Google has ejected 50 apps from its Google Play store that were harboring mobile malware dubbed ExpensiveWall. The malware, which was downloaded between 1 million to 4.2 million times, sends fraudulent premium SMS messages for fake fee-based services without the knowledge or permission of users, according to Check Point security researchers.
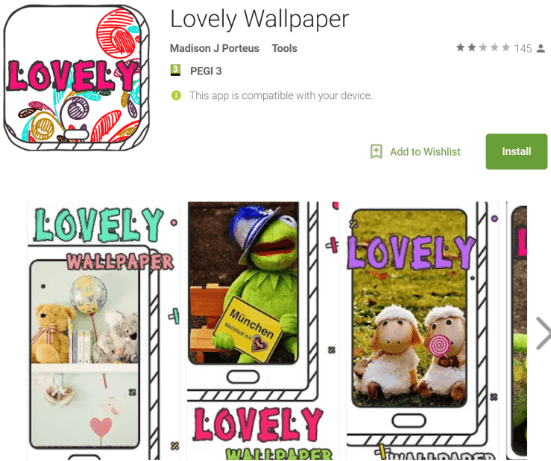
Researchers said the malware was bundled predominantly in the Android wallpaper app called Lovely Wallpaper.
“ExpensiveWall is a new variant of malware found earlier this year on Google Play. The entire malware family has now been downloaded between 5.9 million and 21.1 million times,” wrote Check Point researchers Elena Root, Andrey Polkovnichenko and Bohdan Melnykov in a technical description posted Thursday.
This latest strain sets itself apart from a previous versions of the malware because of the use of the advanced obfuscation technique called “packed“, which compresses malicious programs and encrypts them in order to avoid detection.
Google was notified of the malware-tainted apps on Aug. 7 and removed them. However, the malware reemerged on Google Play days later on a new unidentified app, according to researchers. More than 5,000 additional devices were infected before it was removed four days later, Check Point said.
While this latest infiltration impacted an estimated 50 apps, Google Play has been battling rogue apps for the entire year. Four messaging apps in the Google Play store containing spyware called SonicSpy were removed last month. In May, malware called Judy was downloaded 36 million times and found in 40 apps. On at least four separate occasions this year Google has had to give malware the boot from Google Play. That malware included Dvmap, SMSVova, Ztorg and also 132 apps infected with malicious iFrames.
Researchers said it’s unclear how much revenue has been generated via ExpensiveWall’s premium SMS scam.
“It’s important to point out that any infected app installed before it was removed from the App store, still remains installed on users’ devices. Users who downloaded these apps are therefore still at risk and should manually remove them from their devices,” Check Point said.
Once an app with the malware ExpensiveWall is installed it requests several device permissions including internet access – allowing apps to connect to its C&C server – and SMS permissions to register users for paid services and sending premium SMS messages without the users’ knowledge, researchers said. The firm suggests the apps may have also been able to sneak past Google Play security measures because the permissions required for the scam were not unusual and used for appropriate purposes by legitimate apps.
“ExpensiveWall contains an interface that connects between in-app actions and the JavaScript code, which runs on a web interface called WebView, meaning JavaScript running inside the WebView can trigger in-app activities. After it is installed and granted the necessary permissions, ExpensiveWall sends data about the infected device to its C&C server, including its location and unique identifiers, such as MAC and IP addresses, IMSI, and IMEI,” researchers wrote.
When a user turned on their Android smartphone or switched connectivity preferences, the malware connected to its C&C server and received a URL. The URL “opens in an embedded WebView. This page contains a malicious JavaScript code that can invoke in-app functions using JavascriptInterface, like subscribing them to premium services and sending SMS messages,” they said.
Researchers are warning developers that ExpensiveWall is likely spread to different apps via an SDK called “GTK.”