Few times have there been technologies so reviled and celebrated at the same time as Adobe Flash. Since its introduction as Macromedia Flash Player in the mid-’90s, the technology has helped shape what the web has become today. At the same time, few internet technologies have united so many wanting to kick it to the curb.
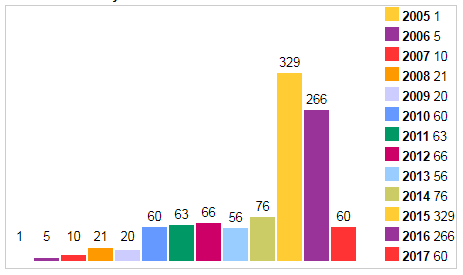
In 2020, in collaboration with Apple, Facebook, Google, Microsoft and Mozilla, Adobe will retire the much maligned Flash Player. A large part of the problem, experts say, despite progress in hardening its attack surface, is that it’s not secure enough. Flash continues to be a massive attack target that needs to go, they said. Since 2005, it has amassed 1,033 unique CVE entries, above, more than Microsoft’s Windows XP or Internet Explorer, according to CVEDetails.com.
“Given the sheer amount of time I’ve focused on Flash, I might get a little teary eyed when it’s finally gone,” said Jasiel Spelman, a senior vulnerability researcher with Zero Day Initiative.
Replacing it will be open standards such as HTML5, WebGL and WebAssembly. “These browser-based alternatives to Flash offer the same capabilities and functionalities. The trend is less helper apps and modern browsers with built-in capabilities that match those plugins of yesteryear,” Spelman said.
Gateway to Exploits, Malware
For more than a decade, the ubiquitous Flash Player has been a favorite target for attacks that attempted to trick users via a browser pop-up to install and run a bogus Flash Player that actually installed malware. Flash has been also abused by hackers who exploit vulnerabilities in the legitimate Flash Player to run malware. Its appeal has been that a single Flash exploit could target multiple browsers, since most of them were running the program.
Adobe Flash Player has offered hackers endless fertile ground for use in exploit kits, phishing schemes, zero-day attacks and backdoor programs, said Steve McGregory, research director at security firm Ixia. Most of those attacks lead to remote code execution because of a litany of vulnerabilities in legacy code leading to buffer overflows, or memory corruption issues. Its trail of carnage has included terabytes of lost intellectual property and industrial secrets, along with stolen passwords and credit card numbers.
For those reasons, technology leaders such as Alex Stamos, chief security officer for Facebook, declared in a 2015 tweet that has since been deleted: “It is time for Adobe to announce the end-of-life date for Flash and to ask the browsers to set killbits on the same day.”
Add to that Steve Jobs’ famous trashing of Flash in a longwinded 2010 manifesto explaining why Apple wouldn’t support it and arguing it should cease to exist.
“Adobe Flash has been heavily leveraged in advertising, media and eLearning spaces, but unfortunately Adobe has not kept pace with the necessary security updates in order to outweigh the benefits of using the product,” said Mark Butler, CISO for Qualys.
“If Flash wasn’t good enough for Steve Jobs to include in iOS software, it definitely shouldn’t be OK for us to use now. Flash has only increased in vulnerabilities since that time, and its patching cycles have lengthened,” he said.
Transition Challenge
Today, Adobe Flash security holes still dominate the threat landscape. So far this year there have been 60 unique CVEs associated with Flash, 53 rated high-severity allowing attackers to remotely execute code. Earlier this month Adobe patched a serious a local sandbox escape bug in its Flash Player after researchers failed to fix the bug completely in a previous patch.
However, despite indicators pointing to a swift death and depreciation of Flash over the next three years, the transition could present challenges for companies. Experts say dependence on Adobe Flash will create legacy issues similar to those of Windows XP.
“This is just the first step, once Flash is retired, we will all be facing the reality of older versions of Flash installed and being used without any security update support similar to what we have with Microsoft Windows XP. We all still have more work to do to make the retirement not just effective but safe,” said Christopher Budd, senior threat communications manager, Unit 42, Palo Alto Networks.

Percentage of users who have encountered at least one page w/ Flash Player content in a day. Courtesy Chromium.org
Three years ago, 80 percent of desktop Chrome users visited a site with Flash each day. Today usage is only 17 percent and continues to decline, according to Chromium, the open-source web browser project founded by Google.
Budd said the biggest issue with Flash after 2020 is the risk of security vulnerabilities affecting Flash with no patches available for those issues.
Zero Day Initiative’s Spelman says about 75 percent of the enterprise companies he works with are still dependent on Flash in some way. “We tell everyone that currently hosts Flash content that they should heed the guidance from Adobe and look to migrate to supported solutions. However, a number of those organizations have legacy Flash applications that can’t be disabled immediately because of dependency issues,” he said.
Enterprises’ Flash Problems Won’t Subside
There are no hard numbers on Flash usage inside and outside the enterprise. But, security experts say there are many firms that are using custom-built Flash applications that will be expensive to replace after the 2020 depreciation deadline.
“Similar to Windows XP end-of-life, there is going to be a time when there are Flash ‘forever day’ [vulnerabilities] that will be known, but just never patched by Adobe,” Spelman said. Those companies are going to have to redevelop those apps from scratch. “It’s going to take time and convincing them that finding a Flash replacement is a cheaper alternative to a security breach.”
For its part, Adobe stated in July it will “continue to support Flash on a number of major OSes and browsers that currently support Flash content through the planned EOL (end of life). This will include issuing regular security patches, maintaining OS and browser compatibility and adding features and capabilities as needed.”
In 2015, Adobe began the process when it announced that it had renamed Flash Professional CC to Animate CC and deemed it Adobe’s preferred tool for developing HTML5 content.
In the meantime, developer Juha Lindstedt reacted to Adobe’s end of life verdict for Flash and turned to GitHub to petition users there to save Adobe Flash. His goal is to convince Adobe to turnover its Flash code to the open-source community.
In his petition, Lindstedt calls Flash “an important piece of internet history and killing Flash means future generations can’t access the past. Games, experiments and websites would be forgotten.”
The petition has received mixed reviews within the software development and security communities. While some see Flash as bloated insecure code that needs to go away fast, others see handing it over to the open source community as a way to make it more secure and ensure that any legacy instances of Flash—after it sunsets—can be addressed with an emergency patch.
So far Lindstedt’s petition has garnered 6,650 digital signatures.
“I think it would be a great idea. Flash is already partially open source,” Spelman said. “From a preservation point of view, I think it would be important to save a snapshot of what the internet looked like when Flash was around.”
Adobe declined to comment for this story with the exception of stating it had no intention to make Adobe Flash open source. “I can tell you we don’t have any plans to do that at this time,” according to an Adobe spokesperson.