For years, security experts, analysts and even users have been lamenting the state of desktop security. Viruses, spam, Trojans and rootkits have added up to create an ugly picture. But, the good news is that the desktop security battle may be over.
The less-than-good news, however, is that we may have lost it. Jeremiah Grossman, CTO of WhiteHat Security, wrote in a blog post Thursday that many organizations, particularly in the financial services industry, have gotten to the point of assuming that their customers’ desktops are compromised. And moving forward from that assumption, things don’t get much prettier.
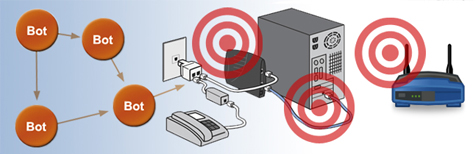
If we operate with this assumption, that the client is compromised (again
not unreasonable), then the good guys have ceded victory in the desktop
security battle. With over 1 billion people on the Internet, that is no
small loss. What’s worse is there are signs that the loss of the home
network could be permanent.
Botnets are starting to target and
infect routers and DSL modems. Scary, and a possible trend. Think about
what this could mean. Should this problem become pervasive, it
won’t matter if PCs are disinfected, swapped out, or replaced with
iPads, the bad guys are still control because they own the network
below. They’ll own DNS, the routers in between, and so on. There is
effectively little defensive countermeasures to protect home routers and
DSL modems, which are not exactly secure to begin with, or detect if
they’ve been compromised.
These are all reasonable assumptions based on real-world attacks that have been going on for some time now. Attackers have been targeting home networking equipment for a couple of years, using a combination of vulnerabilities in the firmware and hardware to get control of home users’ outbound Internet traffic. It’s an increasingly effective strategy for attackers looking to get control of large numbers of systems, without having to re-infect them regularly.
Most users would have no idea how to fix a compromised router or modem, if they were even able to tell it was infected in the first place. And the ISPs, cable companies and other providers have no interest–or expertise for that matter–in trying to identify and clean infected routers or modems. It’s not their business model.
It’s a bleak picture, but unfortunately, not an unrealistic one.