USB drives shipped with some IBM’s Storwize storage products are infected with malware, and the tech giant advises customers destroy the devices.
IBM would not comment on the source of the infection or where in the supply chain the interdiction happened, and instead referred Threatpost to an advisory. “There’s no additional statement at this time,” a spokesperson said.
IBM said the USB drives contain an initialization tool and the affected devices were shipped with IBM Storwize V3500, V3700 and V5000 Gen 1 systems.
The malware is a dropper detected by Kaspersky Lab as Reconyc. The dropper is a cybercrime tool used to install other malware on infected computers, primarily in Russia and India (37 percent and 17 percent respectively of all infections).
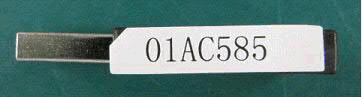
IBM said the infected drives have a part number 01AC585; Storwize systems with serial numbers starting with 78D2 are not affected, IBM said.
“Neither the IBM Storwize storage systems nor data stored on these systems are infected by this malicious code,” IBM said in its advisory, adding that other USB drives used for encryption key management are also not affected.
“When the initialization tool is launched from the USB flash drive, the tool copies itself to a temporary folder on the hard drive of the desktop or laptop during normal operation,” IBM said.
The malware is then copied with the initialization tool to the %TMP%\initTool temporary folder on Windows systems and the /tmp/initTool on Linux and Mac systems. “While the malicious file is copied onto the desktop or laptop, the file is not executed during initialization,” IBM said.
IBM said that any customers who have used the initialization drive on a Storwize systems should verify that their antimalware product has removed the infected file, or follow instructions in the advisory to remove the directory containing the file.
IBM advises that the USB drives be destroyed, or that customers delete the InitTool folder on the drive and download a new initialization tool package.
Supply chain interdiction is a tactic employed by nation-state actors to infect hardware with malware facilitating surveillance and data theft from critical systems. Most recently, a WikiLeaks dump of CIA hacking tools and documentation featured the NightSkies tools purpose-built for factory-fresh iPhones, indicating the agency’s ability to infiltrate Apple’s supply chain to install the surveillance tool.
In March, Check Point said it found more than three dozen Android handsets infected with adware, information-stealing malware, and ransomware pre-installed somewhere along the supply chain. The handsets belonged to Check Point customers who work for either a large, unnamed telecommunications company or an unnamed multinational technology company. The malware was added to the devices before they were in the users’ hands, and were not part of the vendor’s original ROM. For six of the devices, the attacker had system privileges for the device and the malware could not be removed without re-flashing the phone.