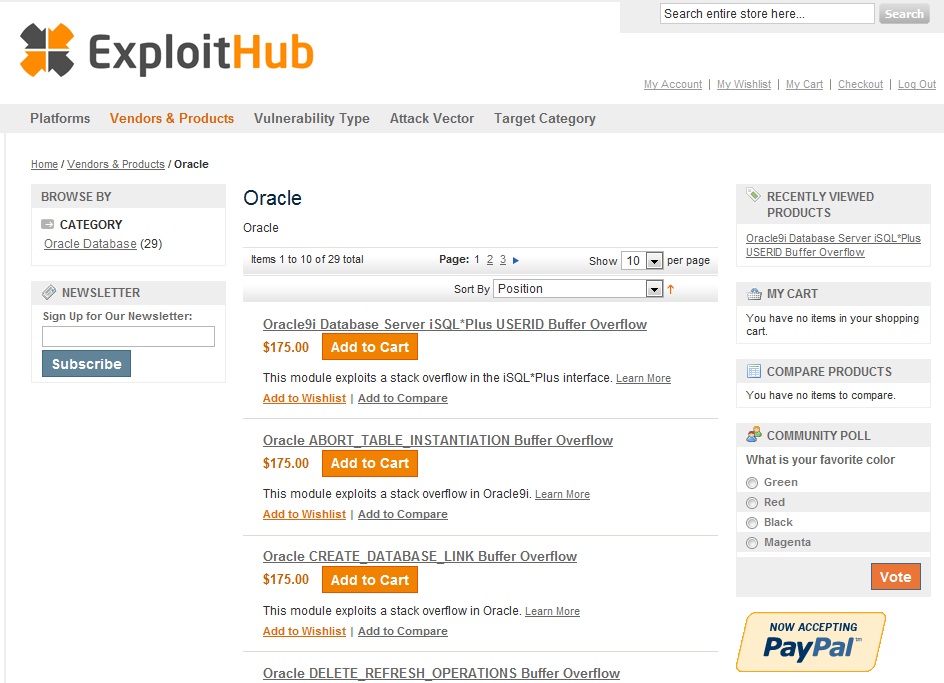
 It’s been tried before, but NSS Labs founder Rick Moy says his company’s new Exploit Hub – a store front for exploit code – can work. In an interview with Threatpost.com, he explains why the current market for exploits doesn’t work for the good guys, and why zero day exploits don’t help anyone. Exploit Hub is just the latest effort to create a viable, public marketplace for software holes and attacks. The new site is now public and accepting applications for those wishing to participate as buyers or sellers. The site is described as a “community-driven marketplace” for software exploits that will broker interactions between security researchers and “white hat” professionals interested in the fruits of their labor.
It’s been tried before, but NSS Labs founder Rick Moy says his company’s new Exploit Hub – a store front for exploit code – can work. In an interview with Threatpost.com, he explains why the current market for exploits doesn’t work for the good guys, and why zero day exploits don’t help anyone. Exploit Hub is just the latest effort to create a viable, public marketplace for software holes and attacks. The new site is now public and accepting applications for those wishing to participate as buyers or sellers. The site is described as a “community-driven marketplace” for software exploits that will broker interactions between security researchers and “white hat” professionals interested in the fruits of their labor.
It’s a great idea…but will it work? Above board markets for software vulnerabilities have been around for close to a decade, but previous efforts to market exploits have had mixed results. The business of selling exploits versus vulnerabilities is fraught with danger, and organizations like WabiSabiLabi have operated eBay style marketplaces for zero day exploits for years, but haven’t seen exploit writers beating a path to their door.
The need for an above-board marketplace that can compete with the black market surely exists, but getting it to work is another matter entirely.
To help answer questions about the new marketplace, Threatpost spoke with NSS Labs founder Rick Moy.
Threatpost: Explain what Exploit Hub is.
Rick Moy: Exploit Hub is a marketplace to promote vulnerability testing. Right now, there’s a key imbalance in the world. The bad guys know about tons of vulnerabilities, whereas the good guys have a fraction of the testing capability they need. So, when you have a vulnerability in a system, you can patch it or put a security product in front of it, or both. You need to know if the mitigations you take are effective.
Threatpost: Who is this service designed for?
Rick Moy: There are really multiple users for this service. Both enterprises and security vendors. Its quite costly for security vendors to keep up with developing these exploits just so they can build protections for them and enterprises don’t have access to more then 10 percent of what’s out there, so there’s no good way for them to do pen(etration) testing because they’re only testing a fraction of what’s broken.
Threatpost: OK. So how would they use Exploit Hub?
Rick Moy: Here’s an example: Penetration testing is mandated by PCI (The Payment Card Industry Data Security Standard). They might use the SANS Critical Security Controls to identify vulnerable, high risk systems in their network. They can then come to Exploit Hub to see which exploits are available to test against those vulnerabilities. They can purchase and run those against the network and determine whether the mitigations that have been put in place are effective or not.

Threatpost: How is this different from the Metasploit Framework?
Rick Moy: Metasploit is open source..the free version of it, anyway. You can think of it as a tool. There are around 800 free exploits that it uses. Most are not critical but there are a smaller number that are relevant and useful for folks. What you can do with Exploit Hub is run it on the Metasploit Framework. Core Security’s Impact and Immunity Inc.’s Canvas are great tools, also. But they suffer from a volume perspective.
We did a study. Over the last five years, if you look at CVSS (Common Vulnerability Scoring System) vulnerabilities with a rating of seven and higher that impact enterprises, there are around 15,000 vulnerabilities. Not all are present in everyone’s network, so you need to figure out what is in your network as a pen tester. Your job is to know which vulnerabilities constitute that organization’s attack surface and make sure their coverage and defenses — whether patch or security product — are adequate. You can put IPS in and it won’t really give you coverage. So the really best way for organizations to close the gap is to do their own pen testing.
But, using the tools available, you’re looking at exploits for maybe 1,000 high and critical vulnerabilities at best. They’re missing about 95% of the exploitable vulnerabilities. So we’re looking to fill the gap.
Exploit Hub will integrate with Canvas and Core ultimately, but we’re initially focusing on Metasploit Framework because its much more widely deployed than the other products. I’ve heard there are 100,000 users of Metasploit out there. Core just announced their 1,000th customer. So it’s a question of ‘How do we make the biggest impact?’
 Threatpost: Where will you get your exploits?
Threatpost: Where will you get your exploits?
Rick Moy: We’ve been talking with security researchers, enterprises, pen testing teams, everybody. There are a lot of folks who have developed exploits individually, but don’t have any way to market and monetize them. They’ve just been doing it in their spare time. A lot of IT folks and pen testers dabble in exploit writing. Its a hobby. They do it in their free time and don’t get paid. That’s hampering the industry. And when you’re buying a point product from companies you’re getting a specific view into things. We said ‘We need to have an industry of professionals. Its not enough to have individual companies addressing this. So let’s create a marketplace that everyone can contribute to.” There are resource constraints – it’s hard to find people to write these exploits. Right now, there’s not a decent place for security vendors to get this kind of information service. (Exploit Hub) can provide an AppStore type model.
Threatpost: And what is NSS’s role in all this?
Rick Moy: We’re just brokering it, like Craigslist. NSS will test the exploits and make sure they work. Legitimate pen testers are wary of going to a marketplace because its like a ‘box of chocolates’ – you never know which one you’re going to get. And they worry about back doors. If you just pull something down, how do you know it works. Some are written in PERL, some in C some in Python. Everything we’ll offer will be coded to work with the Metasploit Framework. Its an opportunity for the Core or Canvas guy, too. We’ll make what we have available as a feed to their products as well. We’re not trying to shut them out. But we can only do so much.
Threatpost: What’s the status of Exploit Hub now?
Rick Moy: We have the marketplace up and running internally and we’re going through QA (quality assurance). At this point, we have around 150 exploits – Oracle, Windows, Web browsers, client side exploits and things like that. IE zero days and the stuff used in Zeus? Nobody benefits from that. This will be non-zero day stuff. We’re providing the ability to test vulnerabilities that are disclosed so that organizations can patch or implement security products to close those holes. If there’s no remediation for an attack, because its a zero day vulnerability, there’s really no point for us to release that to people, because there’s nothing to do about it. We’re not in the game of providing tools to the bad guys. There’s no anonymous buying. This is an application where we go through and verify the ID and contact ID and bank account of the people buying it.









