The attackers behind the raft of banker Trojans emanating from Brazil these days are continuing to refine their craft and learn new tricks. Their latest efforts have seen them going to greater lengths than ever to obfuscate their creations and hide their true functionality in order to evade detection and analysis by security software.
Malware authors have been using an arsenal of tricks and technologies for years to either make their programs look benign or simply help them slip past anti-malware software. In some cases this can mean changing a single byte in a new version of a virus, and in others it can go as far as using multiple packers, downloaders and shell programs to hide the malware.
Encryption has come into vogue in some malware circles, as well, and now the denizens of the Brazilian malware underground have taken to using crypto as a key element of their download-and-infection routines. Most banker Trojans have rather complicated download routines that involve redirecting the victim to a number of different obfuscated links before actually downloading the Trojan onto the victim’s machine. In many cases, the download happens in the background, without any real indication to the user about what’s going on.
Once the malware is on the machine, anti-malware products may detect it as a malicious file. But this process is much more difficult if the Trojan itself is encrypted.Dmitry Bestuzhev, a malware analyst for Kaspersky Lab in Latin America, has been following the evolution of Brazilian banker Trojans, and has noted a recent change in their sophistication.
A new (for Brazil) concept takes place between second and third stages
when the Trojan.Downloader downloads and installs the Banker. On the
one hand Brazilian coders obfuscate the download links using several
techniques and on the other hand
now they also crypt the Banker to be downloaded to the system.
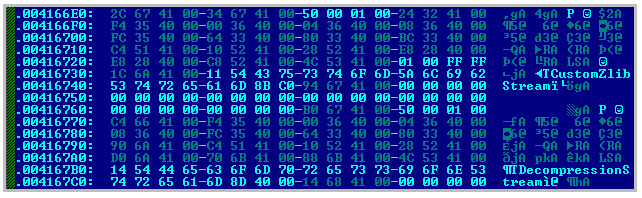
It’s a crypted (specially packed) PE file. The coders from
Brazil use this technique to prevent an automated malware analysis and
monitoring mode by AV companies. This sample downloaded as it is on the
server won’t be functional on the user machine unless
it’s decrypted. The decryption mechanism in this case is
included into the initial Trojan.Downloader, which first downloads
malware, and then decrypts it to be able to infect the user machine:
Once decrypted, the malware then begins its final infection routine, planting the banker Trojan itself on the machine. From there, it’s open season on the victim’s sensitive data.
Banker Trojans have become one of the main exports of the Brazilian underground in recent years, thanks to a fairly lax legal environment regarding computer crime and a high penetration of online banking. Attackers have taken advantage of this situation and spent the last couple of years honing their skills and designing complex pieces of malware that target customers of each specific bank.
In many cases, the attackers use shared hosting or bulletproof hosting services to store their malware tools. They often attack legitimate Web sites as well, planting malicious code on the back-end servers and then using drive-by download techniques to compromise visitors to those sites. Once the banker Trojan is on a victim’s machine, it not only steals sensitive financial information, it likely also will kill any security software and anti-malware software running on the PC and look for credentials for social networking sites such as Orkut or Facebook.









