A new variant of Citadel malware is making the rounds that is targeting Payza, a money transfer service popular all over the world, especially in developing nations that are under-serviced when it comes to accessing the Internet.
The payment processing company bills itself as “your money’s gateway to the world,” and is based in the United Kingdom but also has offices in remote, developing cities like Dhaka, Bangladesh, Solna, Sweden and Mumbai, India.
According to a blog post today by Trusteer’s Etay Maor, this particular malware strain contains a Payza-specific “Man in the Browser” line of code that targets two URLS: https://secure[.]payza.com/login and https://www.alertpay[.]com. AlertPay is a Canadian payment processor that’s now a subsidiary of Payza after being purchased by the company in May 2012.
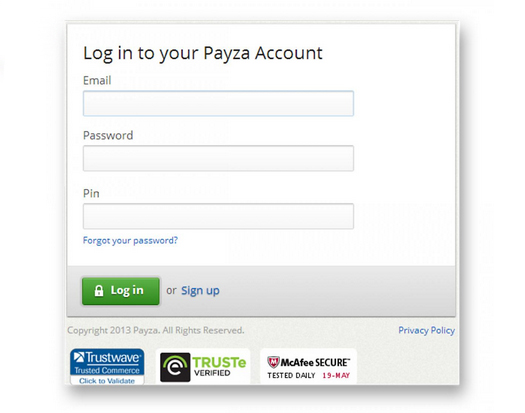
Once the malware catches someone trying to go to one of those sites, it alters the log-in fields to try and trick users into entering their banking PINs, in addition to their normal email and password credentials.
If an attacker were to get a user’s PIN, they could easily gain access to their funds – make withdrawals, deposits or make payments.
McAfee noticed an increase in Citadel malware-fueled attacks earlier this year, especially in European countries like Poland, Denmark and Sweden where it was spotted attacking government offices.
Once thought of as in decline, at least in the United States, McAfee noticed 300 Citadel samples in Europe, according to a report in February (.PDF). The firm noticed a trend: That more and more attackers are beginning to use the malware to attack business and government agencies.