Researchers have identified a wave of new business email compromise campaigns targeting Fortune 500 companies that are designed to trick victims into fraudulent wire transfers.
Researchers said the campaigns originate from Nigeria and are targeting companies in the retail, healthcare and financial markets.
The Nigerian-based business email compromise (BEC) campaigns were highlighted by IBM X-Force in a report released Wednesday. Researchers there said the Nigerian BEC campaigns are representative of an overall BEC trend it has observed where attacks have been highly sophisticated and on the rise since the fall of 2017 – sometimes costing victims millions of dollars.
“Although BEC scams are not new, the examples described here detail how attackers used stolen email credentials and sophisticated social engineering tactics without compromising the corporate network to defraud a company,” according to the X-Force report.
The attacks, which are based mostly on phishing and social engineering, are attractive for cyber criminals because they are relatively simple – the attacker will take over or impersonate a trusted user’s email account, and target companies that conduct international wire transfers.
In the most recent BEC attacks, researchers said adversaries first send mass phishing emails to hundreds of internal and external contacts within a business in order to eventually gain access to a user’s email credentials.
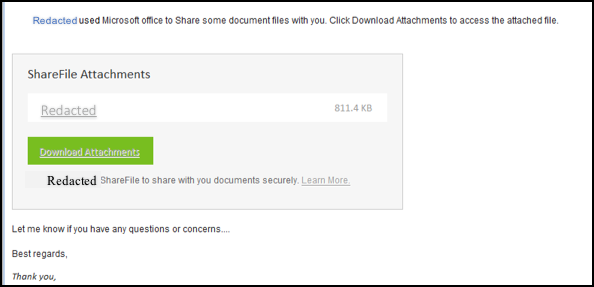
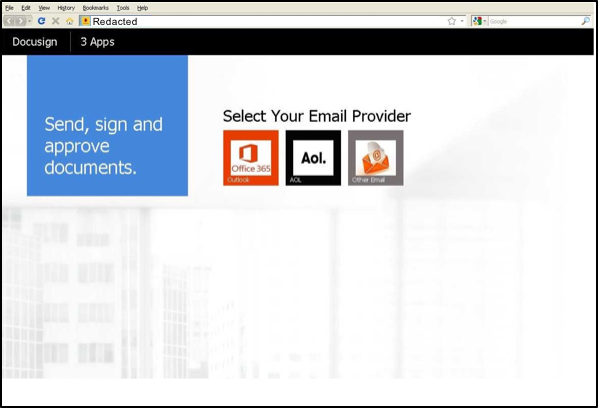
These emails, which use publicly available company information to look believable, contain an attached link that looks like a business document, which then redirect victims to a fraudulent DocuSign portal. From there, the portal requests the target authenticate using their email provider or business user credentials.
Neither the email nor the fraudulent “DocuSign” portals contain malware that is downloaded onto the user’s machine. This allows attackers to avoid the need to plant credential-stealing malware that might set off alerts by traditional detection tools and spam filters.
“Since the user’s Office 365 accounts were not protected with multi-factor authentication, the attackers were able to directly log into their accounts without compromising the organization’s internal network. They were able to create inbox rules configured to delete messages with certain words in the subject or body and messages from particular senders,” Sean Cavanaugh, senior incident response analyst at IBM X-Force, told Threatpost.
Once attackers gained access to user credentials, they were able to access businesses’ email web portals, where they could then look through activities in the compromised emails and hone in emails to Accounts Payable personnel who had access to wire transfer payments.
“The attacker’s thoroughness during reconnaissance and while financial conversations took place has involved such actions as impersonating victims, finding and spoofing internal documents needed to make legitimate wire transfers, and setting up multiple domains and emails to pose as higher-level authorities,” according to the X-Force report. “The attackers created a false sense of reality around the target and imparted a sense of urgency to pay, resulting in successful scams involving millions of dollars.”
From there, the attackers would send communications to the target directly from a compromised email address, carefully impersonating either vendors of a client or higher level authorities within the business. The attackers specifically targeted personnel involved in the organization’s accounts payable departments, because they had access to the company’s bank accounts.
In order to make email conversations seem more legitimate, attackers could go as far as to create mail filters so that communications were conducted only between the attacker and victim, and in some cases to monitor a compromised user’s inbox.
According to X-Force, the threat groups operating these scams are likely based in Nigeria, as that is where the IP addresses used to log into email web access portals are traced back to.
The threat groups, which are of an unknown size, appear to have used a “phishing kit to develop spoofed DocuSign login pages for over 100 compromised websites,” researchers said.
Protecting Against BEC Scams
Business email compromise campaigns are nothing new – the scams are popular because they involve little to no technical knowledge, malware, or special tools for cyber criminals. Despite that, BEC scams are becoming costlier to impacted victims – a recent report predicts that BEC attacks will result in over $9 billion in losses in 2018, up from $5.3 billion at the end of 2016.
“BECs are still successful and stealing millions from organizations and many aren’t aware until it’s too late. Organizations need to focus on implementing technical controls to mitigate BECs and also on training employees to spot the signs of phishing emails and suspicious activity,” Cavanaugh told Threatpost.
According to X-Force, businesses can take an array of security steps to avoid becoming the next victim of a BEC scam –most importantly, implementing two-factor authentication for account log-ins, making it harder for scammers to access company portals and steal credentials, said Cavanaugh.
Businesses can also create banners identifying emails that are coming from external email addresses, so that employees can instantly see if an email has been spoofed; and implement strict international wire transfer policies, so employees involved in financial transactions can be appropriately trained about identifying and preventing BEC scams.