GitLab has awarded a total of $565,650 in security bug bounties to 171 researchers who reported valid vulnerabilities in the past year — and has announced the winners of its latest hacking contest.
GitLab, which started out as a web-based Git repository manager before moving into the DevOps lifecycle management space, launched its bug-bounty program one year ago this week, and according to Juan Broullon, senior application security engineer at the company, received a total of 1,378 reports from 513 white-hat hackers in that time.
“The program kept our engineers on their toes, challenged and surprised our security team, and helped us keep GitLab more secure,” Broullon wrote in a Thursday posting.
The program was launched on HackerOne, and “over the past year we’ve started tackling some early lessons learned and evolved the way we communicate with our reporters, the way we reward bounties, and even what we’re paying for high and critical severity findings,” Broullon wrote. The top reward is $20,000 for critical flaws.
Issue details are made public on GitLab.com 30 days after releasing a fix.
One of the more interesting bugs reported in the year is a command injection into Gitaly, a backend service, that led to remote code execution, according to senior application security engineer James Ritchey.
“Since the flaw was in a backend service, the reporter did a great job of finding the bug through code review and developing a very interesting way of exploiting it,” Ritchey told Threatpost. “The flaw itself was fixed quickly, but has led to a more comprehensive effort to proactively prevent similar flaws in the future.”
Two other reports (here and here) reflect how new features, in this case graphql, can reintroduce problems solved elsewhere in the codebase, he added.
“Both of these examples demonstrate how being an open-core, source-available product allows reporters to identify vulnerabilities quickly because they have the code available for review,” Ritchey said.
Hacking Contest Winners
The platform also runs bug-bounty contests. For the period October 1 through November 30 for instance it awarded prizes for a range of categories, resulting in 279 reports from 123 different individuals.
The categories included best-written report (won by @rpadovani, for Elasticsearch reports which were “consistently clear and concise”); most innovative report (won by @ngalog for a unique and creative technique used to disclose private data on GitLab Pages); and most impactful finding (won by @nyangawa of Chaitin Tech for a report on a complex path traversal bug which lead to remote code execution). Details on the bugs will be revealed after the 30-day disclosure period is up.
Hacker @xanbanx meanwhile won the most reputation points in the period, while @peet86 who had the highest reputation score for a new reporter to the program.
Bug Bounties Evolve
The high-velocity application- and process-development practices collectively known as DevOps has become a core goal for many enterprises, as they look to respond to market forces more dynamically – and GitLab is not the only company in the space to embrace bug bounties.
In January, Microsoft Microsoft began offering rewards of up to $20,000 for flaws in its Azure DevOps online services and the latest release of the Azure DevOps server. Azure DevOps is a cloud service launched in 2018 that enables collaboration on code development across the breadth of a development lifecycle.
Bug bounties are gaining steam across companies of all types, not just in DevOps, but researchers do have caveats and note that these programs are a work in progress.
“Bug-bounty programs encourage specialists to analyze third-party code and report their findings in an accurate manner,” Fausto Oliveira, principal security architect at Acceptto told Threatpost. “With the explosive growth of open source applications, there are too many threat surfaces to scan and address threats in code in a timely manner, especially in small organizations. Having the intelligence of the community looking at your code is an auxiliary measure that allows findings that would be otherwise missed. What needs to be done better is to incorporate those findings into open source code scanning tools that automate those findings and spread the benefit through the community.”
Ritchey admitted that one of the biggest challenges for triaged security bugs is tracking their progress and driving them to be fixed.
“They can easily get lost in the volume and noise,” he told Threatpost. “To help manage bugs in this state, our automation team has developed an escalation engine which tracks bugs progress and ensures they are properly triaged, scheduled, and are meeting our mean time to remediation (MTTR) goals outlined in our handbook page. This makes sure that all teams involved in the vulnerability lifecycle are actively notified when vulnerabilities are overdue, have insufficient labels, or need to be escalated. Without this automation, our small team would struggle to keep track of and manage flaws yet to be patched.”
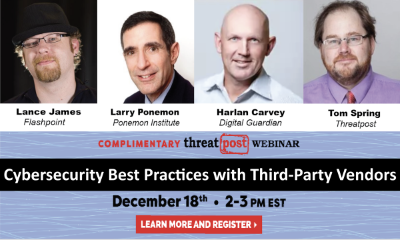
Free Threatpost Webinar: Risk around third-party vendors is real and can lead to data disasters. We rely on third-party vendors, but that doesn’t mean forfeiting security. Join us on Dec. 18th at 2 pm EST as Threatpost looks at managing third-party relationship risks with industry experts Dr. Larry Ponemon, of Ponemon Institute; Harlan Carvey, with Digital Guardian and Flashpoint’s Lance James. Click here to register.