 The attackers behind the insidious Koobface worm have taken to using Google Reader accounts that they control to spread the worm through shared Reader items. The infection method–which has been used before by Facebook worms–is another indication of the resilience and changing tactics the malware authors are employing.
The attackers behind the insidious Koobface worm have taken to using Google Reader accounts that they control to spread the worm through shared Reader items. The infection method–which has been used before by Facebook worms–is another indication of the resilience and changing tactics the malware authors are employing.
The attack takes advantage of the functionality in Google Reader that allows users to share content with other users. Reader is a free Google product that enables users to manage RSS feeds and and other content. One of Reader’s features gives users the ability to mark certain items to share with other Reader users.
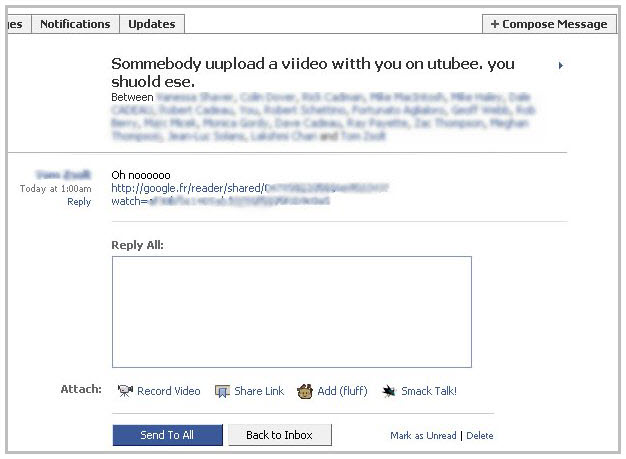
The Koobface authors are taking advantage of that by using Google Reader accounts that they control to host malicious URLs that point to the fake YouTube video that has been an integral part of the Koobface worm attack since its appearance last year, according to an analysis by Trend Micro. The company said that it has seen about 1,300 Google Reader accounts hosting the malicious URLs.
In 2008 the Koobface attackers employed the same method of infection, abusing the shared items function in Google Reader. Now, things have come full circle and the attackers are falling back on their old tricks again.









