Attackers could have stepped through a yawning security hole in the Microsoft Teams chat service that would have let them masquerade as a targeted company’s employee, by reading and sending email on their behalf.
On Monday, Tenable’s Evan Grant explained in a post that he found the bug in Microsoft Power Apps: A platform for low-code/no-code rapid app development.
Exploitation would require a lot of moving parts. But the bug is a simple one, having to do with insufficient input validation, and it packs a nasty punch. Grant said that the vulnerability could have been leveraged to establish persistent read/write access to a victim’s Microsoft bubble, including email, Teams chats, OneDrive, Sharepoint and a variety of other services.
Such attacks could be carried out via a malicious Microsoft Teams tab and Power Automate flows, Grant explained. Microsoft has since fixed the bug, but Grant’s post analyzed how it might have been exploited.
A BEC Fraudster’s Delight
Grant set up a hypothetical scenario in which an attacker – whom he called baduser(at)fakecorp.ca, a member of the fakecorp.ca organization – can create a malicious Teams tab and use it to “eventually steal emails, Teams messages and files from gooduser(at)fakecorp.ca, and send emails and messages on their behalf.”
It would be a “fairly serious” attack, Grant said, given that unbridled access to employees’ emails and the ability to put on the guise of authentic, trusted employees is exactly what fuels business email compromise (BEC), for one.
In a BEC attack, a scammer impersonates a company executive or other trusted party and tries to trick an employee responsible for payments or other financial transactions into wiring money to a bogus account. Attackers usually conduct a fair amount of recon work, studying executive styles and uncovering the organization’s vendors, billing system practices and other information to help mount a convincing attack.
As of last October, BEC fraudsters were operating out of bases in at least 39 countries and causing $26 billion (and growing) in losses annually.
Attackers could also have ripped off potentially sensitive information such as corporate documents; personally identifiable information (PII); or anything, really, that’s sent via chat, email, or on a shared OneDrive or Sharepoint.
Step One: Malicious Microsoft Teams Tab
The video below shows how the method would be used by an attacker – “Bad User” – to steal a Word document from a victim’s (“Good User’s”) private OneDrive for Business.
As Grant detailed, Microsoft Teams has a default feature that allows a user to launch small apps as a tab in any team they belong to. If a given user is part of an Office 365/Teams organization with a Business Basic license or above, they can also access a set of Teams tabs that consist of Microsoft Power Apps applications.
Power Apps are just a subset of the wider Microsoft Power Platform. When a user launches their first Power App tab, it creates what Microsoft calls a “Dataverse for Teams Environment,” which Microsoft says is used to store, manage and share team-specific data, apps and flows.
Besides such team-specific environments, there’s also a default environment for the organization as a whole. That’s key to exploiting the bug, since users can only create connectors and flows in either the default environment or for teams that they own. To exploit this bug, an attacker needs to be able to create flows in Power Automate.
The Power Automate service enables creation of automated workflows – for example, setting up a schedule to send emails or to send alerts whenever a SharePoint file is updated – and can operate on data within Office 365.
When first created, Power App tabs gather information from the make.powerapps.com domain to install the app. Teams tabs generally open an iFrame to a page that the app’s manifest lists as a trusted domain.
Question: Could the apps.powerapps.com page be tricked into loading an attacker’s content?
Answer: Yes indeed.
“Trying to load any url which doesn’t begin with https://make.powerapps.com results in the makerPortalUrl being set to an empty string,” Grant elaborated.
That’s where insufficient validation comes in, he said: “However, the validation stops at checking whether the domain begins with make.powerapps.com, and does not check whether it is the full domain. So, if we set makerPortalUrl equal to something like https://make.powerapps.com.fakecorp.ca/ we will be able to load our own content in the iframe!”
The request to define what page is loaded by a tab can be seen when adding a new tab or even renaming a current tab.
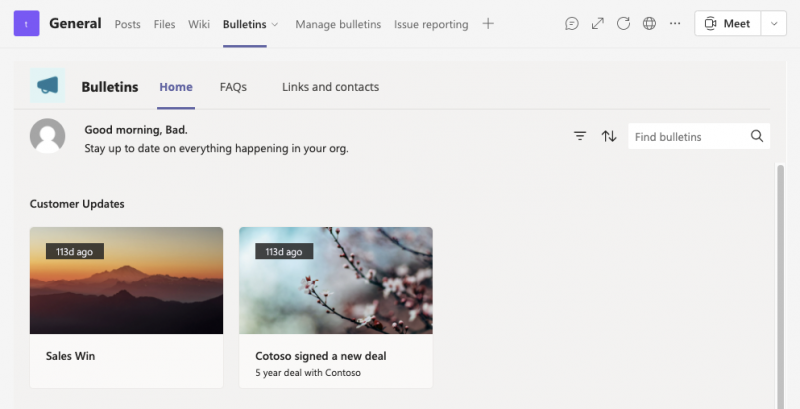
To sneak in malicious content, Tenable researchers pointed a PUT request to the Bulletins Power App that was installed in their team environment. To point the tab to malicious content, the team simply replaced that URL with its apps.powerapps.com/teams/makerportal?makerPortalUrl=https://make.powerapps.com.fakecorp.ca page.
Granted noted that “This only works because we are passing a URL with a trusted domain (apps.powerapps.com) according to the application’s manifest. If we try to pass malicious content directly as the tab’s URL, the tab will not load our content.”
Step Two: Stealing Tokens
Just being able to load an iFrame with malicious content two iFrames deep in a Teams tab would only get an attacker so far. However, not all tabs are created equal. For Power App extension tab types, the app.powerapps.com page communicates both with Teams, by way of the Teams JS SDK, as well as its child iFrame using javascript postMessage, according to Grant’s post.
The researcher used a Chrome extension to observe the postMessages passed between windows as an application is installed and launched.
“At first glance, the most interesting message is a postMessage from make.powerapps.com
in the innermost window (the window which we are replacing when specifying our own makerPortalUrl) to the apps.powerapps.com window, with GET_ACCESS_TOKEN in the data,” he said. “The frame which we were replacing was getting access tokens from its parent window without passing any sort of authentication.”
Using this type of postMessage from the make.powerapps.com.fakecorp.ca subdomain, Grant and his team were able to steal access tokens. “A handler is registered in the WebPlayer.EmbedMakerPortal.jsfile loaded by apps.powerapps.com which fetches tokens for the requested resource using the https://apps.powerapps.com/auth/onbehalfof endpoint.”
Tenable’s testing showed that this endpoint can grab tokens for:
apihub.azure.com
graph.microsoft.com
dynamics apps subdomains
service.flow.microsoft.com
service.powerapps.com
The Trickery a Hijacked Tab Can Pull Off
This is “a super exciting thing to see,” Grant said: “A tab under our control which can be created in a public team can retrieve access tokens on behalf of the user viewing it.”
As a quick proof of concept (PoC) , the researchers focused on grabbing the service.flow.microsoft.com token by hosting a page and overwriting a tab to point to it. They sent the token to another listener they controlled while also loading the original Power App in an iFrame that matches the tab size.
“While it won’t look exactly like a normally-running Power App tab, it doesn’t look different enough to notice,” according to the writeup. “If the application requires postMessage communication with the parent app, we could even act as a man-in-the-middle for the postMessages being sent and received by adding a message handler to the PoC.”
Theservice.flow.microsoft.comtoken was a deliberate choice, in that it can be used to gain access to yet more tokens and to create Power Automate flows, which allowed the researchers to access a user’s email from Outlook, Teams messages, files from OneDrive and SharePoint, and “a whole lot more,” Grant wrote.
The researchers showed pieces of a PoC that creates:
- Office 365 (for Outlook access), and Teams connectors,
- A flow that let them send emails as the user, and
- A flow that enabled them to get all Teams messages from channels the victim is in and to send messages on their behalf.
There are more moving parts, but the TL;DR table below shows the malicious actions the malicious tab performs on opening.
How a Small Bug Can Take a Big Bite
Granted, the exploit entails a “long and not-quite-straightforward attack,” according to the writeup. But the potential impact of such an attack “could be huge, especially if it happens to hit an organization administrator.
“That such a small initial bug (the improper validation of themake.powerapps.comdomain) could be traded-up until an attacker is exfiltrating emails, Teams messages, OneDrive and SharePoint files is definitely concerning,” he continued. “It means that even a small bug in a not-so-common service like Microsoft Power Apps could lead to the compromise of many other services by way of token bundles and first party logins for connectors.
“So if you happen to find a small bug in one service, see how far you can take it and see if you can trade a small bug for a big impact” he concluded. “There are likely other creative and serious potential attacks we didn’t explore with all of the potential access tokens we were able to steal. Let me know if you spot one.”
End users don’t have to take any actions: Microsoft has already implemented a solution.
Join Threatpost for “Tips and Tactics for Better Threat Hunting” — a LIVE event on Wed., June 30 at 2:00 PM ET in partnership with Palo Alto Networks. Learn from Palo Alto’s Unit 42 experts the best way to hunt down threats and how to use automation to help. Register HERE for free.