Once upon a time, only big organizations worried about Advanced Persistent Threats. But it soon became obvious that every organization could find itself under fire, regardless of size or industry, and whether as direct targets or collateral damage. Most security decision makers in these organizations are aware of the importance of protecting against APTs. Yet they find it challenging to map potential APT attack vectors, which is integral in selecting the right security solutions for the organization.
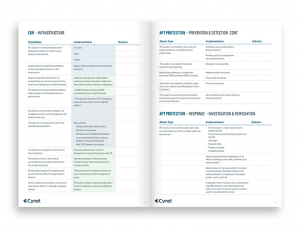
In the effort to fill this knowledge gap, Cynet has released the definitive RFP templates for EDR/EPP and APT protection. These RFPs clearly lay out the requirements for securing potential APT vectors, allowing security decision makers to quickly and accurately evaluate the products they are considering.
These templates will provide organizations with a widest-common-denominator approach to meeting the security needs and save on time and resources that would usually be spent in creating and assessing such a requirement list from scratch.
One of the big challenges in securing against APT attacks is, as the name implies, these attacks are persistent, attacking multiple vectors until successful compromise is achieved. In order to secure against these attacks, a certain level of knowledge is required regarding attack surfaces and vectors commonly used by hackers to achieve their goals.
“Think of a ninja warrior,” explains Eyal Gruner, co-founder of Cynet. “He uses every weapon at his disposal to get to the vulnerable point, well, it’s the same with a hacker – they use every tool at hand attacking endpoints, VPN credentials, networking misconfigurations, insecure DMZ architecture – anything and everything – until they get in. Together with this, there are common attack vectors, where attackers know it will be easier to get in, and using this common knowledge, we can create an attack vector map and plan for better security.”
This map is integral on the backend of any cybersecurity purchase, and would show its value by preventing cyber damage due to attempted attacks. Unfortunately, many security decision makers lack the “attacker mindset” which enables them to accurately prioritize and effectively implement the capabilities necessary in an organization’s cybersecurity solutions.
Cynet’s RFP templates are a free resource being provided to organizations to provide then with protection against advanced threats.
Explained Gruner, “After years of experience in offensive security and attack research, we asked ourselves – if we were the attackers, what types of security would have been successful in deterring us to such a degree that we might have turned our attention to an easier target?” Gruner described it as a “fascinating” exercise that brought the Cynet team to important realizations regarding the plusses and minuses of a wide swatch of attack tools and the most effective protections against them.
It is this knowledge which the typical buyer lacks, and which Cynet now provides in its RFP templates – as Gruner noted, “no one expects the security decision maker to master the attackers’ best practices book. That’s what we are here for.”
At the same time, Gruner also noted that the security decision makers know better than anyone the cost of not having effective security in place, and are well aware of what is at stake. Gruner said he expects the RFP templates to be a game-changer when it comes to enabling educated security purchase decisions, as he said, “putting control and the ability to make the right decisions in the hands of the purchasers.”
The RFP templates cover 5 areas of focus, as defined by Cynet:
- Monitoring & Control – routine activities to gain visibility and proactively discover and reduce attack surfaces.
- Prevention & Detection – mechanisms to thwart the array of commodity and advanced attack vectors.
- Investigation & Response – overall toolset for efficient reaction to detected live attacks.
- Infrastructure (EDR only) – architecture, deployment, data collection and communications.
- Operations – ongoing management of the solution.
“I assume most every organization has bought a hyped solution, only to be disappointed by its performance,” said Gruner. “Maybe it looked great when it was demoed, but in real-life it didn’t stop the threats, or it gave up a bunch of false alerts. We created this RFP guide with the express purpose of giving accurate, real-life value to the security decision makers, while preventing these situations.”
Download the Definitive EDR/EPP and APT Protection RFP Templates here.