The Nocturnal Stealer malware has crept into the Dark Web like a thief in the night, offering criminals a lucrative payday for a small price — and little effort.
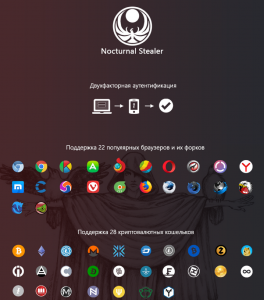
It’s a commodity malware, debuting on an underground forum in March for the low price of $25. It steals things, including 28 different kinds of cryptocurrency wallets, saved FTP passwords within FileZilla, and Chrome and Firefox browser information (such as login credentials, cookies, web data, autofill data and stored credit cards). It also zips up system data, including IP address and language, machine ID, date/time, installation location, operating system, architecture, username, processor type, video card info and a list of all running processes, to send to the C2 server.
According to Proofpoint researchers, Nocturnal Stealer’s detection evasion techniques set it apart from other budget-ware.
“[It] uses several anti-[virtual machine] and anti-analysis techniques, which include but are not limited to: environment fingerprinting, checking for debuggers and analyzers, searching for known virtual machine registry keys and checking for emulation software,” they explained in an analysis published Wednesday. “We commonly observe this step in some mainstream crimeware, but it is unusual for [this class of malware].”
In the wild, Nocturnal Stealer was seen copying stolen information into plaintext files with the obvious names “information” and “passwords”. The system data goes into the former, and the browser, cryptocurrency and FTP data goes into the latter. After that, it cranks up the communication with the C2 server, sending the stolen info in a multi-part HTTP POST form.
“It [also] utilizes an HTTP POST method for the initial check-in to report the infected machine information to the C&C server,” the researchers said. “This POST uses the User-Agent ‘Nocturnal/1.0’ which contains the name and the version of the stealer. This may indicate that this is the first major version of this Nocturnal Stealer to be observed in the wild.”
When its nefarious work is done, it runs a simple command to end its processes and delete itself off the victim machine – it is, in other words, a “one-shot” code, and the victim may be completely unaware that his or her information has been lifted.
Proofpoint researchers noted that while Nocturnal Stealer is a fairly simple weapon, it “provides a glimpse into the evolving criminal markets that continue to produce new variations on the crimeware we see every day.” Specifically, it gives wings to the trend of entry-level cybercriminals gaining the ability to carry out advanced attacks, in this case to harvest and exfiltrate sensitive data. The Dark Web ad hawks Nocturnal Stealer’s anonymity, and offers server setup services (incidentally a savvy technique that gives the malware authors access to all stolen data lifted by their clients).
“Nocturnal Stealer and other malware like it provide a would-be cybercriminal with the means to cause damage and harm to people and companies easily and cheaply,” the researchers said, something that should be a real concern for defenders.