A new strain of banking malware, Beta Bot, has been refined over the last few months to target ecommerce and comes complete with an array of features to help prevent it from being caught by usual security measures.
According to research conducted by RSA Security’s Limor Kessem, the bot started out in January as an HTTP bot and then made the gradual transition to a banking Trojan. Kessem, who’s part of RSA’s Cybercrime and Online Fraud Communications’ division, said Beta Bot has many attack vectors.
The malware has been seen targeting everything from large financial institutions to social networking sites, along with “payment platforms, online retailers, gaming platforms, webmail providers, FTP and file-sharing user credentials … domain registrars for the common malware use of registering new resources,” Kessem said.
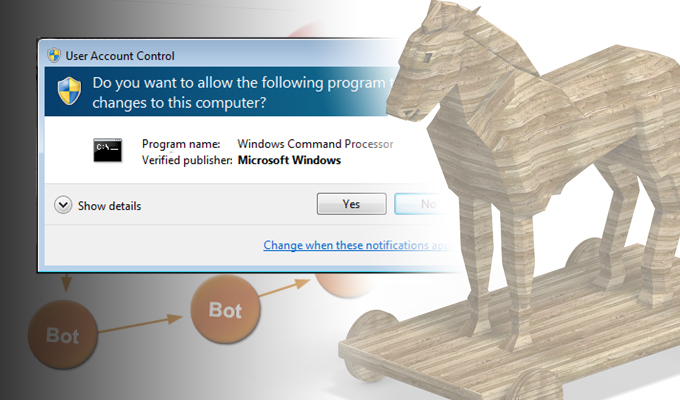
Interestingly enough, the bot is deployed on machines after a user clicks through and allows it. Once it’s in though, the malware has an array of self-defense mechanisms.
Users whose machines are infected by the malware will find themselves unable to reach whatever antivirus and security provider websites the attacker selects. When trying to reach one of those sites, they’ll get redirected to an IP address of the attacker’s choosing instead.
The malware knows better than executing in virtual machines and can avoid sandboxes as well, Kessem said. It can even block other types of malware from spreading on the system by “terminating their processes” and blocking code injections.
The Trojan goes on to log stolen data in a MySQL database, download malicious files, remotely control the infected PC and trick users into making fake banking transactions.
Kessem spoke with Beta Bot’s developer who claims he is selling binaries for the malware and providing technical support but doesn’t plan to sell the builder, opting instead to keep it private. Builds can be purchased though for between $320 and $500 with a customized server-side control panel interface in underground online forums.
Banking Trojans are continuing to grow more sophisticated in order to stay ahead of curve of advanced detection methods. Last month it was reported that Shylock, the credential-swiping Trojan that relies mainly on man-in-the-browser attacks had begun to weed out less profitable banks and updated its infrastructure to avoid downtime. Developers behind the ubiquitous Zeus Trojan were also found in April peddling tweaked versions of the malware, complete with customized botnet panels, via social networks like Facebook.