UPDATE
An extremely high number of keylogger phishing campaigns have been seen tied to the Zoho online office suite software; in an analysis, a full 40 percent spotted in the last month used a zoho.com or zoho.eu email address to exfiltrate data from victim machines.
A Cofense analysis, published Tuesday, of popular keylogging malware – which records user imputs in real-time to find passwords and other information – found that cybercriminals are abusing Zoho in two ways. One is by creating bogus, free accounts, and using these to receive emails from their malware containing the stolen data from the keylogger. Secondly, attackers in some cases are using stolen accounts to facilitate this same data exfiltration.
Darrell Rendell, principal intelligence analyst at Cofense, told Threatpost that Cofense researchers were able to confirm the activity on Zoho by intercepting the malware’s SMTP (Simple Mail Transfer Protocol) traffic.
“We are able to see it connecting to smtp.zoho.com; and because smtp.zoho.com allows the STARTTLS function (encrypting the network traffic), we must use special techniques to intercept the traffic and decrypt it,” he explained. “We can also confirm the contents of the messages being sent to Zoho by parsing the malware’s memory. Either way, the result is an email containing harvested keystrokes, base64 encoded screenshots, stolen passwords and browser histories, to name examples.”
Zoho has become popular with cybercriminals for a few reasons, starting with the simple fact that it’s a free and popular cloud service.
“They’re a software-as-a-service (SaaS) solution, and as we’ve seen cloud-based organizations are a major target for threat actors because of the sheer number of, and variance in, their end-user demographics,” Rendell told us. “For example: If a platform has 30 million+ users, even if a tiny fraction of a percent have their accounts compromised, it generates a huge command-and-control footprint for the threat actors.”
Additionally, by not enforcing strict security features such as multifactor authentication, and with loose controls around account creation, it creates additional risk exposure, according to the researcher.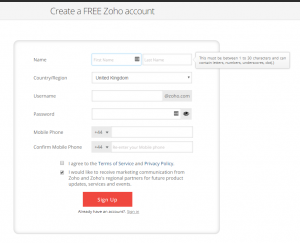
“The risk boils down to this: The ease in which a threat actor can automate account creation, and [Zoho] not providing or enforcing strict security controls on their accounts such as multi-factor authentication, thus enabling easy and sustained takeover,” Rendell told Threatpost. “A somewhat simple script, for example, could potentially provide an attacker the ability to fully automate account creation in this type of scenario.”
On Sept. 25, India-based Zoho’s domain was taken down briefly by its registrar, TierraNet, following reports of phishing originating from one of Zoho’s services.
Threatpost reached out to Zoho about the platform abuse. CEO Sridhar Vembu told us that the company is “clamping down heavily” on the issue and is exploring various heuristics and algorithms to help with the problem. Also, the company has implemented now policies, he noted:
And indeed, Zoho shouldn’t necessarily be singled out as a target for abuse, Rendell pointed out.
“Despite being subject to media scrutiny and aggressive registrar actions, Zoho is hardly the only victim of platform abuse,” he said in a blog post on the analysis, posted Tuesday. “Many trojans and keyloggers have abused popular platforms to support credential theft. The Geodo malware…leverages stolen credentials across hundreds of platforms – SaaS, ESPs and private mail servers alike. Gmail, Outlook.com, Yandex and Yahoo are frequent victims.”
Meanwhile, the analysis also shows a rise in the use of keyloggers by crooks – specifically Agent Tesla and Hawkeye.
“This seems to coincide with a real explosion of the malware-as-a-service model,” Rendell told us. ” By abstracting away all of the difficult parts of malware – namely its authorship and subsequent configuration – it is trivial for utterly non-technical actors to purchase an off-the-shelf keylogger, ready to deploy. With phishing-as-a-service also in existence, it’s possible for would-be attackers to get end-to-end malware delivery without having to so much as run a single command.”
Agent Tesla and Hawkeye also have both added “stealer” capabilities to their portfolios.
“This noxious mix of capabilities gives these families the ability to capture data both in real-time and retroactively, from vaults, wallets, caches and configs,” Rendell said. “Naturally, this begs the question: once the data has been stolen, serialized and prepared, where does it go? Either to a panel or, more commonly, to a compromised email account…keyloggers overwhelmingly favor email to all other exfiltration methods combined.”
This post was updated on Oct. 3 at 10:47 ET, with comments from Zoho’s CEO.











