 The main site for the PHP-Nuke content management system software has been compromised and is serving malicious iFrame exploits to visitors.
The main site for the PHP-Nuke content management system software has been compromised and is serving malicious iFrame exploits to visitors.
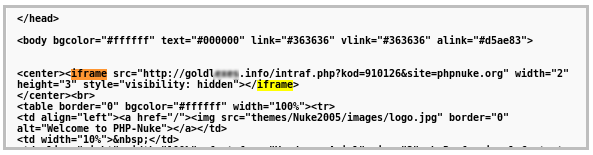
Researchers at Websense found that the phpnuke.org site is currently serving several different exploits. The attack uses the common iFrame-redirection technique to hijack users’ browsers and send them off to a malicious site. The code on that site is highly obfuscated and contains exploits for three separate vulnerabilities, two in Internet Explorer and one in Adobe Reader.
The first attack tries to exploit a four-year-old flaw in Internet Explorer. If that part of the attack works, it downloads a Trojan onto the victim’s machine. The malware then tries to connect to several Web sites, the researchers said.
The second attack uses a Java exploit, which ends up with the same infection routine as the first one.
The third exploit is a PDF exploit — this actually merges three
exploits targeting Adobe Reader. First the JavaScript in the HTML page
checks if Adobe Reader is exploitable by checking its version number.
The version should be between 7 and 7.1.4, 8 and 8.1.7, or 9 and 9.4.
When a vulnerable version is found, the exploit downloads the malicious
PDF file and as it is loaded by Adobe Reader, the malicious ActionScript
in the file is executed automatically. The PDF itself contains an
obfuscated ActionScript that utilizes one of the three different PDF
exploits it hides. These are CVE-2009-4324,
CVE-2007-5659,
and CVE-2009-0927.
If it succeeds, the download and installation of updates.exe
happens in a similar manner to that described earlier.
The Websense report says that the exploit is still active on the PHP-Nuke site right now. PHP-Nuke originally was an open-source platform, but is now a commercial product. The main site, however, still serves as a resource page for users and developers.









