 Although Adobe doesn’t have a patch ready yet for the newly disclosed vulnerability in the company’s Reader application, Adobe and Microsoft security officials said that Microsoft’s recently released Enhanced Mitigation Environment Toolkit 2.0 can protect users against the exploit that is currently circulating.
Although Adobe doesn’t have a patch ready yet for the newly disclosed vulnerability in the company’s Reader application, Adobe and Microsoft security officials said that Microsoft’s recently released Enhanced Mitigation Environment Toolkit 2.0 can protect users against the exploit that is currently circulating.
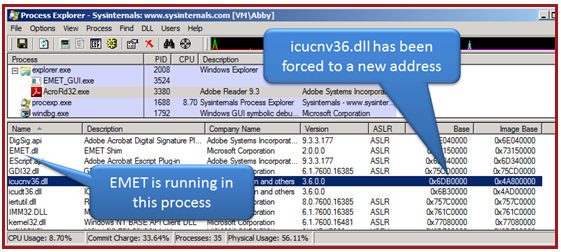
The EMET toolkit is designed to enable users to add exploit mitigations such as ASLR (Address Space Layout Randomization) and DEP (Data Execution Protection) to applications that previously didn’t include them. Microsoft and Adobe said on Friday that EMET can protect users against attacks against the current zero day flaw in Reader by forcing a specific DLL into using ASLR. That moves the address where the DLL is located from a previously predictable location to a random address, preventing the current exploit from working.
From Microsoft’s blog post on using EMET to defeat the Reader exploit:
The good news is that if you have the Enhanced Mitigation Experience Toolkit 2.0 (EMET) enabled for AcroRd32.exe, it blocks this exploit. This is happens thanks to two different mitigations:
Mandatory ASLR:
On Windows 7, Windows Vista, Windows Server 2008 R2, and Windows Server
2008 this mitigation will force the relocation of non ASLR-aware DLLs.
The exploit will then fail to use ROP successfully since it is expecting
the DLL to be at a predictable location. Take a look at the below screenshot from Process Explorer to see what this looks like.
Export Address Table Access Filtering (EAF): The exploit is also blocked by the EAF mitigation. This
is important for Windows XP and Windows Server 2003 because they do not
support mandatory ASLR. With this mitigation in place EMET will detect
the shellcode accessing the EAT of Kernel32.dll trying to resolve some
APIs (e.g. LoadLibraryA). EMET will then raise a
STATUS_STACK_BUFFER_OVERRUN unhandled exception and the program will be
terminated before the shellcode does anything bad.
Adobe has not specified when it will release a patch for this flaw, which is a stack buffer overflow in Reader. IN the meantime, the deployment of EMET is a good option on systems that need to have Reader installed.









