Some iPhone users are vulnerable to having their devices automatically join rogue Wi-Fi networks because of a combination of an iOS feature that allows devices to reconnect to known networks and a directory of carrier-specific wireless network SSIDs that are preloaded into iOS, according to mobile security researchers from Skycure.
A number of operating systems, iOS among them, contain a convenience feature that allows devices to automatically connect to wireless networks with which they have connected in the past based on the SSID of those networks. Skycure cofounder and CEO Adi Sharabani said this feature is something of a security vulnerability in that an attacker can set up a malicious network with a SSID that mimics the SSID of a legitimate wireless network known to a specific device.
In order to exploit this vulnerability, an attacker would have to figure out the SSID of a network that has been accessed on the machine of a potential victim, create a malicious network spoofing that SSID, and then get close enough to the victim’s machine that it will connect to the malicious Wi-Fi network. Once a device is connected to a malicious network, an attacker can launch any number of man-in-the-middle related attacks.
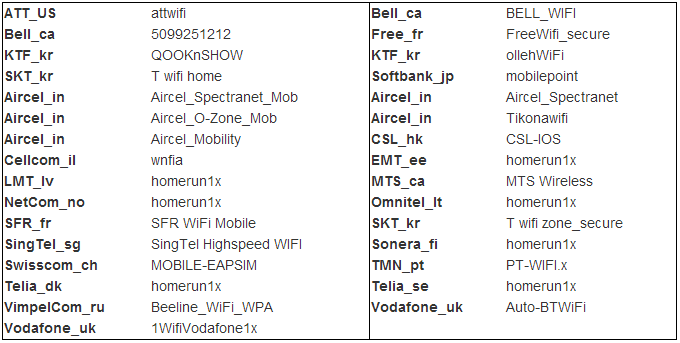
Sharabani claims that some cellular networks are pre-configuring bundles of wireless profiles onto iPhones – in addition to the ones that are built into the default iOS platform – before shipping them off to customers. In this way, customer devices can automatically connect to the wireless networks of the wireless carrier that issued the device. Unfortunately, this also means that an attacker can figure out the SSIDs that carriers and Apple are pre-loading onto their devices, spoof those SSIDs, and compel any number of devices to join malicious networks near them.
A Skycure spokesperson explained that carriers, AT&T for example, deploy Wi-Fi networks in their stores and at Starbucks. The SSID for these networks is “attwifi” and is preloaded into iOS. Despite this, it is not entirely clear why iOS and mobile carriers would have an incentive to preload these SSIDs onto iOS devices, but, according to Sharabani, the fact remains that these SSIDs are on the phones and the phones will connect to any wireless networks associated with them.
Skycure claims to have seen this vulnerability exploited in the wild at a coffee shop in Brooklyn. Apparently a pilot user of one of its mobile security products automatically connected to a malicious wireless hot spot with a SSID that mimicked that of a legitimate wireless carrier. Sharabani believes that the attackers were merely trying to social engineer users into joining what appeared to be a legitimate wireless network, and that they did not realize that certain wireless carriers are pre-configuring Wi-Fi SSIDs so that user’s devices can automatically connect to various wireless networks should they encounter them.