A simple, yet effective, worm is now circulating o n some jailbroken iPhones, changing settings on the phones and terminating some services. The worm, which was discovered Sunday, doesn’t appear to be too malicious, but is an indicator of what might lie ahead for owners of iPhones and other smartphones.
n some jailbroken iPhones, changing settings on the phones and terminating some services. The worm, which was discovered Sunday, doesn’t appear to be too malicious, but is an indicator of what might lie ahead for owners of iPhones and other smartphones.
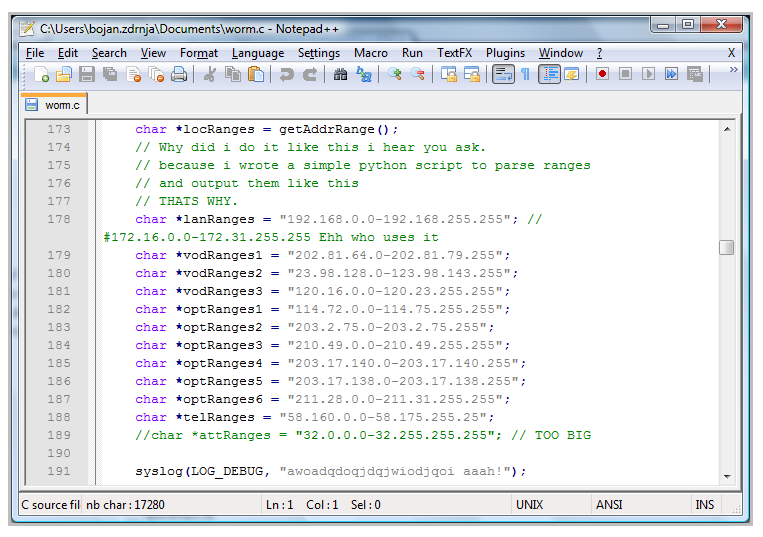
The worm, called iKee, infects jailbroken iPhones by utilizing the SSH service on the phones, which uses the default password and allows remote logins. The worm takes several actions after infecting a phone, including changing the phone’s background image to a photo of Rick Astley, shutting off the SSH service and then copying itself to the iPhone. The iKee worm also scans the available 3G network for a specific set of IP addresses, which an analysis by the SANS Internet Storm Center shows all belong to 3G customers in Australia.
There was a somewhat similar worm that surfaced last week, attacking iPhone users in the Netherlands and demanding a small payment in order to disinfect the iPhone.
Jailbroken iPhones give the owner the ability to run applications that have not been approved by Apple, which has kept a tight watch on what apps can run on the iPhone through its App Store. Only apps that have been approved Apple can be added to the App Store, which has both free and paid apps. But there are thousands of unapproved apps available, as well, and owners who have jailbroken their iPhones can run those if they’re willing to accept the risk of malware or other undesirable features.
Security experts have said that malware targeting the iPhone, one of the more popular handsets in the world right now, was a matter of when, not if, and the appearance of iKee and the Netherlands Trojan are just the first examples of this. The iPhone is one of the more advanced mobile platforms, including a full Web browser and a slew of other features that give it the power of a desktop PC. But with that power also comes an increased attack surface area and more features to exploit.
Security researchers have demonstrated a number of attacks against the iPhone, including SMS-based attacks and others that exploit the iPhone’s Safari browser implementation.
*Image from The SANS ISC.
*iPhone composite image via adactio‘s Flickr photostream









