A new information stealer, dubbed Raccoon, is rapidly gaining popularity with cybercriminals. In just a few months, researchers say the malware has already infected hundreds of thousands of devices across the world to rove through victims’ credit card data, email credentials and more.
The malware is not overly sophisticated or innovative, but its malware-as-a-service (MaaS) model gives cybercriminals a quick-and-easy way to make money stealing sensitive data.
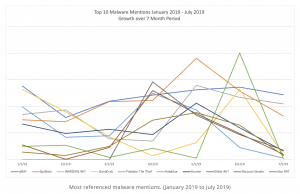
In fact, researchers say that despite only emerging a few months ago, Raccoon is already one of the top 10 most-mentioned malwares in the underground economy right now.
“Based on the logs for sale in the underground community, Raccoon is estimated to have infected over 100,000 endpoints worldwide within a few months,” said researchers with Cybereason in a Thursday analysis. “It is easy to operate for technical and nontechnical individuals alike, lending it mass appeal. Moreover, the team behind Raccoon is constantly working to improve it and provide responsive service. It gives individuals a quick-and-easy way to make money stealing sensitive data without investing a lot of funds or having a deep technical background.”
Infostealer
Researcher first spotted Raccoon in April 2019. The malware, written in C++, leverages several potential delivery methods. These include exploit kits (including Fallout and RIG), as well as phishing attacks and bundled malware (malware that is bundled with legitimate software downloaded from “shady” websites).
 Once installed, Raccoon scours systems for credit card information, cryptocurrency wallets, passwords, emails, cookies, system information and data from popular browsers (including saved credit-card info, URLs, usernames and passwords), and then sends that data back to its operator.
Once installed, Raccoon scours systems for credit card information, cryptocurrency wallets, passwords, emails, cookies, system information and data from popular browsers (including saved credit-card info, URLs, usernames and passwords), and then sends that data back to its operator.
The stealer is developed by a team that appears to originate in Russia and is Russian speaking, researchers said. The stealer was originally sold in exclusively Russian speaking hacking forums, but now has spread to English-speaking forums as well.
“Despite being released earlier this year, the Raccoon stealer is exploding in popularity in the underground community to become one of the top 10 most-referenced malware on the market in 2019, infecting hundreds of thousands of endpoints globally across organizations and individuals in North America, Europe and Asia,” researchers said.
Popularity Explosion
The Raccoon malware’s immense explosion of popularity is attributed to a variety of reasons. As a MaaS offering, it costs $200 per month to use, building in features like an automated backend panel, hosting and customer support.
In addition, feedback around Raccoon in the underground community is generally positive. While many in underground forums believe that while the malware lacks in features and sophistication (for instance, current versions of Raccoon do not have keylogging functionality), it largely makes up for it with consistency and an impressive level of service, support and quality user experience, they say.
“Many in the community praise and endorse Raccoon’s malware capabilities and the services the team provides,” researchers said. “Some voices in the community even endorse it as a worthy replacement for the famous Azorult stealer.”
Raccoon is still under active development, but researchers say that “its popularity, even with a limited feature set, signals the continuation of a growing trend of the commoditization of malware as they follow a MaaS model and evolve their efforts.”