The ransomware gang known as “Cuba” is increasingly shifting to exploiting Microsoft Exchange vulnerabilities – including ProxyShell and ProxyLogon – as initial infection vectors, researchers have found.
The group has likely been prying open these chinks in victims’ armor as early as last August, Mandiant reported on Wednesday.
Mandiant, which tracks the threat actor as UNC2596, noted that the group deploys the COLDDRAW ransomware. In fact, Cuba may be the only group that uses COLDDRAW: At least, it’s the only threat actor using it among those tracked by Mandiant, “which may suggest it’s exclusively used by the group,” researchers said.
Cuba Has Rated an FBI Warning
In a December flash alert, the FBI attributed a spate of attacks – on at least 49 U.S. entities in the financial, government, healthcare, manufacturing and information-technology sectors – to the group. For what it’s worth, Mandiant hasn’t seen Cuba attacking hospitals or other entities that provide urgent care.
At the time, the FBI noted that the Cuba ransomware is distributed using a first-stage implant that acts as a loader for follow-on payloads: the Hancitor malware, which has been around for at least five years.
This isn’t the first time that Cuba has shown a taste for Exchange vulnerabilities, either. They’re just one way that Hancitor operators gain initial access to target machines: Other avenues include phishing emails, and the exploitation of compromised credentials or legitimate Remote Desktop Protocol (RDP) tools, according to the FBI’s December alert.
Microsoft Exchange Action
True to form, Mandiant observed the group “frequently” picking apart vulnerabilities on public-facing Microsoft Exchange infrastructure as an initial compromise vector. “The threat actors likely perform initial reconnaissance activities to identify internet-facing systems that may be vulnerable to exploitation,” researchers said.
Next, Cuba deployed webshells to establish a foothold in the compromised network. Then, the actors planted backdoors to establish a foothold, including the publicly available NetSupport RAT, as well as BEACON and BUGHATCH, which have been deployed using the TERMITE in-memory dropper.
The operators have mainly used credentials from valid accounts to escalate privileges, researchers noted. It’s not always clear where they got the credentials from, but at least in some cases, they were stolen with credential-stealing tools such as Mimikatz and WICKER.
“We have also observed these threat actors manipulating or creating Windows accounts and modifying file access permissions,” researchers added. In one intrusion, the threat actor created a user account and added it to the admin and RDP groups, they said.
Infection Chain
In order to identify active network hosts to potentially encrypt and files to exfiltrate, Cuba has used WEDGECUT, a reconnaissance tool, which sends PING requests to a list of hosts generated by a PowerShell script that enumerates the Active Directory.
Then, the crooks peek around to see what files might be of interest. They also routinely use a script to map all drives to network shares, “which may assist in user file discovery,” researchers noted.
Cuba threat actors have used several methods for lateral movement, including RDP, SMB, and PsExec, “frequently using BEACON to facilitate this movement,” Mandiant said. Then they deploy various backdoors, including NetSupport, as well as BEACON and BUGHATCH, which are often deployed using the TERMITE in-memory dropper.
To finish up their extortion work, the gang tries to steal files and encrypt networked machines, threatening to publish to the shaming site exfiltrated data belonging to organizations that balk at paying ransom.
More Tools, More Malware
According to Mandiant’s report, Cuba is using webshells to load the TERMITE dropper: a password-protected, memory-only dropper with an encrypted shellcode payload. The payloads have included BEACON malware, the Metasploit stager or the group’s custom BUGHATCH downloader.
Cuba isn’t the only threat actor using the TERMITE dropper: Mandiant said that it’s apparently used by “a limited number” of threat actors.
Over the course of six months, collected TERMITE payloads show that its keepers have been grooming TERMITE, tweaking it so as to better burrow in and evade detections, researchers said.
Custom-Rolled Malware & Tools
Beyond common, mainstay malware tools such as Cobalt Strike and NetSupport, Mandiant’s analysis showed that Cuba has some novel malware up its sleeve, including:
BURNTCIGAR: a utility that terminates endpoint security software.
WEDGECUT: a reconnaissance tool that checks to see whether a list of hosts or IP addresses are online.
BUGHATCH: a custom downloader that receives commands and code from a command-and-control (C2) server to execute on a compromised system.
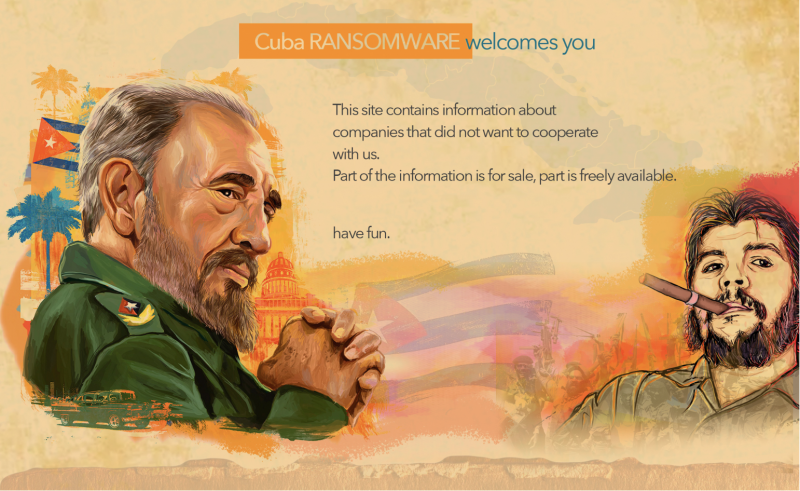
The researchers noted that when COLDDRAW was deployed, Cuba used what they called “a multi-faceted extortion model” – i.e., besides encrypting data, the gang leaked it on the group’s shaming site, which is depicted below in all its cigar-chomping glory.
Who Does Cuba Love the Best?
The majority – 80 percent – of organizations victimized by Cuba are based in North America, but Cuba loves the United States more than anywhere. As shown by the victim map below, the United States is Cuba’s favorite target, followed by Canada, though the group does go after European countries and other regions.
Its favorite industry sector to pick on is manufacturing, followed by financial services.
With regards to the victims listed on its shaming site – which the gang has had up since only early 2021 – Cuba provides a victim list for free, but it also keeps a separate list that you have to pay to see. Mandiant bit the bullet and sprang for that paid section.
It was sparse, to say the least: “[The] paid section … listed only a single victim at the time of publication,” its report said.
Moving to the cloud? Discover emerging cloud-security threats along with solid advice for how to defend your assets with our FREE downloadable eBook, “Cloud Security: The Forecast for 2022.” We explore organizations’ top risks and challenges, best practices for defense, and advice for security success in such a dynamic computing environment, including handy checklists.