LAS VEGAS – Multiple vulnerabilities in Canon’s DSLR camera firmware could allow an attacker to plant malware on devices and ransom images from users. The bugs, outlined in a session here at DEF CON, open the door to a range of hacks via a Wi-Fi network or a PC’s USB connection to a camera.

Eyal Itkin, researcher with Check Point ahead of a session at DEF CON titled “Say Cheese—How I Ransomwared Your DSLR Camera”
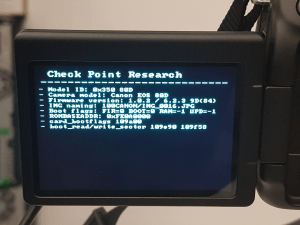
The research comes from Check Point that found six bugs when it reverse engineered Canon’s EOS 80D DSLR firmware. Eyal Itkin, the Check Point researcher giving the talk, said flaws were found in Canon’s implementation of Picture Transfer Protocol (PTP). PTP is an industry standard protocol used by device makers for transferring images via wired or wirelessly from a digital camera to a computer.
The researcher wrote, in a technical paper released Sunday, that PTP is a ripe target, given it is an unauthenticated protocol that supports dozens of different complex commands. “[A] vulnerability in PTP can be equally exploited over USB and over Wi-Fi,” he wrote.
During the DEF CON session, Itkin outlined two attack scenarios against the Canon EOS 80D model camera. One scenario included an attacker that takes over a PC, and can leapfrog an infection into a camera via a USB connection. The second attack involves placing a rogue Wi-Fi access point in a public setting to leverage a remote attack against the targeted camera.
The wireless attack is triggered when the camera connects to the rogue access point. “Once the attacker is within the same LAN as the camera, he can initiate the exploit,” the researcher said.
According to Check Point, its proof-of-concept attack builds off previous camera firmware research by Daniel Mende. In 2013, Mende gave a talk at the security conference Hack in The Box called “Paparazzi over IP.”
 “[Mende] demonstrated how he (mis)used the [PTP] protocol’s functionality for spying over a victim,” Check Point wrote. It was Check Point’s intent to find exploitable bugs, not just spy.
“[Mende] demonstrated how he (mis)used the [PTP] protocol’s functionality for spying over a victim,” Check Point wrote. It was Check Point’s intent to find exploitable bugs, not just spy.
“In our research we aim to advance beyond the point of accessing and using the protocol’s functionality,” Check Point said. “Simulating attackers, we want to find implementation vulnerabilities in the protocol, hoping to leverage them in order to take over the camera. Such a remote code execution scenario will allow attackers to do whatever they want with the camera. Infecting it with ransomware is only one of many options.”
One of the more sinister attack scenarios involved exploiting a bug (CVE-2019-5995) in the firmware that allows for a silent and malicious firmware update. “There is a PTP command for remote firmware update, which requires zero user interaction. This means that even if all of the implementation vulnerabilities are patched, an attacker can still infect the camera using a malicious firmware update file,” researchers wrote.
In all, researchers found six bugs (CVE-2019-5994, CVE-2019-5995, CVE-2019-5998, CVE-2019-5999, CVE-2019-6000 and CVE-2019-6001) allowing them to tamper with the DSLR camera firmware. But still, the researchers’ work was not done. Next, came planting the ransomware.
“Now that we are sure that all of our vulnerabilities indeed work, it’s time to start the real exploit development,” Itkin wrote.
The challenge of delivering ransomware to a DSLR camera wasn’t slight. But thanks to a meticulous reverse engineering of the firmware, researchers were able to take advantage of AES encryption, native to the firmware.
“[During the reverse engineering of the firmware] not only did we find the AES (encryption) functions, we also found the verification and decryption keys for the firmware update process,” researchers wrote.
“Because AES is a symmetric cipher,” they continued, “the same decryption keys can also be used for encrypting back a malicious firmware update and then signing it so it will pass the verification checks.” The simplified version is, researchers created their own malicious firmware update mechanism that allowed encrypting all images stored on the camera’s flash drive.
“The ransomware uses the same cryptographic functions as the firmware update process, and calls the same AES functions in the firmware. After encrypting all of the files on the SD Card, the ransomware displays the ransom message to the user,” Itkin said.
On Tuesday, Canon issued a security bulletin regarding six vulnerabilities tied to Check Point’s research. “Due to these vulnerabilities, the potential exists for third-party attack on the camera if the camera is connected to a PC or mobile device that has been hijacked through an unsecured network,” Canon wrote. “Do not connect the camera to a PC or mobile device that is being used in an unsecure network, such as in a free Wi-Fi environment,” it wrote.
Black Hat USA 2019 has kicked off this week in Las Vegas. For more Threatpost breaking news, stories and videos from Black Hat and DEF CON, click here.